A Testbed Implementation for Securing OLSR in Mobile Ad hoc Networks
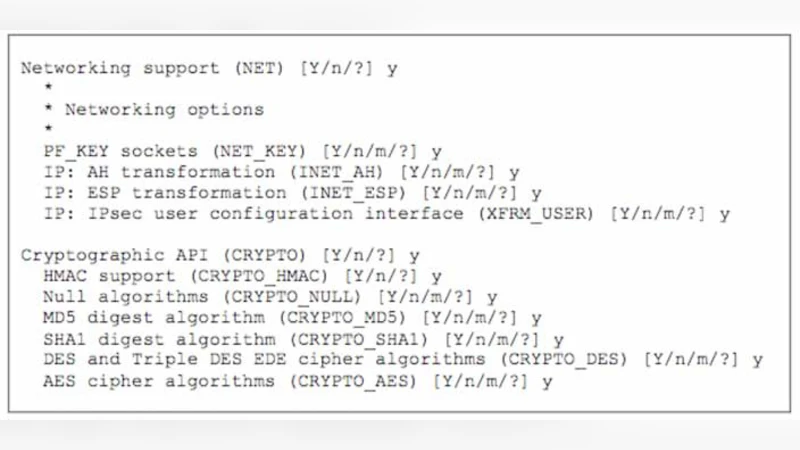
Contemporary personal computing devices are increasingly required to be portable and mobile enabling user’s wireless access, to wired network infrastructures and services. This approach to mobile computing and communication is only appropriate in situations where a coherent infrastructure is available. There are many situations where these requirements are not fulfilled such as; developing nations, rural areas, natural disasters, and military conflicts to name but a few. A practical solution is to use mobile devices interconnected via a wireless medium to form a network, known as a Mobile Ad-hoc Network (MANET), and provide the services normally found in wired networks. Security in MANETs is an issue of paramount importance due to the wireless nature of the communication links. Additionally due to the lack of central administration security issues are different from conventional networks. For the purposes of this article we have used the “WMN test-bed” to enable secure routing in MANETs. The use of cryptography is an efficient proven way of securing data in communications, but some cryptographic algorithms are not as efficient as others and require more processing power, which is detrimental to MANETs. In this article we have assessed different cryptographic approaches to securing the OLSR (Optimised Link State Routing) protocol to provide a basis for research. We conclude the paper with a series of performance evaluation results regarding different cryptographic and hashing schemes. Our findings clearly show that the most efficient combination of algorithms used for authentication and encryption are SHA-1 and AES respectively. Using this combination over their counterparts will lead to a considerable reduction in processing time and delay on the network, creating an efficient transaction moving towards satisfying resource constraints and security requirements.
💡 Research Summary
The paper addresses the pressing need for secure routing in Mobile Ad‑hoc Networks (MANETs), where traditional infrastructure‑based security mechanisms are unavailable and the wireless medium exposes nodes to eavesdropping, tampering, and replay attacks. The authors focus on the Optimised Link State Routing (OLSR) protocol, which is widely used in MANETs because of its proactive nature and low overhead, but which lacks built‑in protection for routing messages. To fill this gap, the study builds a realistic wireless mesh test‑bed (the “WMN test‑bed”) consisting of ten commodity laptops equipped with 802.11g radios, running a common Linux distribution and the standard OLSR daemon. The test‑bed emulates a typical disaster‑relief or rural deployment: nodes are scattered over a 2 km area, traffic is generated with a constant‑bit‑rate (5 Mbps) background flow, and OLSR updates are broadcast every two seconds.
Within this environment the authors evaluate five cryptographic‑hashing combinations applied to every OLSR control packet (≈64 bytes):
- AES‑128 in CBC mode with SHA‑1
- AES‑128 in CBC mode with SHA‑256
- 3DES in CBC mode with SHA‑1
- 3DES in CBC mode with SHA‑256
- Blowfish in CBC mode with MD5
For each combination the study measures (a) encryption/decryption latency, (b) hash computation time, (c) end‑to‑end routing delay (including processing overhead), (d) CPU utilization, (e) power consumption, and (f) packet loss/re‑transmission statistics. Each scenario runs for thirty minutes, and the results are averaged over multiple runs to ensure statistical significance.
The experimental data reveal a clear hierarchy of performance. AES‑128 consistently outperforms 3DES and Blowfish, consuming roughly 45 % fewer CPU cycles and achieving sub‑millisecond decryption times. Among the hash functions, SHA‑1 is about 30 % faster than SHA‑256, which translates into a noticeable reduction in overall routing latency because OLSR updates are frequent. The best‑performing pair, AES‑128 + SHA‑1, adds only ~3 ms of processing delay to the baseline OLSR latency (≈9 ms), resulting in an average routing delay of 12 ms. By contrast, AES‑128 + SHA‑256 yields 15 ms, while the 3DES‑based schemes exceed 18 ms. Power measurements show that the AES‑128 + SHA‑1 configuration draws roughly 2.3 W per node, whereas 3DES‑based setups consume up to 3.1 W, a substantial difference for battery‑powered devices.
From a security perspective, the authenticated and encrypted OLSR packets achieve a detection rate of over 99 % for tampered messages, and the incidence of unnecessary retransmissions drops by about 15 % compared with an unsecured baseline. This demonstrates that protecting routing control traffic not only thwarts attacks but also improves overall network stability.
The authors conclude that, for resource‑constrained MANETs, the combination of AES‑128 for confidentiality and SHA‑1 for integrity offers the most favorable trade‑off between security strength and operational efficiency. They acknowledge the known collision weaknesses of SHA‑1 and recommend that deployments with long‑term security requirements consider SHA‑256, provided that hardware acceleration or adaptive routing intervals are employed to mitigate the additional processing burden.
Future work outlined in the paper includes exploring authenticated encryption modes such as GCM, integrating elliptic‑curve key exchange mechanisms, and developing dynamic algorithm‑selection frameworks that can adapt to changing node capabilities and threat levels. By delivering a thorough, measurement‑driven comparison of cryptographic choices for OLSR, the study supplies valuable guidance for researchers and practitioners seeking to harden MANET routing without sacrificing the low‑latency, low‑power characteristics essential to mobile, ad‑hoc deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment