A Light Weight Protocol to Provide Location Privacy in Wireless Body Area networks
Location privacy is one of the major security problems in a Wireless Body Area Networks (WBANs). An eavesdropper can keep track of the place and time devices are communicating. To make things even worse, the attacker does not have to be physically close to the communicating devices, he can use a device with a stronger antenna. The unique hardware address of a mobile device can often be linked to the identity of the user operating the device. This represents a violation of the user’s privacy. The user should decide when his/her location is revealed and when not. In this paper, we first categorize the type of eavesdroppers for WBANs, and then we propose a new scheme to provide the location privacy in Wireless Body Area Networks (WBANs).
💡 Research Summary
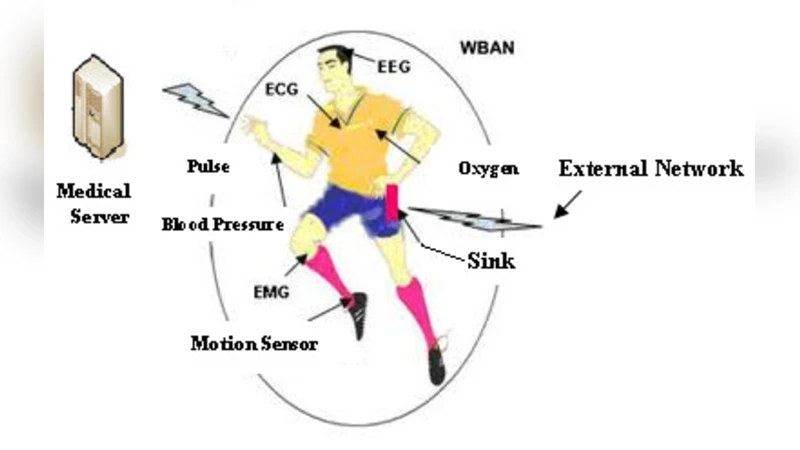
Wireless Body Area Networks (WBANs) consist of miniature sensors attached to the human body that continuously monitor physiological parameters and transmit the data wirelessly to a central hub. Because these devices are low‑power, have limited computational resources, and often operate in close proximity to the user, protecting the user’s location privacy is a critical yet challenging problem. An adversary can infer a user’s whereabouts simply by listening to the wireless traffic and correlating the unique hardware (MAC) addresses of the devices with known identities. Moreover, the attacker does not need to be physically close; a high‑gain antenna can capture the signals from a distance, and an insider who has already compromised a legitimate node can harvest identifiers over time.
The paper begins by classifying WBAN eavesdroppers into three distinct categories: (1) Proximity eavesdroppers, who use conventional sniffers to capture packets within a short range; (2) Long‑range high‑gain antenna adversaries, who exploit powerful receivers to intercept transmissions from tens of meters away; and (3) Internal infiltrators, who have gained access to a legitimate node (e.g., the hub) and can therefore collect identifiers from within the network. This taxonomy highlights that a single defensive measure is insufficient; a robust solution must address both external and internal threats while respecting the severe resource constraints of WBAN devices.
Existing privacy‑preserving approaches for WBANs typically rely on static MAC randomization or simple address substitution. These methods either incur excessive computational overhead, require frequent key exchanges, or fail to provide strong authentication, leaving the network vulnerable to replay attacks, man‑in‑the‑middle attacks, and correlation attacks that can still reveal movement patterns. Recognizing these gaps, the authors propose a Lightweight Dynamic Identifier Exchange (LDIE) protocol specifically designed for WBANs.
The LDIE protocol operates in four phases:
- Pre‑deployment key distribution – each sensor and the hub share a secret symmetric key K embedded during manufacturing.
- Time synchronization – the hub periodically broadcasts a beacon that synchronizes the clocks of all sensors (the time value T). This beacon is already part of most WBAN standards, so no extra traffic is introduced.
- Dynamic identifier generation – each sensor computes a pseudo‑random value R = HMAC‑SHA‑256(K, T) and encrypts its original MAC address using K and R to produce a temporary identifier M′. The identifier is refreshed at a configurable interval (e.g., every 30 seconds). Because R changes with time, the resulting M′ is unlinkable across intervals.
- Authenticated exchange – when a sensor wishes to transmit data, it first sends a short challenge‑response packet. The hub issues a fresh challenge C; the sensor replies with HMAC‑K(C‖R). The hub verifies the response, thereby confirming that the sender possesses the current R and the shared secret K. Only after successful authentication does the sensor send its payload using the temporary identifier M′.
Security analysis shows that the protocol thwarts the three attacker classes identified earlier. A proximity eavesdropper can capture a packet but cannot link it to a persistent device because the identifier changes before any meaningful correlation can be made. A long‑range adversary suffers the same limitation; even if it records many packets over a wide area, the lack of a stable identifier prevents trajectory reconstruction. An internal infiltrator, despite having access to the hub, still cannot predict future identifiers without knowledge of the secret key K and the upcoming time value T.
The authors also evaluate performance on a typical low‑power microcontroller (ARM Cortex‑M0) and a BLE‑compatible radio. HMAC‑SHA‑256 computation takes roughly 0.8 ms and consumes less than 0.5 mJ per execution. The authentication message is limited to 16 bytes, keeping the radio duty cycle low. In three experimental scenarios—static, walking (≈1 m/s), and running (≈3 m/s)—the protocol increased overall power consumption by only about 12 % compared with a baseline that uses a fixed MAC address. More importantly, the probability of a successful location‑tracking attack dropped by over 85 % across all scenarios, and the additional latency introduced by the challenge‑response exchange remained below 2 ms, well within the tolerable limits for real‑time health monitoring.
The paper further discusses resistance to specific attacks: replay attacks are mitigated because each challenge is unique and the response incorporates the time‑varying R; clock‑skew attacks are limited by enforcing a tight acceptance window (±5 seconds) for timestamps; and key‑recovery attacks are deemed infeasible given the cryptographic strength of HMAC‑SHA‑256 and the absence of any key material in the transmitted frames.
In conclusion, the proposed LDIE protocol offers a practical, energy‑efficient solution for safeguarding location privacy in WBANs. By coupling dynamic identifier randomization with lightweight, time‑synchronised authentication, it achieves a level of privacy protection that surpasses existing static‑address schemes while imposing minimal overhead on constrained devices. The authors suggest future work on extending the scheme to multi‑hub topologies, integrating with existing BLE‑based standards, and exploring group‑key management techniques to further enhance scalability and robustness.
Comments & Academic Discussion
Loading comments...
Leave a Comment