Digital Identity in The Absence of Authorities: A New Socio-Technical Approach
On the Internet large service providers tend to control the digital identities of users. These defacto identity authorities wield significant power over users, compelling them to comply with non-negotiable terms, before access to services is granted. In doing so, users expose themselves to privacy risks, manipulation and exploitation via direct marketing. Against this backdrop, the emerging areas of Digital Ecosystems and user-centric identity emphasise decentralised environments with independent self-determining entities that control their own data and identity. We show that recent advances in user-centric identity, federated identity and trust have prepared the ground for decentralised identity provisioning. We show how social trust, rather than blind deference to authorities, can provide a basis for identity, where risks can be weighed and compared rather than merely accepted. Fundamentally, we are considering the move from authority-centric centralised identity provisioning to user-centric distributed identity provisioning. Finally, we highlight the potential impacts of distributed identity provisioning in the Information Society and give a brief roadmap for its general implementation and adoption.
💡 Research Summary
The paper begins by diagnosing a fundamental problem in today’s Internet ecosystem: large service providers act as de‑facto identity authorities, forcing users to accept non‑negotiable terms and surrender personal data before they can access services. This authority‑centric model concentrates identity data in centralized repositories, exposing users to privacy breaches, manipulation, and a loss of control over their digital personas. The authors argue that such a model is increasingly untenable in an era that values user autonomy, data sovereignty, and transparent governance.
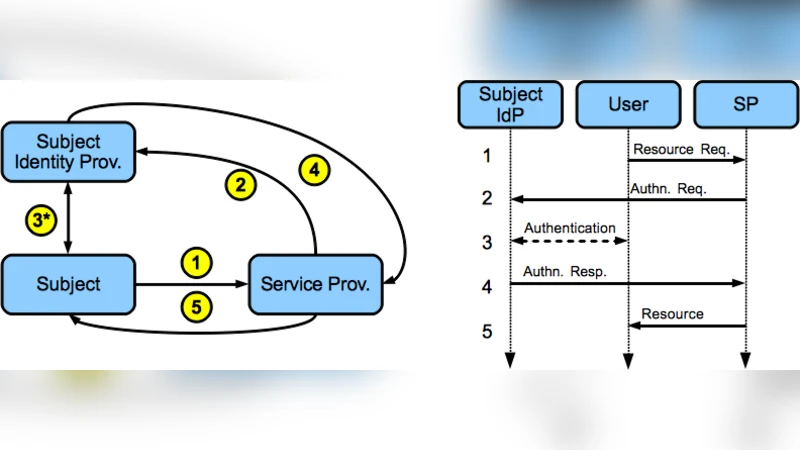
Against this backdrop, the authors review recent advances in user‑centric identity, federated identity, and trust frameworks that collectively lay the groundwork for a decentralized identity provisioning paradigm. They note that while federated identity reduces the number of credentials a user must manage, it still relies on a central Identity Provider (IdP). User‑centric identity, on the other hand, empowers individuals to own and manage their identifiers, but practical deployment has been hampered by the lack of robust, interoperable technical foundations.
The core contribution of the paper is the proposal of a “Social‑Trust‑Based Identity” (STBI) model that replaces blind reliance on centralized authorities with a dynamic, reputation‑driven trust network. The model leverages three key technological pillars:
-
Distributed Ledger Technologies (DLT) and Decentralized Identifiers (DIDs) – DIDs enable the creation of globally unique identifiers without a central registrar, while DLT provides immutable, auditable records of identifier creation, updates, and revocation.
-
Zero‑Knowledge Proofs (ZKPs) – ZKPs allow users to prove possession of attributes (e.g., age over 18, citizenship) without revealing the underlying data, thereby achieving selective disclosure and minimizing data leakage.
-
Dynamic Trust Scoring – Trust is quantified through a score that aggregates past interactions, transaction histories, peer endorsements, and reputation signals. Smart contracts automatically compute, update, and decay these scores, ensuring that trust reflects recent behavior and that malicious actors are gradually isolated.
In the STBI architecture, each participant maintains a local cryptographic key pair. The public key is linked to a DID stored on a blockchain. When a service (the “Verifier”) requests proof of a particular attribute, the user’s wallet generates a ZKP that satisfies the verifier’s policy while exposing only the minimal required claim. The verifier also queries the trust network to retrieve the user’s current trust score; if the score exceeds a pre‑defined threshold, the verifier proceeds with the transaction. This dual‑layer verification (cryptographic proof + trust score) replaces the traditional “identity assertion” issued by a central IdP.
The paper further details a Trust Propagation Algorithm that spreads trust across the network. Direct trust relationships are weighted by interaction frequency, transaction value, and explicit feedback. Indirect trust is derived through transitive paths, with a decay factor that reduces influence over longer chains. The algorithm includes safeguards against Sybil attacks by limiting the impact of newly created identities and by requiring multi‑party endorsement for high‑value trust updates.
Key security considerations are addressed through a Social Recovery mechanism. Should a user lose access to their private key, a set of pre‑selected “Recovery Agents”—trusted peers within the network—can collectively re‑issue a new key pair after satisfying a multi‑signature threshold. This eliminates the single point of failure inherent in centralized password‑reset services while preserving user autonomy.
Beyond technical design, the authors explore the broader economic and societal implications of decentralized identity. By decoupling identity verification from data disclosure, users can monetize their personal data on emerging data marketplaces, setting price points and usage conditions themselves. Moreover, the STBI model can mitigate digital exclusion: individuals in regions lacking formal state‑issued IDs can bootstrap a digital identity through community‑based trust, gaining access to essential services such as banking, healthcare, and education.
Implementation is mapped out in a three‑phase roadmap:
-
Phase 1 – Pilot & Standards Alignment: Deploy pilot projects using existing DID specifications (W3C) and ZKP libraries (e.g., zk‑SNARKs, Bulletproofs). Establish a consortium of early adopters (e.g., fintech, e‑government, NGOs) to test interoperability and refine trust scoring parameters.
-
Phase 2 – Open‑Source Ecosystem & Scaling: Release the trust scoring engine and recovery protocol as open‑source modules, encouraging third‑party integration. Conduct large‑scale simulations to stress‑test the trust propagation algorithm and to fine‑tune decay factors, thresholds, and Sybil‑resistance mechanisms.
-
Phase 3 – Regulatory Alignment & Commercial Roll‑out: Engage with data‑protection authorities (e.g., GDPR bodies, national privacy commissions) to develop legal frameworks that recognize decentralized identifiers as valid proof of identity. Partner with major service providers to embed STBI verification into existing onboarding flows, thereby achieving mass adoption.
The authors conclude that moving from authority‑centric, centralized identity provisioning to a user‑centric, socially‑trusted, distributed model can simultaneously enhance privacy, empower data ownership, and foster inclusive digital participation. The proposed architecture is technically feasible, aligns with emerging standards, and offers a clear, phased pathway toward real‑world deployment.
Comments & Academic Discussion
Loading comments...
Leave a Comment