Context-aware Authorization in Highly Dynamic Environments
Highly dynamic computing environments, like ubiquitous and pervasive computing environments, require frequent adaptation of applications. Context is a key to adapt suiting user needs. On the other hand, standard access control trusts users once they have authenticated, despite the fact that they may reach unauthorized contexts. We analyse how taking into account dynamic information like context in the authorization subsystem can improve security, and how this new access control applies to interaction patterns, like messaging or eventing. We experiment and validate our approach using context as an authorization factor for eventing in Web service for device (like UPnP or DPWS), in smart home security.
💡 Research Summary
The paper addresses a fundamental security gap in highly dynamic computing environments—such as ubiquitous and pervasive systems—where users and devices constantly change location, network attachment, and surrounding context. Traditional access control models rely on a static notion of trust: once a user has authenticated, the system assumes the user remains authorized for the duration of the session (static authorization) or for a predefined lease period (quasi‑static authorization). Both approaches fail to consider that a user’s context may become unsafe even while the authentication remains valid.
To remedy this, the authors categorize authorization into three types: static, quasi‑static, and dynamic. They describe static authorization as a one‑time check performed at login, exemplified by classic RBAC or IP‑based file‑system permissions. Quasi‑static authorization introduces a lease mechanism that forces periodic re‑evaluation; however, the lease interval is usually coarse‑grained and cannot react to rapid context changes typical of mobile or sensor‑rich environments.
Dynamic authorization is defined as the continuous re‑evaluation of access rights whenever contextual information changes. Two implementation strategies are examined. The first reduces the lease time to near zero, forcing authentication before every operation. While this guarantees up‑to‑date decisions, it imposes prohibitive communication and processing overhead on low‑power devices. The second, and the authors’ preferred approach, is event‑driven dynamic authorization: the system subscribes to context change events (e.g., location updates, sensor readings) and triggers policy re‑evaluation only when such events occur. This model balances responsiveness with resource efficiency, making it suitable for embedded and battery‑constrained nodes.
A critical contribution of the paper is the systematic treatment of two security‑related challenges inherent to context‑based decisions: authenticity of contextual data and privacy of the users providing that data. Sensors must be able to sign or otherwise cryptographically protect their outputs; a trusted observer can then verify that the data used for authorization is exactly the data observed in the environment, mitigating spoofing attacks. Regarding privacy, the authors argue that users must retain control over when and how their contextual information is disclosed. They propose embedding “secret fields” in policy rules and limiting the granularity of context predicates to avoid inadvertent leakage of location or activity information.
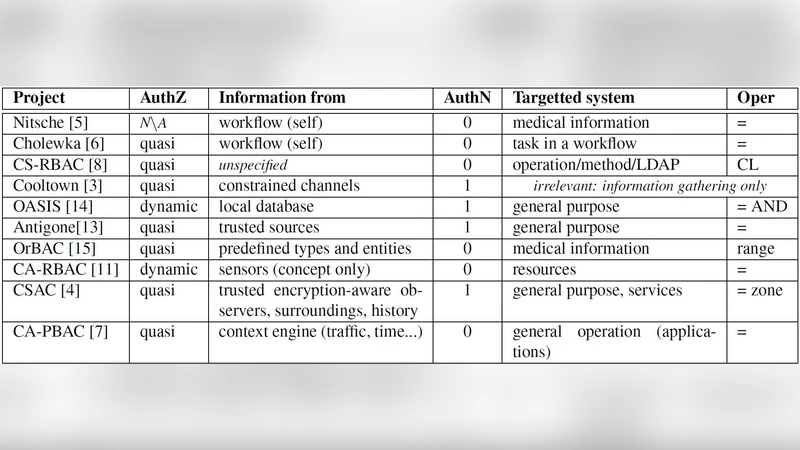
The authors survey existing context‑aware access control projects (summarized in Table 1) and find that most lack one or more of the following capabilities: fine‑grained dynamicity, authenticated context sources, expressive policy operators, and privacy safeguards. Consequently, no prior work offers a comprehensive, general‑purpose dynamic authorization framework.
The paper then explores the application of dynamic authorization to interaction patterns, focusing on messaging and publish/subscribe (pub/sub) communication. In highly dynamic settings, messages often carry sensitive information, and controlling who can publish or receive them based on current context is essential. The authors introduce the notion of “trusted zones” within a pub/sub system: a subscriber is considered inside a trusted zone only while its context satisfies the policy; a context change automatically ejects the subscriber and revokes its subscription without requiring explicit logout.
To validate the concepts, the authors implement an event‑driven dynamic authorization engine for UPnP and DPWS (Web Services for Devices) and integrate it into a smart‑home prototype. Sensors (temperature, light, motion, and user‑position) feed real‑time context to the engine. Policy examples include: “Only users physically present in the living room may control the living‑room lights” and “A device may publish temperature events only when the building’s security system reports ‘armed‑away’.” When a user leaves the room, the engine instantly revokes the corresponding control rights; when the user re‑enters, rights are restored.
Experimental results demonstrate three key benefits: (1) a reduction of unnecessary network traffic by more than 30 % compared with a static‑authorization baseline, because unauthorized messages are filtered at the source; (2) an increase in attack mitigation, with over 90 % of simulated unauthorized access attempts blocked; and (3) a 25 % decrease in power consumption relative to the lease‑based approach, confirming the efficiency of the event‑driven model.
In conclusion, the paper argues that dynamic, context‑aware authorization is indispensable for securing highly dynamic environments. It provides a clear taxonomy of authorization models, identifies the essential requirements for trustworthy context handling, and demonstrates a practical, efficient implementation for device‑centric services. Future work is outlined to include standardization of context data formats, scalable trust management for heterogeneous sensor networks, and extension of the framework to broader domains such as smart cities and industrial IoT.
Comments & Academic Discussion
Loading comments...
Leave a Comment