A Comparison of Link Layer Attacks on Wireless Sensor Networks
Wireless sensor networks (WSNs) have many potential applications [1, 5] and unique challenges. They usually consist of hundreds or thousands small sensor nodes such as MICA2, which operate autonomously; conditions such as cost, invisible deployment and many application domains, lead to small size and limited resources sensors [2]. WSNs are susceptible to many types of link layer attacks [1] and most of traditional networks security techniques are unusable on WSNs [2]; due to wireless and shared nature of communication channel, untrusted transmissions, deployment in open environments, unattended nature and limited resources [1]. So, security is a vital requirement for these networks; but we have to design a proper security mechanism that attends to WSN’s constraints and requirements. In this paper, we focus on security of WSNs, divide it (the WSNs security) into four categories and will consider them, include: an overview of WSNs, security in WSNs, the threat model on WSNs, a wide variety of WSNs’ link layer attacks and a comparison of them. This work enables us to identify the purpose and capabilities of the attackers; also, the goal and effects of the link layer attacks on WSNs are introduced. Also, this paper discusses known approaches of security detection and defensive mechanisms against the link layer attacks; this would enable it security managers to manage the link layer attacks of WSNs more effectively.
💡 Research Summary
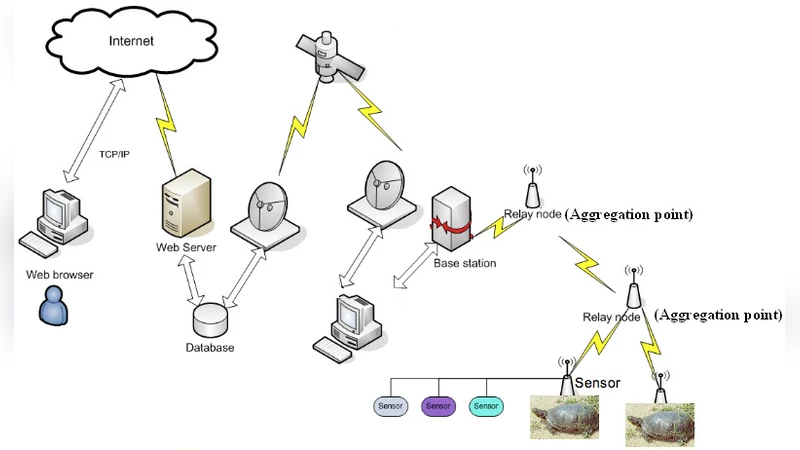
The paper “A Comparison of Link Layer Attacks on Wireless Sensor Networks” provides a comprehensive taxonomy and analysis of security threats that target the link layer of wireless sensor networks (WSNs). Beginning with an overview of WSN characteristics—such as low‑cost, low‑power sensor motes, hierarchical architecture (sensor nodes, aggregation points, base stations), and a wide range of applications (military, environmental monitoring, industrial control)—the authors highlight the inherent constraints (limited energy, processing, memory, and unreliable wireless channels) that make traditional network security mechanisms unsuitable.
The authors then outline the core security goals for WSNs (confidentiality, integrity, authentication, availability, data freshness) and enumerate the obstacles that impede their achievement, including resource scarcity, unattended deployment, and the broadcast nature of the wireless medium. They briefly review common security protocols (SNEP, µTESLA, SPIN, encrypted broadcasts) and map security threats to four high‑level security classes: interruption, interception, modification, and fabrication.
A central contribution of the paper is its multi‑dimensional threat model. Attacks are classified along three axes: (1) damage/access level (active vs. passive), (2) attacker location (internal/insider vs. external/out‑sider), and (3) attacker device class (mote‑class vs. laptop‑class). For each axis, the paper describes typical attack behaviors, objectives, and impacts. Active attackers may inject false data, impersonate nodes, or modify packets, leading to network functionality disruption, performance degradation, or node destruction. Passive attackers focus on eavesdropping and privacy violations. Insider attackers, being legitimate but compromised nodes, can steal cryptographic keys, manipulate routing, or launch selective denial‑of‑service attacks, whereas outsiders typically rely on jamming and resource exhaustion. Device class influences the attack’s power: mote‑class attackers can perform jamming or key theft using compromised sensor hardware, while laptop‑class attackers can leverage higher bandwidth and processing capability for more sophisticated attacks.
The paper proceeds to enumerate specific link‑layer attacks, including:
- Jamming – deliberate interference that blocks all communication;
- Collision – causing intentional packet collisions to force retransmissions;
- Replay – retransmitting captured frames to bypass authentication;
- Sybil – a single node assuming multiple identities to disrupt routing;
- Wormhole – tunneling packets between distant locations to create false topology;
- Selective Forwarding – dropping or altering specific packets;
- Node Capture – physical compromise of a mote to extract keys and code.
For each attack, the authors list the primary security goal violated (e.g., availability for jamming, integrity for selective forwarding), the resulting effects on the network, and possible detection and mitigation techniques. Detection mechanisms discussed include MAC‑layer authentication codes, intrusion detection systems (IDS) that monitor traffic anomalies, and time‑synchronization checks to prevent replay. Defensive strategies comprise multi‑path routing to increase resilience, periodic key renewal (as in µTESLA), power‑control based anti‑jamming, secure broadcast authentication, and secure aggregation protocols.
The authors conclude that their taxonomy enables security managers to systematically identify attacker capabilities, objectives, and suitable countermeasures. However, the paper acknowledges several limitations: the analysis is largely theoretical, lacking experimental validation; the survey does not cover newer lightweight cryptographic schemes, blockchain‑based key management, or machine‑learning‑driven anomaly detection that have emerged after 2011; and the discussion of attack inter‑dependencies (e.g., combined jamming and replay) is minimal.
Overall, the paper serves as a solid introductory reference for understanding link‑layer vulnerabilities in WSNs and provides a structured framework for classifying attacks and selecting appropriate defenses. For practitioners working on modern IoT deployments, the taxonomy remains useful, but it should be supplemented with recent advances in low‑power security primitives, real‑world test‑bed evaluations, and integration with higher‑layer security architectures.
Comments & Academic Discussion
Loading comments...
Leave a Comment