Hiding Secret Information in Movie Clip: A Steganographic Approach
Establishing hidden communication is an important subject of discussion that has gained increasing importance nowadays with the development of the internet. One of the key methods for establishing hidden communication is steganography. Modern day steganography mainly deals with hiding information within files like image, text, html, binary files etc. These file contains small irrelevant information that can be substituted for small secret data. To store a high capacity secret data these carrier files are not very supportive. To overcome the problem of storing the high capacity secret data with the utmost security fence, we have proposed a novel methodology for concealing a voluminous data with high levels of security wall by using movie clip as a carrier file.
💡 Research Summary
The paper addresses the growing need for covert communication in the age of the Internet and proposes a novel steganographic scheme that uses digital movie clips as the carrier medium. Traditional steganographic approaches have largely focused on images, text, HTML, or binary files, which provide limited embedding capacity. By exploiting the massive data volume inherent in video streams—typically 30 frames per second, each frame containing millions of pixels—the authors argue that a movie clip can serve as an “unbounded” carrier capable of hiding gigabytes of secret information.
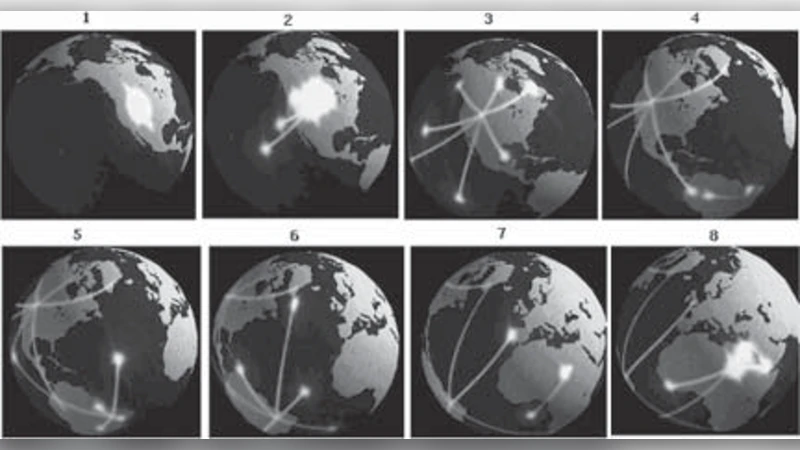
The work is organized into three main phases. In Phase‑I, the secret payload is first analyzed to determine its size, after which an appropriately sized movie clip is selected. The clip is then segmented hierarchically into scenes, shots, and finally individual frames, a necessary step because raw video files can be several gigabytes in size.
Phase‑II focuses on “place analysis,” i.e., identifying regions within each frame that are suitable for embedding. The authors distinguish between static regions (areas that remain visually unchanged across consecutive frames) and dynamic regions (areas with noticeable motion). Three techniques are described for this classification: (a) pixel‑level intensity comparison across frames, (b) likelihood analysis based on block‑level statistical similarity, and (c) color‑histogram analysis that groups pixels into discrete color baskets. The identified static and dynamic regions are stored in separate buffers for later processing.
Phase‑III introduces the stego‑key (a password) and the actual embedding algorithms. Two complementary embedding strategies are employed:
-
Static‑region embedding – In static portions, the method replaces the entire RGB triplet of a pixel with three characters (24 bits). This allows one pixel to carry three characters, compared with the conventional Least Significant Bit (LSB) approach that would require nine pixels for the same amount of data. The placement of each character follows a deterministic mathematical formula X₍ᵢⱼ₎ = i + (j‑1)·d, where i is the initial pixel index, j the character index, and d a user‑defined spacing. This deterministic distribution adds a layer of security because an attacker must know both the key and the spacing parameter to recover the payload.
-
Dynamic‑region embedding – For motion‑rich areas, the authors revert to a classic LSB technique. Each secret bit is compared with the LSB of the corresponding cover pixel; if they differ, the pixel value is incremented or decremented by one to match the secret bit. This approach minimizes perceptual distortion in regions where the human visual system is most sensitive.
Both algorithms are presented in pseudo‑code, showing the conversion of the secret message to ASCII, the sequential traversal of the cover frame array, and the writing of modified pixel values to a stego frame. After processing, the modified frames are reassembled into a “stego‑clip” that can be transmitted as a regular video file.
The extraction process is essentially the inverse of embedding. It requires the same stego‑key, the initial pixel index, and the spacing formula. By regenerating the pixel positions, the receiver reads the RGB values from static regions, converts them back to characters, and extracts LSBs from dynamic regions. The recovered bitstream is then passed through a grammar‑based parser to reconstruct the original message.
In the discussion, the authors evaluate the scheme along three dimensions: capacity, security, and robustness. Capacity is theoretically unlimited because the carrier can be as large as the video file itself. Security is layered: (1) the stego‑key, (2) the mathematical placement function, and (3) the separation of static and dynamic embedding methods, which together make statistical steganalysis more difficult. Robustness is claimed to stem from the use of static regions (where full‑pixel replacement is less likely to be altered by compression) and from the dual‑embedding strategy.
The conclusion reiterates that movies provide an excellent high‑capacity carrier, that the dual‑embedding technique enables both large payloads and low visual distortion, and that the approach could benefit sectors such as music, film, publishing, as well as governmental and military communications.
While the concept is innovative, the paper lacks empirical validation. No quantitative metrics (e.g., PSNR, SSIM, bitrate impact) are reported, and there is no analysis of how common video compression standards (H.264/AVC, HEVC) affect the hidden data. Moreover, the comparative effectiveness of the three static‑region detection methods is not experimentally demonstrated, and key management protocols are not detailed. Future work should address these gaps by providing rigorous performance evaluations, robustness tests against compression and transcoding, and a secure key‑exchange framework.
Comments & Academic Discussion
Loading comments...
Leave a Comment