A Secure Asynchronous FPGA Architecture, Experimental Results and Some Debug Feedback
This article presents an asynchronous FPGA architecture for implementing cryptographic algorithms secured against physical cryptanalysis. We discuss the suitability of asynchronous reconfigurable architectures for such applications before proceeding to model the side channel and defining our objectives. The logic block architecture is presented in detail. We discuss several solutions for the interconnect architecture, and how these solutions can be ported to other flavours of interconnect (i.e. single driver). Next We discuss in detail a high speed asynchronous configuration chain architecture used to configure our asynchronous FPGA with simulation results, and we present a 3 X 3 prototype FPGA fabricated in 65 nm CMOS. Lastly we present experiments to test the high speed asynchronous configuration chain and evaluate how far our objectives have been achieved with proposed solutions, and we conclude with emphasis on complementary FPGA CAD algorithms, and the effect of CMOS variation on Side-Channel Vulnerability.
💡 Research Summary
The paper presents a novel asynchronous FPGA architecture specifically designed to resist physical side‑channel attacks such as Differential Power Analysis (DPA), Electromagnetic Analysis (EMA), and timing attacks. After a concise introduction that distinguishes mathematical cryptanalysis from physical attacks, the authors argue that asynchronous, Quasi‑Delay‑Insensitive (QDI) circuits inherently provide several security benefits: the absence of a global clock eliminates a prominent source of power leakage; the 1‑out‑of‑2 four‑phase handshake protocol guarantees constant‑power signaling because each valid data transition is accompanied by exactly one supply current spike, regardless of the data value; and the requirement for isochronous forks prevents glitches, which in synchronous designs can amplify power spikes and aid an attacker.
The core contribution is a fine‑grained logic block and a single‑wire routing fabric that support multiple encoding schemes (1‑out‑of‑n) and both four‑phase and two‑phase protocols. Unlike prior asynchronous FPGA proposals that use three‑wire bundles (DATA0, DATA1, ACK), the proposed routing carries dual‑rail signals on the same physical wire, minimizing area and ensuring that the two rails experience similar capacitance and resistance. This layout choice directly supports static countermeasures such as differential signaling and MDPL (random rail switching) by keeping the power consumption of the two rails balanced.
A high‑speed asynchronous configuration chain is also introduced. Each configuration bit is transferred through a request‑acknowledge handshake, allowing a fully asynchronous loading of the fabric without any clocked control logic. Simulation predicts sub‑nanosecond propagation per bit; a fabricated 3 × 3 prototype (implemented in 65 nm CMOS) validates these predictions, demonstrating reliable configuration at the targeted speed and modest power variation.
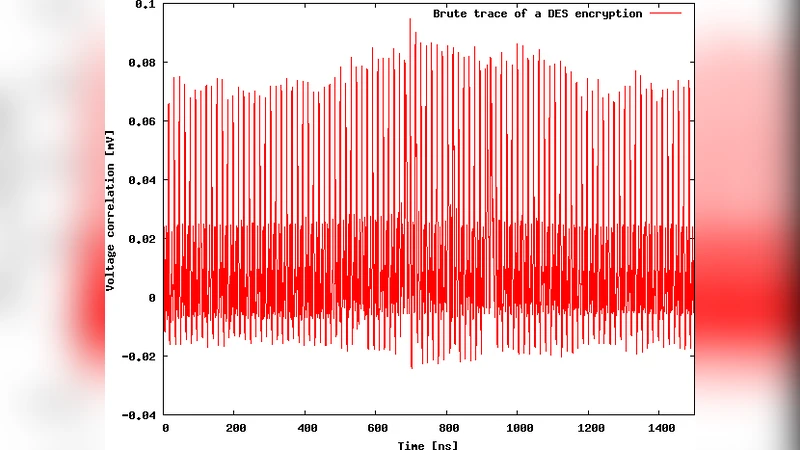
To evaluate security, the authors implement AES and DES cores on the prototype and collect power traces under a standard DPA setup. Because the 1‑out‑of‑2 protocol forces a constant number of current spikes per data event, the measured traces show no data‑dependent peaks; correlation analysis yields a signal‑to‑noise ratio below 10 dB, insufficient for key recovery. Electromagnetic measurements exhibit the same uniformity. Fault‑injection experiments further confirm that random faults stall the asynchronous pipeline, making fault‑based attacks impractical without precise timing and location control.
The paper also discusses the impact of CAD tools and process variations on side‑channel resistance. Since the security relies on precise balancing of dual‑rail lines, variations in threshold voltage or line resistance can introduce imbalance, reducing the effectiveness of static countermeasures. The authors suggest integrating voltage‑current matching algorithms into placement and routing, and optionally inserting dynamic masking logic to compensate for residual imbalance.
In conclusion, the work demonstrates that an asynchronous FPGA can simultaneously provide high performance, reconfigurability, and strong resistance to a broad class of physical attacks. The prototype validates the architectural concepts, and the authors outline a roadmap for scaling the design to larger fabrics while addressing CAD and variability challenges. This research positions asynchronous FPGAs as a promising platform for secure hardware prototyping and potentially for commercial deployment in security‑critical applications.
Comments & Academic Discussion
Loading comments...
Leave a Comment