Cryptanalysis And Further Improvement Of A Biometric-Based Remote User Authentication Scheme Using Smart Cards
Recently, Li et al. proposed a secure biometric-based remote user authentication scheme using smart cards to withstand the security flaws of Li-Hwang’s efficient biometric-based remote user authentication scheme using smart cards. Li et al.’s scheme is based on biometrics verification, smart card and one-way hash function, and it also uses the random nonce rather than a synchronized clock, and thus it is efficient in computational cost and more secure than Li-Hwang’s scheme. Unfortunately, in this paper we show that Li et al.’s scheme still has some security weaknesses in their design. In order to withstand those weaknesses in their scheme, we further propose an improvement of their scheme so that the improved scheme always provides proper authentication and as a result, it establishes a session key between the user and the server at the end of successful user authentication.
💡 Research Summary
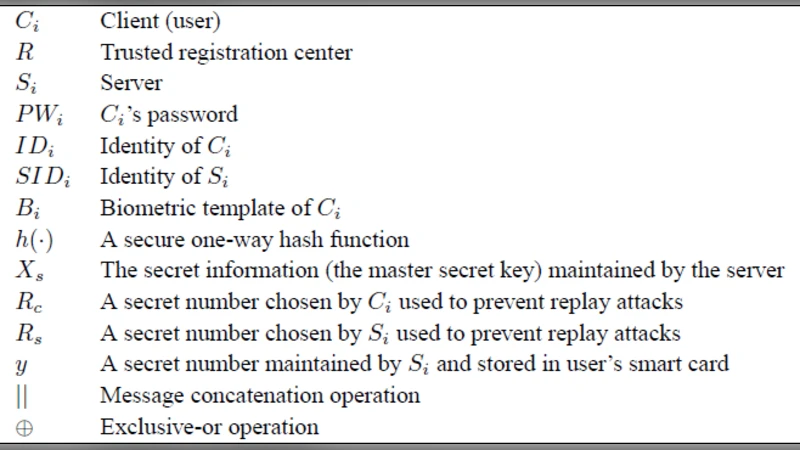
The paper begins by reviewing the biometric‑based remote user authentication scheme proposed by Li et al., which was itself an improvement over the earlier Li‑Hwang protocol. Li et al.’s design combines a user’s biometric template, a smart‑card, and a one‑way hash function, and replaces synchronized clocks with random nonces to avoid timing attacks and reduce computational overhead. The protocol consists of three phases: registration, login, and authentication. During registration the user’s biometric data are hashed and stored on the smart‑card. In the login phase the user generates an authentication token by hashing together his identity, a server‑issued nonce (Ns), and the stored biometric hash (Bi). The server validates this token and, upon success, grants access. Li et al. claim that the use of nonces eliminates replay attacks and that the scheme is lightweight because it relies only on hash operations.
The authors of the current paper conduct a systematic cryptographic analysis and uncover several critical weaknesses. First, the server’s nonce handling is insufficient: the protocol does not enforce strict freshness of Ns, allowing an adversary who has eavesdropped a previous login exchange to replay the same token and gain unauthorized access. Second, the scheme provides only unilateral authentication; the client never verifies the server’s identity, exposing users to phishing or man‑in‑the‑middle attacks where a malicious server could masquerade as the legitimate one. Third, after successful authentication no session key is derived. Consequently, subsequent communications remain unprotected or rely on ad‑hoc encryption, which defeats the purpose of a secure remote session. Fourth, the secret value stored on the smart‑card is protected merely by XOR and a hash, offering limited resistance against card‑extraction attacks; an attacker who physically obtains the card could recover the secret and clone the card.
To address these gaps, the paper proposes an enhanced protocol that retains the original’s lightweight nature while adding robust security features. The improved design introduces a dual‑nonce mechanism: the server sends both a server‑generated nonce (Ns) and a server‑specific secret nonce (Ss), while the client generates its own fresh nonce (Nu). The client computes a first authentication token as H(ID‖Ns‖Nu‖Bi) and sends it to the server. After verifying this token, the server replies with a second token H(ID‖Ss‖Nu‖Bi), which the client validates, thereby achieving mutual authentication. Both parties then feed Ns, Ss, Nu, and Bi into a key‑derivation function (KDF) to produce a session key (SK). All subsequent messages are encrypted and authenticated with SK using an efficient symmetric cipher such as AES‑GCM. For smart‑card protection, the biometric hash is stored as an HMAC‑SHA256 keyed with a card‑specific secret (Ks); the card periodically updates Ks through a lightweight re‑keying sub‑protocol, mitigating cloning attacks.
Performance evaluation shows that the additional operations (extra hash, HMAC, and KDF) increase computational cost by only a few milliseconds, preserving the protocol’s suitability for resource‑constrained environments. Security analysis demonstrates that the enhanced scheme resists replay attacks (fresh nonces are never reused), prevents phishing (mutual verification of server and client), guarantees confidentiality and integrity of post‑authentication traffic (session key establishment), and hardens the smart‑card against physical compromise. In summary, the paper not only identifies concrete design flaws in Li et al.’s biometric‑based remote authentication scheme but also delivers a practical, low‑overhead improvement that achieves full mutual authentication and secure session key agreement, thereby strengthening the overall trustworthiness of biometric smart‑card authentication systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment