A Cyber Security Study of a SCADA Energy Management System: Stealthy Deception Attacks on the State Estimator
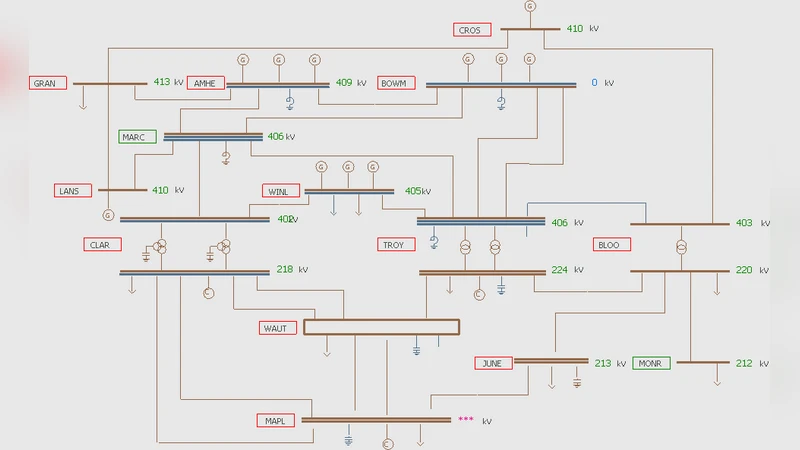
The electrical power network is a critical infrastructure in today’s society, so its safe and reliable operation is of major concern. State estimators are commonly used in power networks, for example, to detect faulty equipment and to optimally route power flows. The estimators are often located in control centers, to which large numbers of measurements are sent over unencrypted communication channels. Therefore cyber security for state estimators becomes an important issue. In this paper we analyze the cyber security of state estimators in supervisory control and data acquisition (SCADA) for energy management systems (EMS) operating the power network. Current EMS state estimation algorithms have bad data detection (BDD) schemes to detect outliers in the measurement data. Such schemes are based on high measurement redundancy. Although these methods may detect a set of basic cyber attacks, they may fail in the presence of an intelligent attacker. We explore the latter by considering scenarios where stealthy deception attacks are performed by sending false information to the control center. We begin by presenting a recent framework that characterizes the attack as an optimization problem with the objective specified through a security metric and constraints corresponding to the attack cost. The framework is used to conduct realistic experiments on a state-of-the-art SCADA EMS software for a power network example with 14 substations, 27 buses, and 40 branches. The results indicate how state estimators for power networks can be made more resilient to cyber security attacks.
💡 Research Summary
The paper investigates the cyber‑security vulnerability of state estimators used in supervisory control and data acquisition (SCADA) energy‑management systems (EMS) that monitor and control electric power networks. State estimation is a cornerstone of modern grid operation: it aggregates a large number of remote measurements (bus voltages, line flows, etc.) to produce a consistent picture of the system’s operating point, which is then used for fault detection, optimal power flow, and other critical functions. Because most measurements are transmitted over unencrypted channels to a central control center, an adversary who can inject false data may manipulate the estimator’s output without being noticed.
Current EMS implementations rely on Bad Data Detection (BDD) schemes that compute a weighted residual vector (r = W(z - H\hat{x})) and compare its norm to a threshold (\tau). The underlying assumption is that the measurement set is highly redundant; any single corrupted measurement will cause a large residual and be flagged. This works for naïve attacks that tamper with a few measurements arbitrarily. However, an intelligent attacker who knows the measurement matrix (H) and the BDD parameters can deliberately craft a deception vector (a) such that the altered measurement vector (z’ = z + a) satisfies (|W(z’ - H\hat{x})| \le \tau). In other words, the attack is “stealthy” – it stays under the detection radar while steering the estimated state toward a malicious target.
To formalize this threat, the authors adopt a recent optimization‑based attack framework. The attacker solves a constrained optimization problem:
\
Comments & Academic Discussion
Loading comments...
Leave a Comment