A new protocol implementing authentication transformations for multi-located parties
This paper discusses a new protocol implementing authentication in a multi-located environment that avoids man-in-the-middle (MIM) attack, replay attack and provides privacy, integrity of a message for multi-located parties. The protocol uses the concept that each party is associated with a subsidiary agent.
💡 Research Summary
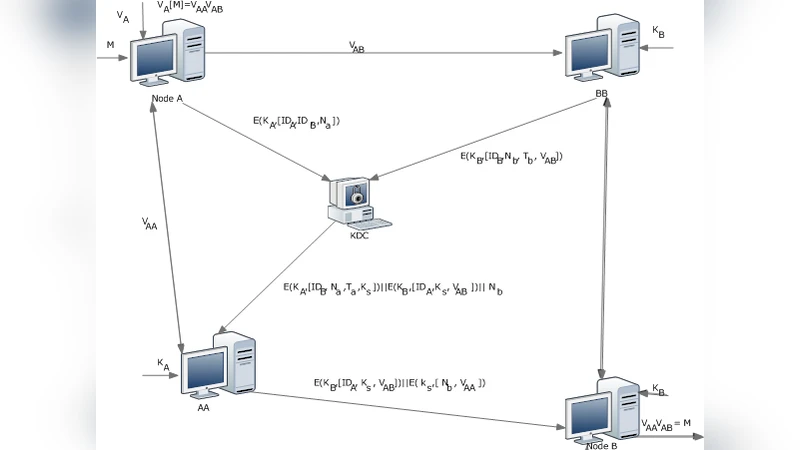
The paper presents a novel three‑stage protocol designed for communication between parties that are geographically distributed and each supported by a subsidiary agent. Building on Kak’s earlier work on multi‑located cryptography, the authors integrate a classical symmetric‑key authentication scheme (the Needham‑Schroeder protocol) with a linguistic transformation based on context‑free grammars. The core idea is to convert the plaintext into a sequence of production‑rule numbers using a shared grammar, then split this sequence into two fragments (V_AA and V_AB). These fragments are sent over separate, insecure channels to the two agents (AA for the sender and BB for the receiver).
The protocol proceeds as follows:
-
Initial Transformation and Distribution – Sender A encodes the message into bits, applies a pre‑agreed grammar to obtain a production‑rule number string, and divides it into V_AA and V_AB. Simultaneously, A encrypts (ID_A, ID_B, N_A) with its secret key K_A and sends it to a Key Distribution Center (KDC).
-
Agent‑to‑KDC Communication – Receiver’s agent BB encrypts (ID_B, N_B, T_B, V_AB) with its secret key K_B and forwards it to the KDC.
-
KDC Session‑Key Generation – The KDC generates a fresh session key K_S. It returns to AA (the sender’s agent) an encrypted package containing (ID_B, N_A, T_B, K_S) under K_A, and to BB an encrypted package containing (ID_A, K_S, V_AB) under K_B.
-
Agent‑Mediated Exchange – AA uses K_S to protect the nonce N_B and the fragment V_AA, then sends both the K_B‑encrypted (ID_A, K_S, V_AB) and the K_S‑encrypted (N_B, V_AA) to the final destination B.
-
Reconstruction at the Receiver – B receives the two fragments, recombines them into the full production‑rule sequence, and, using the shared grammar, reconstructs the original plaintext.
Security analysis highlights several strengths. The inclusion of nonces (N_A, N_B) and timestamps (T_B) prevents replay attacks, while the three‑stage exchange guarantees mutual authentication. By splitting the transformed message, no single intermediate node possesses enough information to reconstruct the secret, mitigating man‑in‑the‑middle (MITM) threats. The reliance on a KDC provides a trusted source for session keys, ensuring confidentiality and integrity of the exchanged data.
The authors also acknowledge limitations. The KDC is a single point of trust; its compromise would endanger the entire system. The protocol’s dependence on multiple agents and separate channels introduces additional latency and bandwidth overhead, making it vulnerable to denial‑of‑service (DoS) attacks that flood specific agents. Moreover, the security of the linguistic transformation hinges on the secrecy and randomness of the chosen grammar; if an adversary learns the grammar or can infer patterns in the production‑rule numbers, partial information leakage could occur.
In conclusion, the paper contributes a hybrid approach that merges classical authentication with grammar‑based secret sharing, offering a promising solution for multi‑located environments where direct secure channels are unavailable. Future work is suggested to incorporate puzzle‑based key distribution and recursive hidden‑secret techniques to further harden the protocol against active attacks and to address the identified DoS vulnerability.
Comments & Academic Discussion
Loading comments...
Leave a Comment