We study the communication complexity of symmetric XOR functions, namely functions $f: \{0,1\}^n \times \{0,1\}^n \rightarrow \{0,1\}$ that can be formulated as $f(x,y)=D(|x\oplus y|)$ for some predicate $D: \{0,1,...,n\} \rightarrow \{0,1\}$, where $|x\oplus y|$ is the Hamming weight of the bitwise XOR of $x$ and $y$. We give a public-coin randomized protocol in the Simultaneous Message Passing (SMP) model, with the communication cost matching the known lower bound for the \emph{quantum} and \emph{two-way} model up to a logarithm factor. As a corollary, this closes a quadratic gap between quantum lower bound and randomized upper bound for the one-way model, answering an open question raised in Shi and Zhang \cite{SZ09}.
Deep Dive into Tight bounds on the randomized communication complexity of symmetric XOR functions in one-way and SMP models.
We study the communication complexity of symmetric XOR functions, namely functions $f: \{0,1\}^n \times \{0,1\}^n \rightarrow \{0,1\}$ that can be formulated as $f(x,y)=D(|x\oplus y|)$ for some predicate $D: \{0,1,...,n\} \rightarrow \{0,1\}$, where $|x\oplus y|$ is the Hamming weight of the bitwise XOR of $x$ and $y$. We give a public-coin randomized protocol in the Simultaneous Message Passing (SMP) model, with the communication cost matching the known lower bound for the \emph{quantum} and \emph{two-way} model up to a logarithm factor. As a corollary, this closes a quadratic gap between quantum lower bound and randomized upper bound for the one-way model, answering an open question raised in Shi and Zhang \cite{SZ09}.
Communication complexity quantifies the minimum amount of communication needed for two (or sometimes more) parties to jointly compute some function f . Since introduced by Yao [Yao79], it has attracted significant attention in the last three decades, not only for its elegant mathematical structure but also for its numerous applications in other computational models [KN97,LS09].
The two parties involved in the computation, usually called Alice and Bob, can communicate in different manners, and here we consider the three well-studied models, namely the two-way model, the one-way model and the simultaneous message passing (SMP) model. In the two-way model, Alice and Bob are allowed to communicate interactively in both directions, while in the one-way model, Alice can send message to Bob and Bob does not give feedback to Alice. An even weaker communication model is the SMP model, where Alice and Bob are prohibited to exchange information directly, but instead they each send a message to a third party Referee, who then announces a result. A randomized protocol is called private-coin if Alice and Bob each flip their own and private random coins. If they share the same random coins, then the protocol is called public-coin. The private coin model differs from the public coin model by at most an additive factor of O(log n) in the two-way and one-way models [New91].
We use R priv (f ) to denote the communication complexity of a best private-coin randomized protocol that computes f with error at most 1/3 in the two-way protocol. Similarly, we use the R ||,priv (f ) to denote the communication complexity in the private-coin SMP model, and R 1,priv (f ) for the private-coin one-way model. Changing the superscript “priv” to “pub” gives the notation for the communication complexities in the public-coin models. If we allow Alice and Bob to use quantum protocols, then Q(f ), Q 1 (f ), Q || (f ) represent the quantum communication complexity in two-way model, one-way model and SMP model, separately. In the quantum case the communication complexity is evaluated in terms of the number of qubits in the communication. If Alice and Bob share prior entanglement, then we use a star in the superscript to denote the communication complexity.
Arguably the most fundamental issue in communication complexity is to determine the largest gap between the quantum and classical complexity. In particular, there is no superconstant separation between quantum and classical complexities in the one-way model; actually, it could well be the truth that they are the same up to a constant factor for all total Boolean functions.
One way to understand the question is to study special classes of functions. An important class of Boolean functions is that of XOR functions, namely those in the form of f (x ⊕ y) where x ⊕ y is the bitwise XOR of x and y. Some well studied functions such as the Equality function and the Hamming Distance function are special cases of XOR functions. XOR functions belong to a larger class of “composed functions”; see [LZ10] for some recent studies.
While the general XOR function seems hard to study, recently Shi and Zhang [SZ09] considered symmetric XOR functions, i.e. f (x ⊕ y) = D(|x ⊕ y|) for some D : {0, 1, …, n} → {0, 1}. Define r 0 and r 1 to be the minimum integers such that r 0 , r 1 ≤ n/2 and D(k) = D(k + 2) for all k ∈ [r 0 , n -r 1 ) and set r = max{r 0 , r 1 }. Shi and Zhang proved that the quantum lower bound for symmetric XOR functions in the two-way model is Ω(r), and on the other hand, they also gave randomized protocol in communication of Õ(r) in the two-way model and Õ(r 2 ) in the one-way model. Pinning down the quantum and randomized communication complexity of symmetric XOR functions in the one-way model was raised as an open problem.
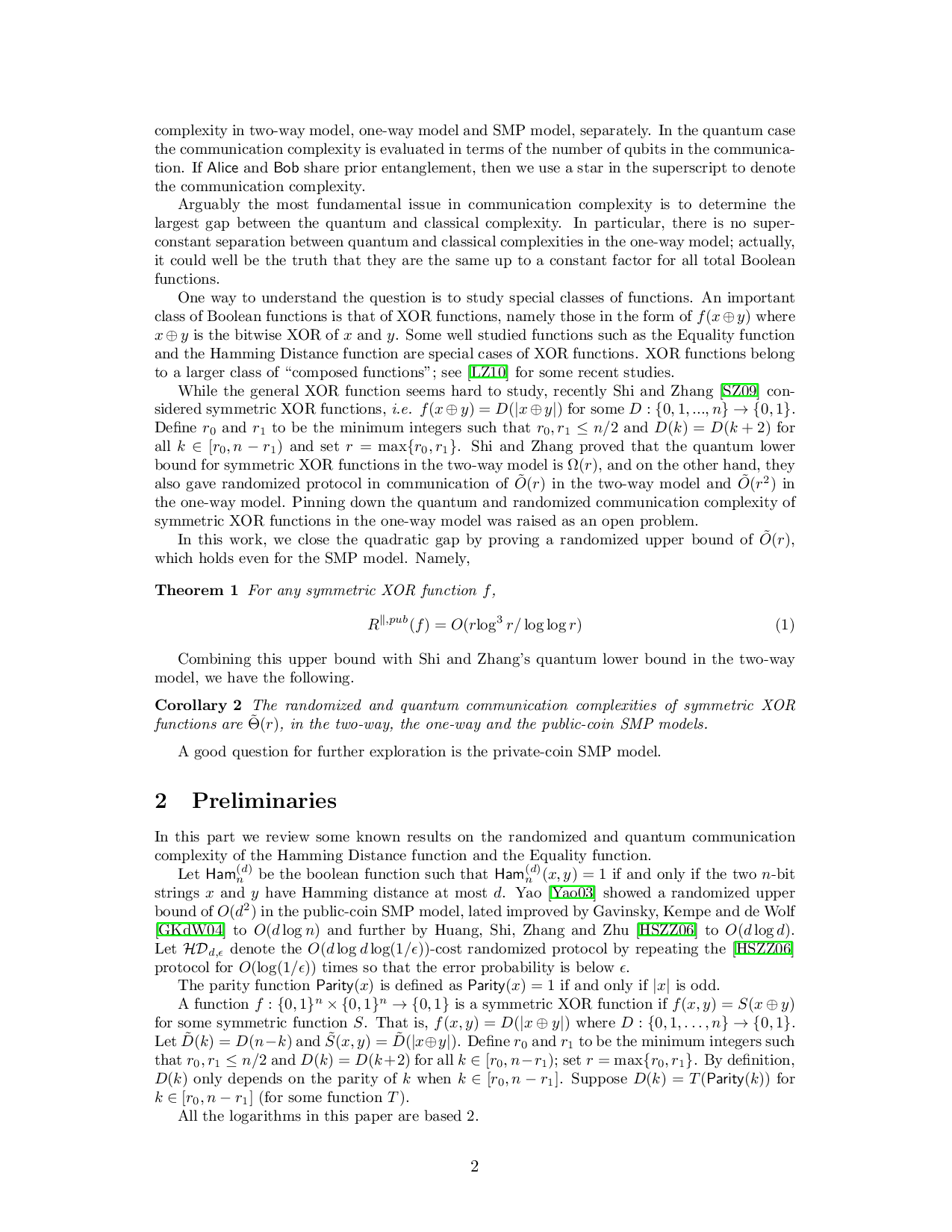
In this work, we close the quadratic gap by proving a randomized upper bound of Õ(r), which holds even for the SMP model. Namely,
Combining this upper bound with Shi and Zhang’s quantum lower bound in the two-way model, we have the following.
A good question for further exploration is the private-coin SMP model.
In this part we review some known results on the randomized and quantum communication complexity of the Hamming Distance function and the Equality function.
Let Ham (d) n be the boolean function such that Ham All the logarithms in this paper are based 2.
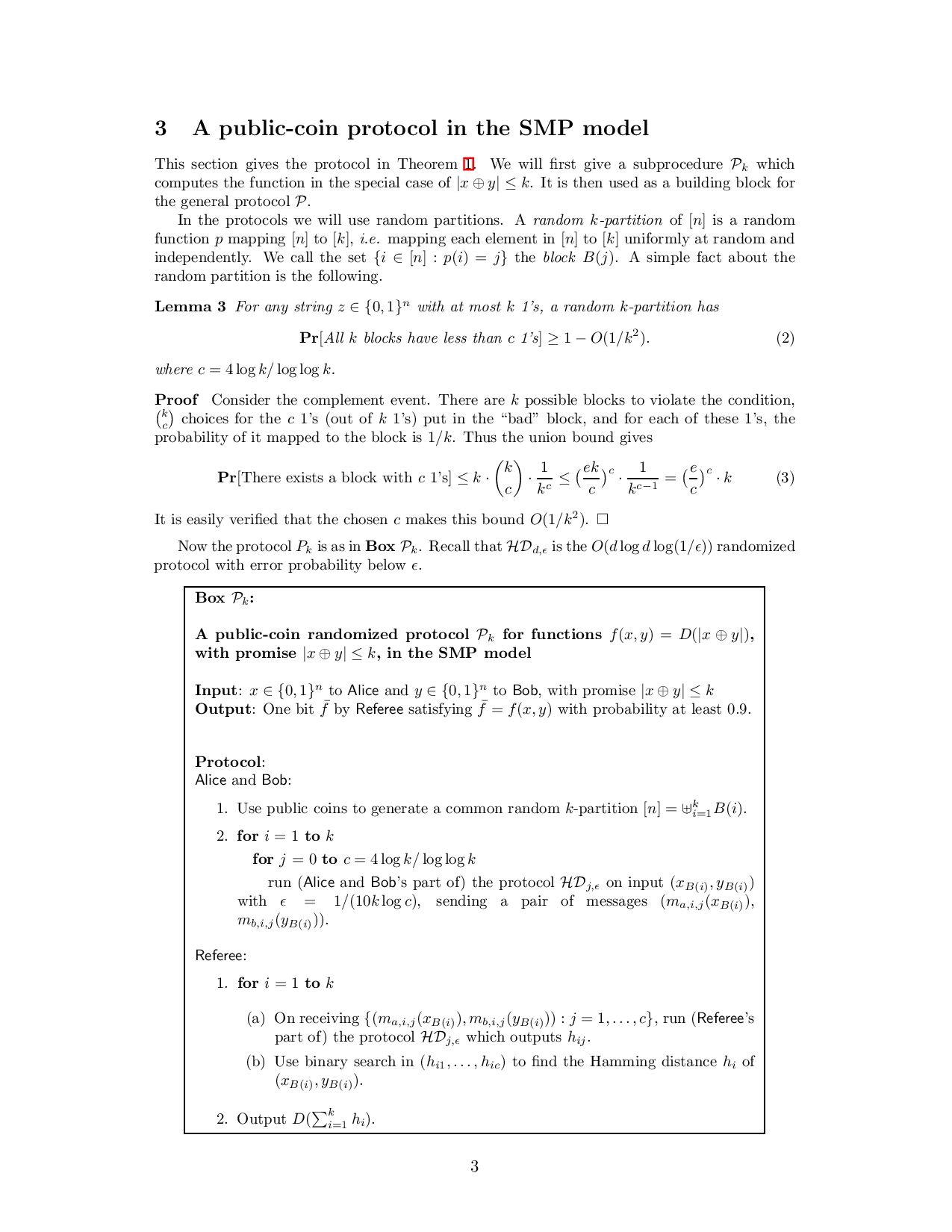
This section gives the protocol in Theorem 1. We will first give a subprocedure P k which computes the function in the special case of |x ⊕ y| ≤ k. It is then used as a building block for the general protocol P.
In the protocols we will use random partitions. A random k-partition of [n] is a random function p mapping [n] to [k], i.e. mapping each element in [n] to [k] uniformly at random and independently. We call the set {i ∈ [n] : p(i) = j} the block B(j). A simple fact about the random partition is the following.
Lemma 3 For any string z ∈ {0, 1} n with at most k 1’s, a random k-partition has
(
where
…(Full text truncated)…
This content is AI-processed based on ArXiv data.