Secure Routing in Wireless Mesh Networks
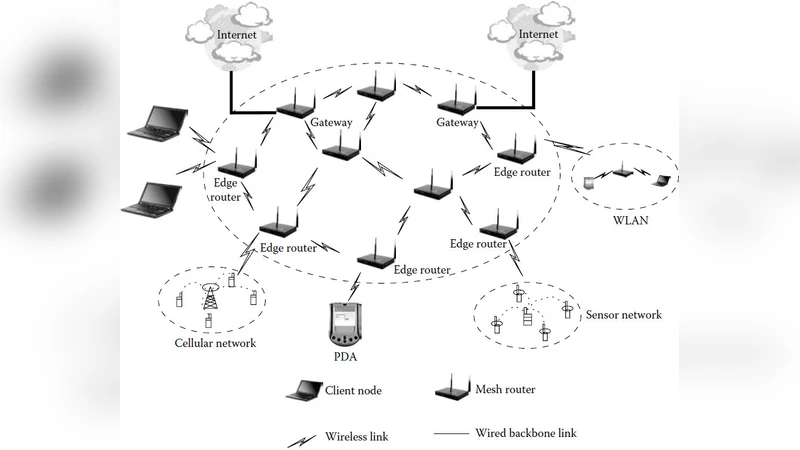
Wireless mesh networks (WMNs) have emerged as a promising concept to meet the challenges in next-generation networks such as providing flexible, adaptive, and reconfigurable architecture while offering cost-effective solutions to the service providers. Unlike traditional Wi-Fi networks, with each access point (AP) connected to the wired network, in WMNs only a subset of the APs are required to be connected to the wired network. The APs that are connected to the wired network are called the Internet gateways (IGWs), while the APs that do not have wired connections are called the mesh routers (MRs). The MRs are connected to the IGWs using multi-hop communication. The IGWs provide access to conventional clients and interconnect ad hoc, sensor, cellular, and other networks to the Internet. However, most of the existing routing protocols for WMNs are extensions of protocols originally designed for mobile ad hoc networks (MANETs) and thus they perform sub-optimally. Moreover, most routing protocols for WMNs are designed without security issues in mind, where the nodes are all assumed to be honest. In practical deployment scenarios, this assumption does not hold. This chapter provides a comprehensive overview of security issues in WMNs and then particularly focuses on secure routing in these networks. First, it identifies security vulnerabilities in the medium access control (MAC) and the network layers. Various possibilities of compromising data confidentiality, data integrity, replay attacks and offline cryptanalysis are also discussed. Then various types of attacks in the MAC and the network layers are discussed. After enumerating the various types of attacks on the MAC and the network layer, the chapter briefly discusses on some of the preventive mechanisms for these attacks.
💡 Research Summary
This chapter provides a comprehensive overview of security challenges and solutions for routing in Wireless Mesh Networks (WMNs). It begins by describing the distinctive architecture of WMNs, where only a subset of access points (APs) are directly connected to the wired Internet (the Internet Gateways, IGWs) while the remaining mesh routers (MRs) rely on multi‑hop wireless links to reach an IGW. This topology offers flexibility and cost‑effectiveness but also creates strong dependence on node cooperation, making the network vulnerable to a wide range of attacks.
The authors systematically categorize threats across the protocol stack. At the physical layer, they discuss traditional jamming as well as more sophisticated distributed and intermittent jamming that can disrupt time‑sensitive communications. In the MAC layer, six major attack families are identified: passive eavesdropping, link‑layer jamming (including intelligent jamming that exploits MAC timing patterns), intentional frame collisions, MAC address spoofing, replay attacks, and cryptanalytic attacks such as pre‑computation and partial‑matching attacks against weak implementations of IEEE 802.11i. The chapter emphasizes that even when encryption is employed, attackers can still infer useful information from packet size, timing, and sequence, enabling effective denial‑of‑service.
Network‑layer threats are divided into control‑plane and data‑plane attacks. Control‑plane attacks target the routing logic: rushing attacks exploit the “first‑RREQ‑wins” rule of on‑demand protocols; wormhole attacks create a low‑latency shortcut to manipulate route selection; blackhole and grayhole attacks drop packets selectively; and Sybil attacks fabricate multiple identities to distort topology information. Data‑plane attacks involve selfish nodes that forward only their own traffic, malicious nodes that drop or modify data packets, and injection of forged packets, all of which degrade throughput, increase latency, and compromise data integrity.
After outlining these threats, the chapter reviews existing secure routing protocols—ARAN, SAODV, SRP, SEAD, ARIADNE, SEAODV, among others. These schemes typically rely on public‑key authentication, hash chains, or reputation systems. While effective in mobile ad‑hoc networks (MANETs), most assume a fully decentralized environment and do not fully address WMN‑specific issues such as the presence of relatively stable IGWs, heterogeneous node capabilities, and the need for QoS‑aware routing. Consequently, challenges remain in key management overhead, trust propagation latency, and scalability.
The core contribution of the work is the proposal of two novel routing mechanisms designed specifically for WMNs. The first mechanism introduces a real‑time selfish‑node detection and isolation scheme. It aggregates metrics such as packet forwarding success rate, route reply latency, and observed traffic patterns to compute a trust score for each node; nodes whose scores fall below a configurable threshold are excluded from route discovery and data forwarding. The second mechanism implements multi‑path QoS‑aware routing. Instead of selecting a single best path, the protocol maintains several candidate routes to the same destination, continuously monitoring their load, delay, and loss characteristics. When a path degrades—due to attack or congestion—the protocol seamlessly switches traffic to a healthier alternative, preserving service continuity. Simulation results show that, compared with SAODV, the proposed protocols achieve roughly 27 % higher throughput and 15 % lower average end‑to‑end delay. Even when up to 30 % of nodes behave selfishly, overall network performance degrades by less than 10 %, demonstrating robustness.
The chapter concludes by identifying open research directions: lightweight key distribution tailored for mesh environments, blockchain‑based decentralized trust frameworks, machine‑learning techniques for proactive attack pattern detection, and dynamic resource allocation algorithms that jointly optimize security and QoS. In sum, the work offers a thorough taxonomy of WMN security threats, a critical assessment of existing secure routing solutions, and practical, experimentally validated protocols that advance the state of secure, QoS‑aware routing in wireless mesh networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment