Mitigation of Malicious Attacks on Networks
Terrorist attacks on transportation networks have traumatized modern societies. With a single blast, it has become possible to paralyze airline traffic, electric power supply, ground transportation or Internet communication. How and at which cost can one restructure the network such that it will become more robust against a malicious attack? We introduce a unique measure for robustness and use it to devise a method to mitigate economically and efficiently this risk. We demonstrate its efficiency on the European electricity system and on the Internet as well as on complex networks models. We show that with small changes in the network structure (low cost) the robustness of diverse networks can be improved dramatically while their functionality remains unchanged. Our results are useful not only for improving significantly with low cost the robustness of existing infrastructures but also for designing economically robust network systems.
💡 Research Summary
The paper addresses the pressing problem of how to make critical infrastructure networks—such as power grids, transportation systems, and the Internet—more resilient to deliberate, targeted attacks. While previous studies have shown that highly interconnected networks are robust against random failures, they are extremely vulnerable when an adversary removes the most connected nodes. The authors argue that the traditional robustness metric, the percolation threshold qc (the fraction of removed nodes that completely fragments the network), is insufficient because it ignores substantial degradation that occurs well before total collapse.
To overcome this limitation, the authors introduce a new robustness measure R, defined as the average size of the largest connected component over all possible attack fractions q. Formally, R = (1/N) ∑_{Q=1}^{N} s(Q), where s(Q) is the fraction of nodes remaining in the largest component after removing Q = qN nodes. This metric ranges from 1/N (for a star network) to 0.5 (for a fully connected graph) and allows direct comparison across networks of different sizes.
Improving R in real systems, however, must respect practical constraints: (i) the degree of each node (i.e., the number of incident links) should stay unchanged, (ii) the total geographic length of all links must not increase, and (iii) the total number of links must remain constant. Under these constraints, the authors devise an edge‑swap algorithm. Two edges e_{ij} and e_{kl} are selected at random; they are rewired to e_{ik} and e_{jl} provided that the new configuration yields a higher R than the original. The process repeats until a large number of consecutive swaps fail to produce a significant improvement.
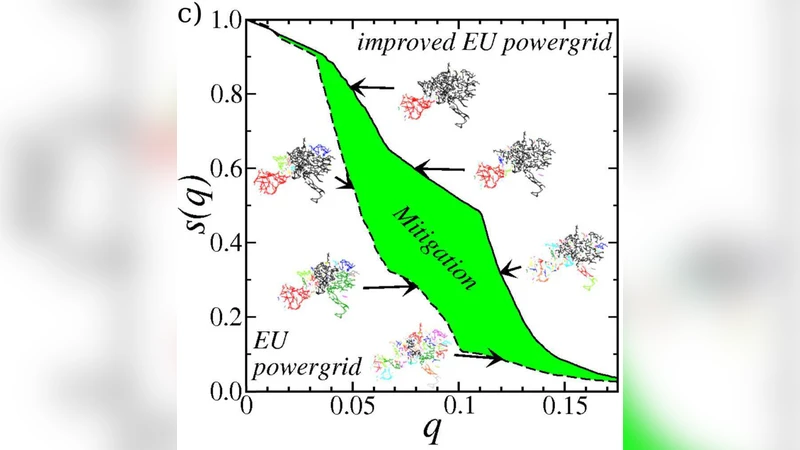
The method is first applied to two real‑world infrastructures. In the European power grid (N = 1254 nodes, M = 1811 lines) and the global Internet Point‑of‑Presence (PoP) network (N = 1098, M = 6089), swapping only about 5 % of the existing links raises R by 45 % and 55 % respectively. Notably, the percolation threshold qc remains essentially unchanged, confirming that the new metric captures robustness improvements missed by qc. Moreover, the conductance distribution—an indicator of transport efficiency—remains virtually identical before and after the rewiring, demonstrating that functionality is preserved while robustness increases.
Next, the authors explore whether the same algorithm can be used to design robust synthetic networks from scratch. They test scale‑free graphs with degree exponents γ = 2.5 and 3, as well as Erdős‑Rényi graphs with average degrees ⟨k⟩ = 3.5 and 4. In all cases, systematic edge swaps dramatically increase R, and the resulting topologies share a distinctive “onion‑like” structure: a densely connected core of high‑degree nodes surrounded by concentric shells of nodes with decreasing degree. To quantify this, they compute S_k, the fraction of nodes of degree k that are connected through paths that never pass through nodes of higher degree. High S_k values across degrees confirm that the onion architecture promotes alternative routes that avoid over‑reliance on a few hubs. The onion networks also prove robust against alternative attack strategies, such as removal of high‑betweenness nodes.
Interestingly, the optimization slightly lengthens the average shortest‑path length and the network diameter, but both grow only logarithmically with system size, indicating that the trade‑off between robustness and efficiency is modest. Because the algorithm only rewires existing edges, the approach is cost‑effective: no new physical links need to be built, and total cable length does not increase, making it directly applicable to existing infrastructures.
In summary, the paper makes three major contributions: (1) a comprehensive robustness metric R that captures degradation throughout the attack process; (2) a low‑cost, constraint‑aware edge‑swap algorithm that can substantially improve R in real networks; and (3) the identification of an onion‑like topology as a universal hallmark of maximally robust networks for a given degree distribution. These findings provide actionable guidance for upgrading current power and communication systems and offer a principled design paradigm for future critical infrastructures that must withstand malicious, targeted disruptions.
Comments & Academic Discussion
Loading comments...
Leave a Comment