EPS Confidentiality and Integrity mechanisms Algorithmic Approach
The Long Term Evolution of UMTS is one of the latest steps in an advancing series of mobile telecommunications systems. Many articles have already been published on the LTE subject but these publications have viewed the subject from particular perspectives. In the present paper, a different approach has been taken. We are interested in the security features and the cryptographic algorithms used to ensure confidentiality and integrity of the transmitted data. A closer look is taken to the two EPS confidentiality and integrity algorithms based on the block cipher algorithm AES: the confidentiality algorithm EEA2 and the integrity algorithm EIA2. Furthermore, we focused on the implementation of both algorithms in C language in respect to the specifications requirements. We have tested our implementations according to the testsets given by the 3rd Generation Partnership Project (3GPP) implementation document. Some examples of the implementation tests are presented bellow.
💡 Research Summary
**
The paper provides a thorough examination of the confidentiality and integrity mechanisms employed in the LTE‑Evolved Packet System (EPS), focusing specifically on the two AES‑based algorithms defined by 3GPP: EEA2 for encryption and EIA2 for integrity protection. After a concise overview of the LTE protocol stack, the authors explain how the PDCP layer handles security for both user‑plane and control‑plane traffic, distinguishing the processing of payload data from that of MAC‑I fields attached to signaling messages.
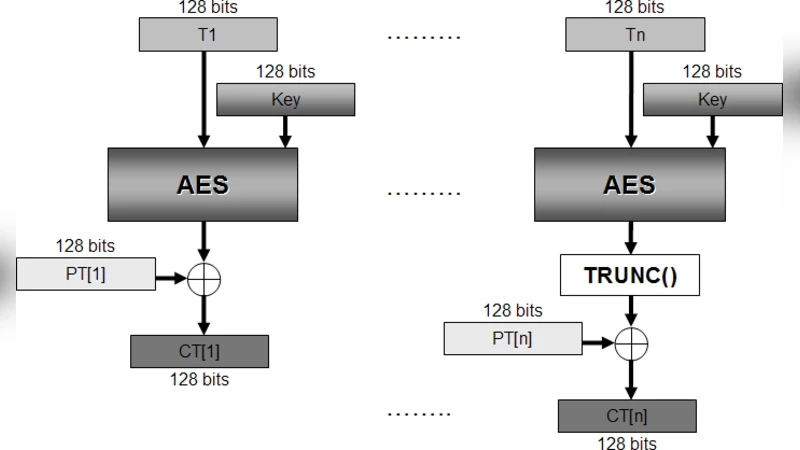
EEA2 is described as a stream cipher built on AES‑128 operating in Counter (CTR) mode. The algorithm takes as inputs the 32‑bit COUNT, 5‑bit BEARER, a 1‑bit DIRECTION flag, the length of the data to be protected, and a 128‑bit encryption key (different keys are used for user‑plane, RRC, and NAS). The first counter block T₁ is formed by concatenating COUNT‖BEARER‖DIRECTION‖26 zero bits as the most‑significant 64 bits, while the least‑significant 64 bits are set to zero. Subsequent counters are generated by incrementing the low 64‑bit word modulo 2⁶⁴. Each counter block is encrypted with AES‑128, producing a 128‑bit keystream segment that is XOR‑ed with the corresponding plaintext block. The final block may be truncated to match the exact payload length. Because CTR mode uses only the AES encryption primitive, encryption and decryption are identical operations, which simplifies implementation and enables high‑throughput processing.
EIA2, on the other hand, provides integrity protection by computing a 32‑bit Message Authentication Code (MAC‑I) using AES‑CMAC. Its inputs are a 32‑bit COUNT, a 5‑bit BEARER, a 1‑bit DIRECTION, the message itself, and a 128‑bit integrity key (separate keys for RRC and NAS). The algorithm first builds a 128‑bit block in the same way as EEA2’s counter, encrypts it to derive sub‑keys, and then processes the padded message through the CMAC construction. The resulting MAC‑I is appended to the RRC or NAS message, allowing the receiver to verify both authenticity and integrity.
The authors implemented both algorithms in C, paying particular attention to endianess and memory alignment issues that can cause subtle bugs on different processor architectures. They explicitly convert data to network byte order, use 64‑bit unsigned integers for counter increments, and ensure that the AES core operates on correctly aligned blocks. The implementation was validated against the official 3GPP test vectors defined in TS 33.401. All twelve test sets were executed successfully; the paper presents one representative example where a given key, COUNT, BEARER, DIRECTION, and plaintext of 310 bits produce the exact ciphertext specified by the standard.
Beyond the implementation details, the paper discusses why AES was chosen over the legacy SNOW 3G‑based UEA1/UIA1 algorithms. AES offers royalty‑free licensing, is already required for IP‑based security (NDS/IP) in the eNodeB, and provides a unified cryptographic primitive that can be hardware‑accelerated. By reusing the same AES engine for both confidentiality (CTR) and integrity (CMAC), the LTE‑EPS design reduces code size, simplifies certification, and achieves the performance needed for high‑speed mobile data.
In conclusion, the study not only clarifies the internal workings of EEA2 and EIA2 but also demonstrates a practical, standards‑compliant C implementation that passes all official verification vectors. The work serves as a valuable reference for engineers developing LTE‑compatible equipment, for researchers investigating mobile security protocols, and for anyone interested in the transition from stream‑cipher‑based to block‑cipher‑based security in modern cellular networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment