Evolution of Computer Virus Concealment and Anti-Virus Techniques: A Short Survey
This paper presents a general overview on evolution of concealment methods in computer viruses and defensive techniques employed by anti-virus products. In order to stay far from the anti-virus scanners, computer viruses gradually improve their codes to make them invisible. On the other hand, anti-virus technologies continually follow the virus tricks and methodologies to overcome their threats. In this process, anti-virus experts design and develop new methodologies to make them stronger, more and more, every day. The purpose of this paper is to review these methodologies and outline their strengths and weaknesses to encourage those are interested in more investigation on these areas.
💡 Research Summary
The paper provides a concise yet comprehensive survey of the co‑evolution of computer virus concealment techniques and the corresponding anti‑virus (AV) defenses. It begins by outlining the historical context: early viruses in the late 1980s were simple file‑infectors that could be detected by static signature scanners. To evade these scanners, virus authors introduced encryption, embedding a decryption routine together with a fixed key. This “encrypted virus” phase lasted until AV vendors began to target the decryption stub itself, prompting the next leap in concealment.
The authors describe the emergence of polymorphic viruses, which generate a new encryption key and a slightly altered decryption routine for each infection. Polymorphic engines may be embedded within the malware or invoked as external modules, producing a virtually unlimited set of distinct binaries while preserving the same functional payload. Because the only invariant is the decryption algorithm’s logic, traditional signature‑based detection becomes ineffective.
Metamorphic viruses represent the next evolutionary step. Rather than merely encrypting their code, metamorphic malware rewrites its own executable body. Techniques such as opcode substitution, register renaming, instruction reordering, insertion of dead code, and control‑flow graph transformation are combined to produce a program that bears no structural similarity to its predecessor. This level of mutation defeats both static signatures and many heuristic or behavior‑based detectors, as the malicious actions may appear benign until the payload is actually executed.
Beyond code mutation, the paper surveys system‑level concealment mechanisms: rootkits that hook kernel‑mode system calls to hide processes and files, file‑less malware that resides solely in memory and leverages legitimate system utilities, and virtualization‑aware code that detects sandbox or virtual machine environments through timing checks, CPU feature queries, or specific hardware identifiers. These tactics specifically target dynamic analysis environments, rendering sandbox execution and emulation less reliable.
On the defensive side, the authors trace the progression of AV technologies. Signature‑based detection, the earliest and most straightforward method, relies on exact byte patterns and quickly becomes obsolete against polymorphic and metamorphic threats. Heuristic analysis was introduced to flag suspicious code constructs or anomalous file structures, but it suffers from high false‑positive rates. Behavioral (or anomaly) detection monitors runtime activities—system calls, registry modifications, network traffic—to identify malicious intent regardless of the binary’s static appearance. While effective against file‑less and zero‑day threats, behavior‑based engines can be evaded through delayed execution, user‑interaction triggers, or by mimicking legitimate application behavior.
The paper then examines modern, data‑driven defenses. Machine‑learning and deep‑learning classifiers are trained on large corpora of benign and malicious samples to learn discriminative feature vectors. Cloud‑based scanning platforms enable rapid distribution of the latest threat intelligence, mitigating the lag inherent in local signature updates. Integrity verification mechanisms—file, memory, and kernel integrity checks—provide an additional layer of protection against rootkits and code‑injection attacks. However, the authors note that ML models are vulnerable to adversarial manipulation, suffer from dataset bias, and demand substantial computational resources.
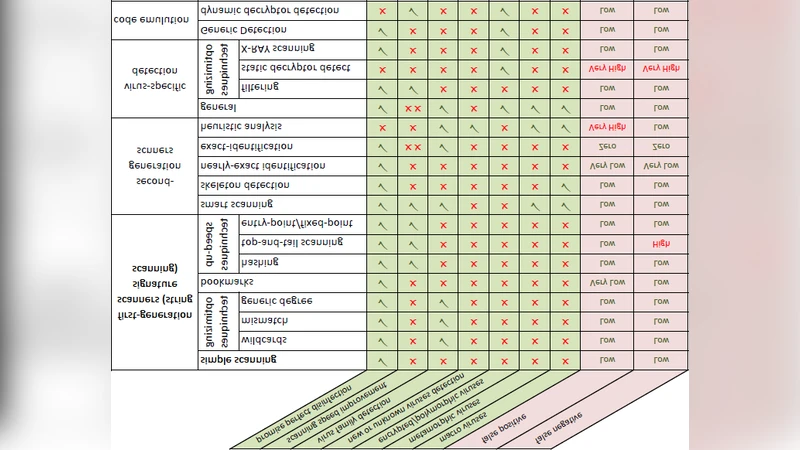
A comparative matrix summarises each concealment technique against the corresponding detection strategies, highlighting that the cost of detection grows roughly exponentially with the sophistication of the concealment. Metamorphic and file‑less malware incur the highest evasion rates, while hybrid AV solutions that combine signatures, heuristics, behavior monitoring, and ML achieve the best trade‑off between detection efficacy and performance.
In the concluding section, the authors forecast future trends. They anticipate the rise of AI‑generated, automatically mutating malware capable of learning from AV responses in real time, as well as threats targeting cloud‑native and containerized workloads where traditional endpoint AV is less applicable. To counter these developments, the paper recommends a multi‑layered defense architecture: integrating static signatures, dynamic behavior analysis, machine‑learning classifiers, and continuous threat‑intel sharing across organizations. The authors argue that only through such a holistic, adaptive approach can the security community keep pace with the ever‑advancing art of virus concealment.
Comments & Academic Discussion
Loading comments...
Leave a Comment