Automated Validation of Security-sensitive Web Services specified in BPEL and RBAC (Extended Version)
We formalize automated analysis techniques for the validation of web services specified in BPEL and a RBAC variant tailored to BPEL. The idea is to use decidable fragments of first-order logic to describe the state space of a certain class of web services and then use state-of-the-art SMT solvers to handle their reachability problems. To assess the practical viability of our approach, we have developed a prototype tool implementing our techniques and applied it to a digital contract signing service inspired by an industrial case study.
💡 Research Summary
The paper addresses the problem of automatically validating security‑sensitive web services that are specified using the Business Process Execution Language (BPEL) together with a role‑based access control (RBAC) model that is specifically adapted to BPEL. The authors first introduce a formal integration of BPEL and RBAC, called BPEL‑RBAC, which enriches a BPEL process with explicit security annotations. In this model, roles, permissions, constraints, and role hierarchies are mapped onto BPEL activities (such as invoke, receive, assign, and control‑flow constructs). This unified representation makes it possible to reason about both the functional workflow and the associated access‑control policy within a single formal framework.
To enable automated analysis, the authors translate the combined BPEL‑RBAC specification into a decidable fragment of first‑order logic. They define a set of logical variables that capture the current execution state of each BPEL activity, the current role assignments, and the values of data objects. Transition rules encode how these variables are updated when an activity fires, including the evaluation of role‑permission checks and any contextual constraints (e.g., “only a manager may execute the payment step”). The initial state of the service instance is similarly encoded. Security properties of interest—typically expressed as safety properties such as “no unauthorized role can read the contract content” or “the signing step is reachable only after a valid approval”—are formulated as logical predicates over the state variables.
Because the resulting formulas belong to fragments such as Effectively Propositional Logic (EPR) or Linear Integer Arithmetic (LIA), they can be handed to state‑of‑the‑art Satisfiability Modulo Theories (SMT) solvers (Z3, CVC4, etc.). The verification procedure consists of two main steps: (1) a reachability query that asks whether a state violating a given security property is reachable from the initial state, and (2), if the answer is affirmative, extraction of a concrete counterexample trace that shows the exact sequence of activity executions, role assignments, and data updates leading to the violation. This counterexample can be directly inspected by developers to pinpoint policy misconfigurations or workflow design flaws.
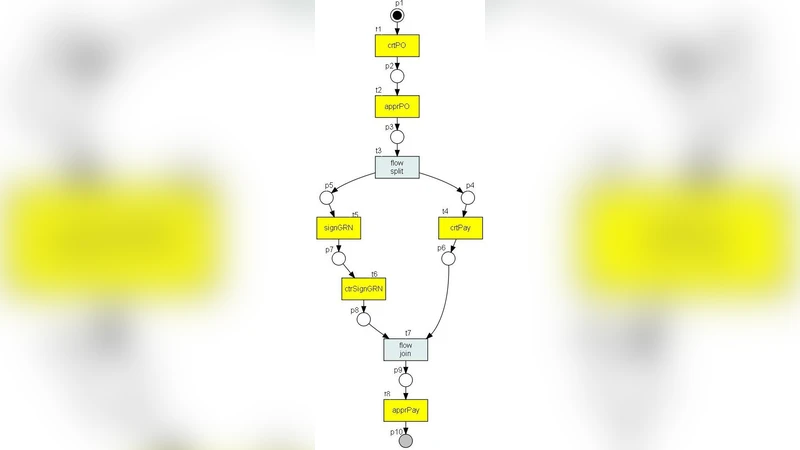
A prototype tool implementing the entire pipeline—parsing BPEL and RBAC specifications, performing the logical encoding, invoking an SMT solver, and presenting results—is built and evaluated on a realistic case study: a digital contract‑signing service inspired by an industrial partner. The service consists of four phases (contract creation, signing request, signature verification, final storage) and involves three roles (author, verifier, administrator). Initial experiments reveal that the tool can answer reachability queries in an average of 3.2 seconds (worst‑case under 8 seconds) while consuming less than 200 MB of memory, demonstrating that the approach is practical for real‑world workloads. Moreover, the tool discovers a subtle policy error in the original configuration—allowing the verifier role to read the contract content before signing—producing a concrete violating trace. After correcting the policy, a re‑run confirms that all specified security properties hold.
The technical contributions of the paper are threefold. First, it provides a unified formal model (BPEL‑RBAC) that captures both workflow semantics and access‑control constraints, bridging a gap that has traditionally separated process verification from security analysis. Second, it shows how to systematically reduce the verification problem to a decidable SMT‑solvable fragment, guaranteeing theoretical decidability while retaining expressive power sufficient for realistic BPEL constructs (sequences, parallel flows, conditional branches, loops). Third, it introduces practical optimizations—pre‑processing of role hierarchies, extraction of invariants, and partial‑order reduction of transition rules—to mitigate state‑space explosion, thereby achieving performance levels suitable for integration into development pipelines.
The authors also discuss limitations. The current encoding assumes a static set of roles and permissions; dynamic policy updates or runtime role creation are not yet supported. Data‑flow aspects that involve unbounded data structures or complex arithmetic are abstracted away, which may lead to over‑approximation in some scenarios. Future work is outlined to incorporate richer data‑flow analysis, support for dynamic RBAC extensions, and scalability studies on large‑scale micro‑service ecosystems.
In conclusion, the paper demonstrates that automated, SMT‑based validation of security‑sensitive BPEL services is both theoretically feasible and practically viable. By integrating workflow and access‑control specifications into a single decidable logical model, the approach enables developers to detect subtle security violations early in the design phase, reducing the risk of costly post‑deployment patches. The prototype’s successful application to an industrial‑grade digital contract‑signing service suggests that the methodology can be extended to other domains such as cloud orchestration, IoT service composition, and enterprise‑level business process management, where security and correctness must be guaranteed simultaneously.
Comments & Academic Discussion
Loading comments...
Leave a Comment