A Survey on Wireless Sensor Network Security
Wireless sensor networks (WSNs) have recently attracted a lot of interest in the research community due their wide range of applications. Due to distributed nature of these networks and their deployment in remote areas, these networks are vulnerable to numerous security threats that can adversely affect their proper functioning. This problem is more critical if the network is deployed for some mission-critical applications such as in a tactical battlefield. Random failure of nodes is also very likely in real-life deployment scenarios. Due to resource constraints in the sensor nodes, traditional security mechanisms with large overhead of computation and communication are infeasible in WSNs. Security in sensor networks is, therefore, a particularly challenging task. This paper discusses the current state of the art in security mechanisms for WSNs. Various types of attacks are discussed and their countermeasures presented. A brief discussion on the future direction of research in WSN security is also included.
💡 Research Summary
The surveyed paper provides a comprehensive overview of security challenges and solutions in Wireless Sensor Networks (WSNs), emphasizing the unique constraints that differentiate these networks from traditional wired or wireless systems. Because sensor nodes are typically low‑cost, battery‑powered devices with limited processing, memory, and communication bandwidth, the authors argue that conventional security mechanisms—such as heavyweight public‑key cryptography, frequent key exchanges, and extensive authentication protocols—are often infeasible in practice.
The authors first categorize threats using a four‑layer model (Physical, Data Link, Network, Application). At the physical layer, attacks include node capture, tampering, and electromagnetic interference, all of which can directly compromise hardware and expose cryptographic material. The data‑link layer is vulnerable to eavesdropping, frame injection, replay attacks, and denial‑of‑service (DoS) attacks that flood the medium. Network‑layer attacks are the most extensively studied and comprise sinkhole, wormhole, blackhole, grayhole, and routing manipulation attacks that aim to disrupt or misdirect traffic. At the application layer, privacy breaches and data integrity violations are highlighted, especially in mission‑critical deployments such as battlefield monitoring.
To counter these threats, the paper surveys three major families of defense mechanisms: (1) lightweight cryptographic primitives, (2) key management and distribution schemes, and (3) intrusion detection and resilience techniques. For cryptography, the authors discuss symmetric‑key block ciphers optimized for constrained hardware (e.g., PRESENT, KATAN, and reduced‑round AES‑128 variants) and hash‑based message authentication codes (HMAC, CMAC). They also review elliptic‑curve cryptography (ECC) adaptations that reduce key sizes to 160‑224 bits, making public‑key operations marginally affordable for certain nodes.
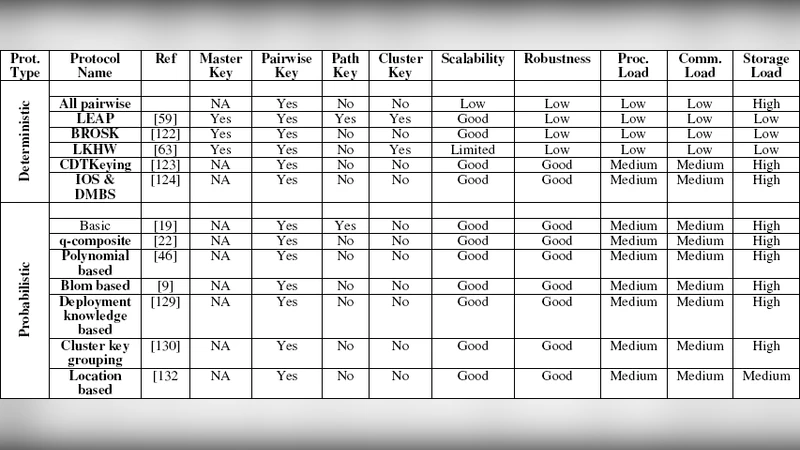
Key management is identified as a critical bottleneck. Pre‑shared key (PSK) approaches are simple but do not scale well. The paper describes key‑pool based probabilistic key predistribution, where each node stores a random subset of keys from a large pool and establishes secure links through shared keys. Dynamic key renewal mechanisms that exploit node mobility, environmental entropy (e.g., temperature‑based randomness), and routing‑path‑derived keys are also examined. The authors stress that any key‑management protocol must balance security freshness against the energy cost of re‑keying.
Intrusion detection and resilience are treated as complementary to cryptographic protection. Collaborative neighbor‑based anomaly detection, Bayesian inference models, and lightweight machine‑learning classifiers are surveyed for detecting routing anomalies or abnormal traffic patterns. Multi‑path routing and redundant data aggregation are recommended to maintain connectivity when a subset of nodes is compromised or disabled. For fault tolerance, the paper discusses node duplication, data replication, and lightweight distributed consensus protocols (e.g., PBFT variants) that can survive node failures while preserving data integrity.
A central theme throughout the survey is the security‑energy trade‑off. The authors present quantitative analyses showing that increasing security parameters—such as more frequent key updates or stronger encryption—can dramatically shorten network lifetime due to higher power consumption. Consequently, they propose an adaptive security framework that monitors residual energy, traffic load, and perceived threat level to dynamically adjust security settings (e.g., selecting between AES‑128 and a lighter cipher, or varying the key‑refresh interval).
Looking forward, the paper outlines several promising research directions. Quantum‑resistant cryptography, particularly lattice‑based schemes, is highlighted as a long‑term necessity, though further work is needed to reduce computational overhead. Machine‑learning‑driven real‑time intrusion detection must address the scarcity of labeled data and the need for ultra‑low‑power inference engines. Finally, the authors explore the integration of blockchain or distributed ledger technologies to provide decentralized trust, immutable audit trails, and automated node revocation. They suggest lightweight consensus mechanisms (e.g., Proof‑of‑Authority adaptations) and smart‑contract‑based key management as ways to eliminate single points of failure inherent in traditional key‑distribution servers.
In conclusion, the survey underscores that WSN security is not a single‑layer problem but a holistic system design challenge that intertwines cryptography, key management, routing protocols, and energy awareness. By cataloguing existing attacks, evaluating current countermeasures, and identifying gaps in scalability, resilience, and adaptability, the paper offers a valuable roadmap for researchers and practitioners aiming to secure the next generation of sensor‑rich, mission‑critical applications.