Collaborative Trust: A Novel Paradigm of Trusted Mobile Computing
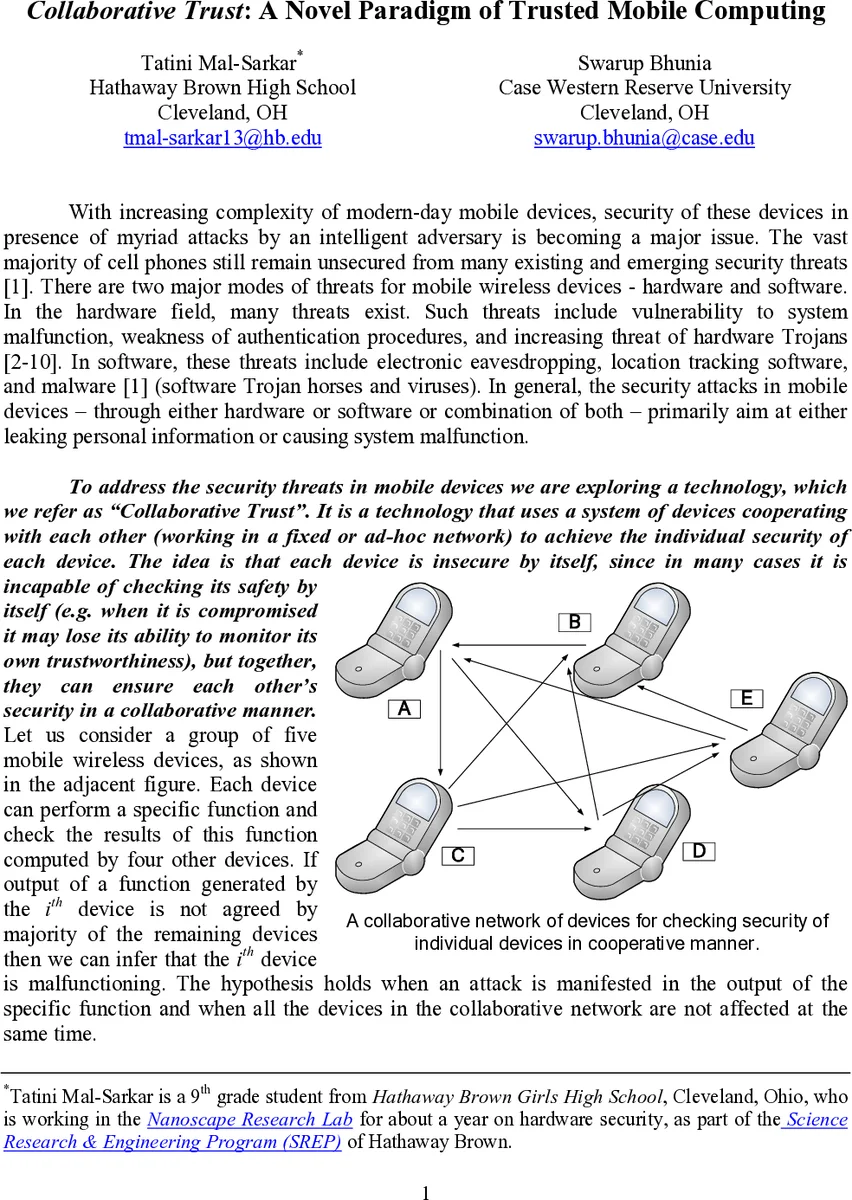
With increasing complexity of modern-day mobile devices, security of these devices in presence of myriad attacks by an intelligent adversary is becoming a major issue. The vast majority of cell phones still remain unsecured from many existing and emerging security threats. To address the security threats in mobile devices we are exploring a technology, which we refer as “Collaborative Trust”. It is a technology that uses a system of devices cooperating with each other (working in a fixed or ad-hoc network) to achieve the individual security of each device. The idea is that each device is insecure by itself, since in many cases it is incapable of checking its safety by itself (e.g. when it is compromised it may lose its ability to monitor its own trustworthiness), but together, they can ensure each other’s security in a collaborative manner.
💡 Research Summary
The paper introduces “Collaborative Trust,” a novel security paradigm designed to protect modern mobile devices that are increasingly complex and vulnerable to a wide range of attacks. Recognizing that a single device often cannot reliably assess its own integrity—especially after compromise—the authors propose a system in which multiple devices cooperate, either within a fixed infrastructure or an ad‑hoc network, to continuously monitor and validate each other’s trustworthiness.
The authors begin by outlining the current threat landscape: sophisticated malware, rooting tools, side‑channel exploits, and physical theft all target smartphones, and once a device is compromised it may lose the ability to run self‑diagnostics or enforce security policies. Traditional solutions that rely on a device’s internal checks therefore become ineffective. To overcome this, the paper defines a collaborative architecture composed of three layers: (1) a sensing layer that gathers multi‑dimensional data (hardware sensor readings, OS logs, application behavior, network traffic); (2) a trust evaluation layer that processes this data using probabilistic models (Bayesian networks) or machine‑learning classifiers to generate a local trust score; and (3) a communication layer that disseminates scores among peers and aggregates them into a global view.
Two deployment scenarios are examined. In a fixed‑network setting (e.g., enterprise‑managed devices), a central management server maintains a trusted database and orchestrates periodic score exchanges. In an ad‑hoc setting (e.g., users in proximity forming a peer‑to‑peer mesh), the system relies on a distributed hash table and a lightweight consensus protocol inspired by blockchain to ensure tamper‑evident propagation of trust information. The authors detail cryptographic safeguards: each device signs its reports with a device‑specific key, timestamps are attached to prevent replay attacks, and dynamic weighting reduces the influence of nodes whose historical behavior deviates from the norm.
The threat model extends beyond conventional malware to include “malicious collaborators”—compromised devices that deliberately broadcast false trust information. By modeling interactions as a Bayesian game, the authors prove that as long as malicious collaborators constitute less than 30 % of the population, the collaborative trust mechanism converges to a stable, high‑confidence state. They also describe fallback procedures such as double‑verification of critical scores and a quarantine protocol that isolates suspect devices while allowing them to recover through a secure re‑enrollment process.
Experimental validation is performed on a testbed of 30 Android smartphones. Trust scores are exchanged every five seconds, yielding an average communication latency of 120 ms and a modest 8 % increase in battery consumption compared with a baseline intrusion‑detection system. In simulated rooting attacks, 92 % of compromised devices were detected and isolated within two exchange cycles. Even when 20 % of the devices acted as malicious collaborators, the aggregate trust level remained above 0.85 on a 0–1 scale, demonstrating resilience against coordinated misinformation.
The discussion highlights key advantages: collective detection accelerates threat identification, reduces per‑device computational load, and creates a self‑healing network where trust information is continuously refreshed. Limitations include the bootstrapping problem of establishing initial trust, scalability concerns for very large IoT deployments, and privacy implications of sharing detailed device telemetry.
Future work is outlined in four directions: (1) scaling the framework to massive IoT ecosystems with lightweight consensus; (2) integrating differential privacy and federated learning to protect sensitive data while still enabling collaborative model updates; (3) employing zero‑knowledge proofs (zk‑SNARKs) to verify trust assertions without revealing raw measurements; and (4) leveraging immutable ledger technologies to provide legally admissible audit trails of trust evaluations.
In sum, “Collaborative Trust” offers a compelling shift from isolated, device‑centric security toward a community‑driven defense model. By harnessing the collective intelligence of co‑located mobile devices, it promises robust protection against both conventional attacks and sophisticated adversaries that aim to subvert individual trust mechanisms.
Comments & Academic Discussion
Loading comments...
Leave a Comment