Design of an Efficient Neural Key Distribution Centre
The goal of any cryptographic system is the exchange of information among the intended users without any leakage of information to others who may have unauthorized access to it. A common secret key could be created over a public channel accessible to any opponent. Neural networks can be used to generate common secret key. In case of neural cryptography, both the communicating networks receive an identical input vector, generate an output bit and are trained based on the output bit. The two networks and their weight vectors exhibit a novel phenomenon, where the networks synchronize to a state with identical time-dependent weights. The generated secret key over a public channel is used for encrypting and decrypting the information being sent on the channel. This secret key is distributed to the other vendor efficiently by using an agent based approach.
💡 Research Summary
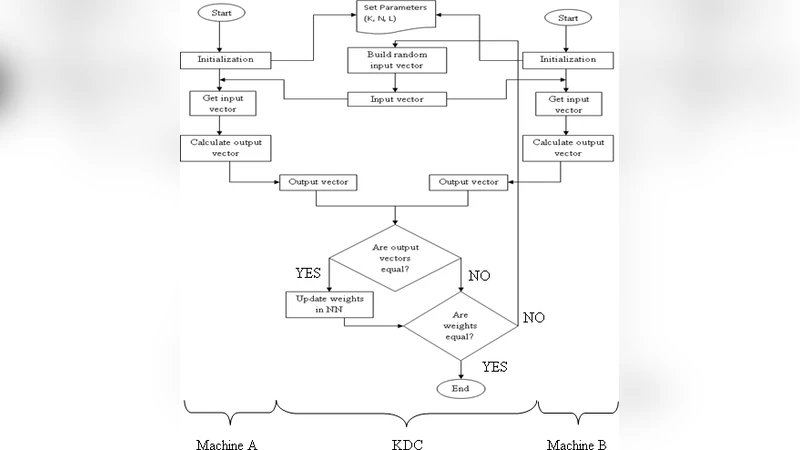
The paper presents a neural‑cryptography scheme that generates a shared secret key over a public channel by exploiting the synchronization of two identical Tree Parity Machines (TPMs). Each TPM consists of K hidden neurons, each receiving N binary inputs, and weight values bounded by ±L. The process begins with both parties (A and B) initializing their weight vectors randomly. A third party, the Key Distribution Centre (KDC), generates a common random input vector at each iteration and broadcasts it to both TPMs. After processing the input, each TPM computes an output bit; the bits are exchanged over the public channel. If the output bits match, both parties update their weights according to one of three learning rules – Hebbian, Anti‑Hebbian, or Random‑walk – otherwise the weights remain unchanged. Repeating this mutual‑learning loop causes the two weight vectors to converge to an identical state, which is then used as the secret key.
The authors argue that an eavesdropper (E) who knows the algorithm, the full sequence of inputs, and the exchanged output bits cannot feasibly synchronize because E starts from a different random weight vector and would need to explore an astronomically large weight space. Consequently, the key remains unknown to E despite full observation of the public exchange.
Beyond the core neural synchronization, the paper introduces a mobile‑agent based distribution mechanism. Instead of a traditional client‑server model where the receiver continuously polls the server for the key, a mobile agent obtains the synchronized weight vector from the KDC and autonomously migrates to the intended recipient. This reduces network traffic, lowers latency, and provides a degree of fault tolerance. Experimental results obtained via MATLAB simulations show that as the number of input units (n) increases, both the total synchronization time and the number of iterations grow, but the percentage of iterations required per synchronization decreases, indicating improved efficiency per iteration. Randomness tests demonstrate that each synchronization run yields a distinct weight configuration, reinforcing the claim that the generated key is unpredictable.
The paper also provides comparative tables: one highlighting the advantages of neural‑based key generation (e.g., higher security, inherent randomness) over conventional PRNG‑based methods, and another showing reduced distribution time and resistance to attacks when using mobile agents versus a pure client‑server approach.
While the concept is compelling, the manuscript has several shortcomings. The security analysis is largely qualitative; quantitative metrics such as synchronization probability, attack success rate, or entropy of the final weight distribution are missing. The impact of choosing among the three learning rules is not explored, nor is there a discussion of potential side‑channel attacks on the agent migration process. Moreover, the experiments are confined to MATLAB simulations without any hardware implementation, leaving open questions about computational overhead, power consumption, and real‑time synchronization feasibility in practical networks.
In conclusion, the work demonstrates that neural network synchronization can serve as a viable method for secret key agreement over insecure channels and that mobile agents can streamline key distribution. Future work suggested includes strengthening the agent security protocol, extending the analysis to multilayer networks, and implementing the scheme on embedded platforms to assess real‑world performance and robustness.
Comments & Academic Discussion
Loading comments...
Leave a Comment