Analyzing Network Coding Gossip Made Easy
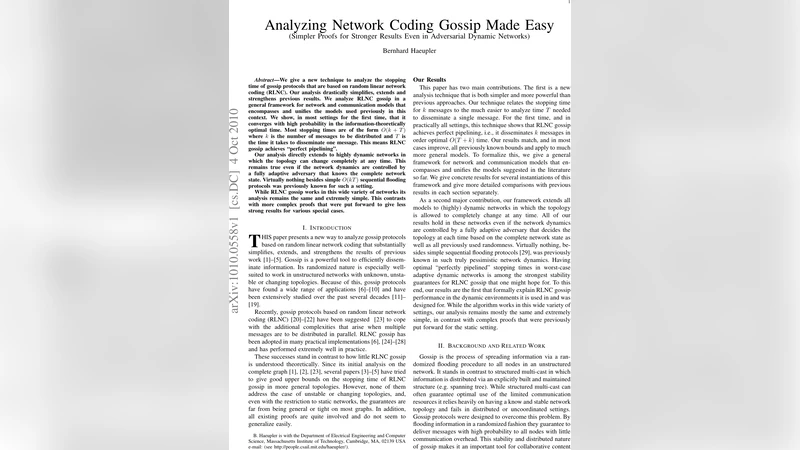
We give a new technique to analyze the stopping time of gossip protocols that are based on random linear network coding (RLNC). Our analysis drastically simplifies, extends and strengthens previous results. We analyze RLNC gossip in a general framework for network and communication models that encompasses and unifies the models used previously in this context. We show, in most settings for the first time, that it converges with high probability in the information-theoretically optimal time. Most stopping times are of the form O(k + T) where k is the number of messages to be distributed and T is the time it takes to disseminate one message. This means RLNC gossip achieves “perfect pipelining”. Our analysis directly extends to highly dynamic networks in which the topology can change completely at any time. This remains true even if the network dynamics are controlled by a fully adaptive adversary that knows the complete network state. Virtually nothing besides simple O(kT) sequential flooding protocols was previously known for such a setting. While RLNC gossip works in this wide variety of networks its analysis remains the same and extremely simple. This contrasts with more complex proofs that were put forward to give less strong results for various special cases.
💡 Research Summary
This paper introduces a remarkably simple yet powerful analytical technique for the stopping time of gossip protocols that employ Random Linear Network Coding (RLNC). The authors develop a unified framework that captures a broad spectrum of network and communication models, ranging from static graphs to highly dynamic topologies that may be altered arbitrarily by a fully adaptive adversary in every round, provided the network remains connected.
The core of the new analysis is a shift from tracking the growth of each node’s coefficient subspace (Y_v) to monitoring its orthogonal complement (Y_v^{\perp}). A node “knows” a vector (\mu) if its subspace is not orthogonal to (\mu); this notion is weaker than having (\mu) in the subspace but sufficient for information propagation. Lemma 4.2 shows that when a node that knows (\mu) transmits, the receiving node learns (\mu) with probability (1-1/q), where (q) is the field size (the analysis holds for any prime power, and the hardest case (q=2) already yields strong results). Because the set of nodes that know a given (\mu) evolves as a monotone Markov process, its expected cover time (T) can be bounded, and the tail of the distribution decays exponentially.
The authors then apply a union bound over all (q^k) non‑zero vectors in (\mathbb{F}_q^k). By choosing (t = O(T + k)) rounds, every vector spreads with high probability, which implies that all (k) original messages are decoded with probability (1-\delta). This yields the elegant “perfect pipelining” result: the total dissemination time is essentially the sum of the single‑message flooding time (T) and the number of messages (k), i.e., (O(T + k)).
The framework is instantiated for several concrete settings:
- Static networks – The analysis recovers and often improves upon prior bounds, eliminating the need for intricate graph‑specific arguments.
- Random edge‑failure or random neighbor models – The same (O(T + k)) bound holds, with (T) reflecting the expected time for a single message to flood under the given stochastic connectivity.
- Adversarial dynamic networks – Extending the pessimistic model of Kuhn, Lynch, and Oshman (where an adaptive adversary may rewire the entire network each round), the authors prove that RLNC gossip still achieves (O(T + k)) dissemination, dramatically outperforming the naïve sequential flooding approach that only guarantees (O(kT)).
The paper also discusses the impact of the field size (q). Larger fields increase the per‑transmission success probability, but the results are already optimal for the minimal field (q=2), which is attractive for implementation because packets consist of simple XORs.
In comparison with earlier works (
Comments & Academic Discussion
Loading comments...
Leave a Comment