Entanglement-assisted communication of classical and quantum information
We consider the problem of transmitting classical and quantum information reliably over an entanglement-assisted quantum channel. Our main result is a capacity theorem that gives a three-dimensional achievable rate region. Points in the region are ra…
Authors: Min-Hsiu Hsieh, Mark M. Wilde
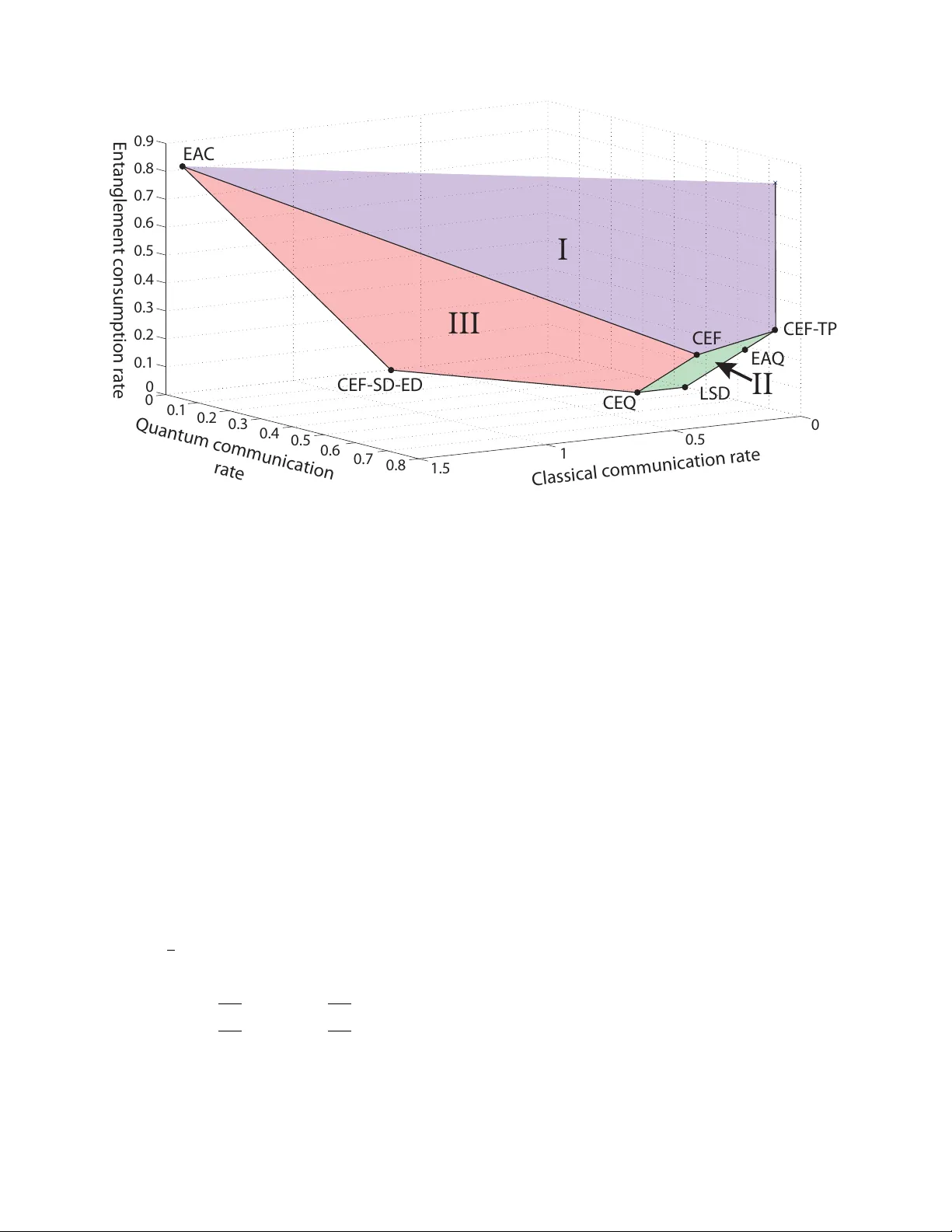
1 Entanglement-assisted communication of classical and quantum information Min-Hsiu Hsieh and Mark M. W ilde Abstract —W e consider the problem of transmitting classical and quantum information r eliably over an entanglement-assisted quantum channel. Our main result is a capacity theorem that gives a three-dimensional achievable rate region. Points in the region are rate triples , consisting of the classical communication rate, the quantum communication rate, and the entanglement consumption rate of a particular coding scheme. The crucial protocol in achieving the boundary points of the capacity r egion is a pr otocol that we name the classically-enhanced father protocol . The classically-enhanced father protocol is more general than other protocols in the family tree of quantum Shannon theoretic protocols, in the sense that sev eral pre viously known quantum protocols ar e now child protocols of it. The classically-enhanced father protocol also shows an improv ement over a time-sharing strategy for the case of a qubit dephasing channel—this result justifies the need for simultaneous coding of classical and quan- tum inf ormation over an entanglement-assisted quantum channel. Our capacity theorem is of a multi-letter nature (requiring a limit over many uses of the channel), but it reduces to a single- letter characterization for at least three channels: the completely depolarizing channel, the quantum erasur e channel, and the qubit dephasing channel. Index T erms —quantum Shannon theory , entanglement-assisted quantum channel, entanglement-assisted classical-quantum cod- ing, classically-enhanced father protocol I . I N T RO D U C T I O N The communication of information over a noisy quantum channel is a fundamental task in quantum communication theory . A sender may wish to transmit classical informa- tion, quantum information, or both. The Holev o-Schumacher- W estmoreland (HSW) coding theorem giv es an achiev able rate at which a sender can transmit classical data to a recei ver if she transmits the classical information over a noisy quantum chan- nel [1], [2]. The HSW theorem generalizes Shannon’ s classical channel coding theorem [3] to the quantum setting. The Lloyd- Shor-De vetak (LSD) coding theorem giv es an achiev able rate at which a sender can transmit quantum data to a receiv er through a quantum channel [4], [5], [6]. Devetak and Shor followed up on these results by determining achiev able rates at which a sender can simultaneously transmit both classical and quantum information over a quantum channel [7]. The na ¨ ıve scheme is to employ a time-sharing strategy , where a sender uses an HSW code for a fraction of the transmitted qubits and an LSD code for the other fraction. The Dev etak-Shor Min-Hsiu Hsieh is with the ERA TO-SORST Quantum Computation and Information Project, Japan Science and T echnology Agency , 5-28-3, Hongo, Bunkyo-ku, T okyo, Japan 113-0033. Mark M. Wilde was originally a visiting researcher with the Centre for Quantum T echnologies, National University of Singapore, 3 Science Driv e 2, Singapore 117543 at the beginning of this project, and he is now a postdoctoral fellow with the School of Computer Science, McGill University , Montreal, Canada H3A 2A7 (E-mail: minhsiuh@gmail.com and mwilde@gmail.com) coding strategy outperforms the na ¨ ıve time-sharing strategy , at least when the noisy channel is the qubit dephasing channel [8]. This result demonstrates the need to consider non-trivial coding schemes when communicating more than one resource. A sender can exploit a quantum channel alone, as in the abov e examples, or she can exploit assisting resources as well. Examples of such assisting resources are a static resource shared with the receiver , as in the case of common ran- domness, secret key , or entanglement, or a dynamic resource connecting the sender to the receiv er , as in the case of a noiseless classical or quantum side channel. Assisting a quantum channel with noiseless resources some- times improv es communication rates. The simplest and most striking example of this phenomenon occurs when a noise- less ebit assists a noiseless qubit channel. The super-dense coding protocol outlines a simple method to transmit two classical bits ov er a noiseless qubit channel assisted by an ebit [9]. This protocol beats the Holevo bound [8], which limits an unassisted noiseless qubit channel to transmit no more than one classical bit. The super-dense coding protocol then led Bennett et al. to explore if one could improve the classical capacity of a noisy quantum channel by assisting it with unlimited entanglement [10], [11]. They confirmed their intuition by proving a channel coding theorem that gi ves an entanglement-assisted classical transmission rate higher than that without assistance. Shor then refined this result by determining trade-offs between the classical communication rate and the entanglement consumption rate [12]. Quantum information theorists have since organized pro- tocols that exploit the different resources of quantum com- munication, classical communication, and entanglement into a family tree [13], [14], [15], [16]. One member of the family tree is the father pr otocol [13], [14]. The father protocol is so named because it generates sev eral “child” protocols using the theory of resource inequalities [13], [14]. Dev etak et al. exploited the father protocol to demonstrate trade-of fs between the quantum communication rate and the entanglement con- sumption rate over an entanglement-assisted quantum channel [13]. An important natural question, in light of the aforemen- tioned trade-off solutions for two of the three noiseless re- sources, is then how one might combine all three different resources. Pre vious work has addressed trade-offs for the task of remotely preparing quantum states with the aid of classical communication, quantum communication, and entanglement [17], but no one has yet considered the triple trade-of fs for channel coding. In this article, we conduct an in vestigation of the trade-of fs for channel coding both quantum and classical information 2 ov er a quantum channel assisted by noiseless entanglement. W e prov e the entanglement-assisted classical and quantum capacity theorem, that gives achiev able rates for this task. W e extend the family tree of quantum Shannon theory by dev eloping the classically-enhanced father protocol . 1 This protocol is more general than any of the existing protocols in the tree and achiev es rates in the three-dimensional capacity region. W e dub this protocol the “classically-enhanced father protocol” because it is an extension of the father protocol, and it generates fiv e child protocols in the sense of Refs. [13], [14]. T wo of its child protocols are classically-enhanced quan- tum communication [7] and entanglement-assisted classical communication [10], [11], [12] (we detail the others in Sec- tion VI-F). W e also demonstrate that isometric encodings are sufficient for achieving our rate formulas, resolving an open problem from Ref. [14]. A benefit of the classically-enhanced father protocol is that it inspires the design of classically-enhanced entanglement- assisted quantum error-correcting codes [19], [20]. W e giv e evidence in Section VIII-B that it is possible to reach the achiev able rates without encoding classical information into the entanglement shared between the sender and recei ver . W e structure this article as follows. In the next section, we give some definitions and establish notation used in the remainder of the article. Section III provides a description of a general protocol for communication of classical and quantum information with the assistance of entanglement. W e then state the main capacity theorem, Theorem 1, in Section IV and show how the classical capacity theorem [1], [2], the quan- tum capacity theorem [4], [5], [6], the classically-enhanced quantum capacity region [7], the father capacity region [14], and the entanglement-assisted classical capacity region [12] are all special cases of the entanglement-assisted classical and quantum capacity region. W e prove the con verse of Theorem 1 in Section V and prove the direct-coding part of Theorem 1 in Section VI. Section VI-F discusses the child protocols that the classically-enhanced father protocol generates. W e then giv e three example channels, the completely depolarizing channel, the quantum erasure channel, and the qubit dephasing channel, that admit a single-letter solution for the capacity region (meaning that we ha ve a complete understanding of the capacity region for these channels). W e also show that the classically-enhanced father protocol gives an impro vement ov er a time-sharing strategy when the noisy channel is the qubit dephasing channel. W e end by summarizing our results and by posing several open questions. I I . D E FI N I T I O N S A N D N OTA T I O N The ensemble p ( x ) , ψ AB E x x ∈X , where each state ψ AB E x is a pure tripartite state, is essential in the ensuing analysis of this article. The coher ent information I ( A i B ) ψ x of each state ψ AB E x in the ensemble is as follows: I ( A i B ) ψ x ≡ H ( B ) ψ x − H ( AB ) ψ x , 1 As a side note, we mention that former articles discuss the possibility of this protocol but never fully de veloped it [18], [14]. In addition, the current authors have both constructed “classically-enhanced father” error-correcting coding schemes for block codes [19] and for con volutional codes [20]. where H ( B ) ψ x is the von Neumann entropy of the reduction of the state ψ AB E x to the system B with a similar definition for H ( AB ) ψ x . The quantum mutual information I ( A ; B ) ψ x of each state ψ AB E x is as follows: I ( A ; B ) ψ x ≡ H ( A ) ψ x + I ( A i B ) ψ x . W e can classically correlate states in some system X with each state ψ AB E x to produce an augmented ensemble n p ( x ) , | x i h x | X ⊗ ψ AB E x o x ∈X , where the set {| x i} x ∈X is some preferred orthonormal basis for the auxiliary system X . The expected density operator of this augmented ensemble is the follo wing classical-quantum state: σ X AB E ≡ X x ∈X p ( x ) | x i h x | X ⊗ ψ AB E x . The Holevo information of the classical variable X with the quantum system B is I ( X ; B ) σ . For the special case of a classical system X , taking the expectation of the above en- tropic quantities with respect to the density p ( x ) giv es the re- spectiv e conditional entropy H ( A | X ) σ , conditional coherent information I ( A i B | X ) σ , and conditional mutual information I ( A ; B | X ) σ : H ( A | X ) σ ≡ X x ∈X p ( x ) H ( A ) ψ x , I ( A i B | X ) σ ≡ X x ∈X p ( x ) I ( A i B ) ψ x , I ( A ; B | X ) σ ≡ X x ∈X p ( x ) I ( A ; B ) ψ x . One can easily prove that I ( A i B | X ) σ = I ( A i B X ) σ . W e use the notation I ( A i B X ) σ for conditional coherent information in what follo ws. The above definitions lead to the following useful identities: H ( A | X ) σ = 1 2 I ( A ; B | X ) σ + 1 2 I ( A ; E | X ) σ , (1) I ( A i B X ) σ = 1 2 I ( A ; B | X ) σ − 1 2 I ( A ; E | X ) σ . (2) Proving the above identities is a simple matter of noting that the von Neumann entropy is equal for the reduced systems of a pure bipartite state. Adding the above identities gi ves the following one: H ( A | X ) σ + I ( A i B X ) σ = I ( A ; B | X ) σ . (3) The chain rule for quantum mutual information proves to be useful as well: I ( AX ; B ) σ = I ( A ; B | X ) σ + I ( X ; B ) σ . (4) All of the abov e information quantities possess operational interpretations in the theorems in this article. A noisy quantum channel N A 0 → B acts as a completely- positiv e trace-preserving (CPTP) map. It takes a quantum system A 0 as an input and produces a noisy output quantum system B . A conditional quantum encoder E M A → B , or conditional quantum channel [21], is a collection E A → B m m of CPTP 3 maps. Its inputs are a classical system M and a quantum system A and its output is a quantum system B . A classical- quantum state ρ M A , where ρ M A ≡ X m p ( m ) | m i h m | M ⊗ ρ A m , can act as an input to the conditional quantum encoder E M A → B . The action of the conditional quantum encoder E M A → B on the classical-quantum state ρ M A is as follows: E M A → B ρ M A = T r M ( X m p ( m ) | m i h m | M ⊗ E A → B m ρ A m ) . It is actually possible to write any quantum channel as a conditional quantum encoder when its input is a classical- quantum state [21]. In this article, a conditional quantum encoder functions as the sender Alice’ s encoder of classical and quantum information. A quantum instrument D A → B M is a CPTP map whose input is a quantum system A and whose outputs are a quantum system B and a classical system M [14], [21]. A collection D A → B m m of completely-positiv e trace-reducing maps spec- ifies the instrument D A → B M . The action of the instrument D A → B M on an arbitrary input state ρ is as follo ws: D A → B M ρ A = X m D A → B m ρ A ⊗ | m i h m | M . (5) T racing out the classical register M gi ves the induced quantum operation D A → B where D A → B ρ A ≡ X m D A → B m ρ A . This sum map is trace preserving: T r ( X m D A → B m ρ A ) = 1 . W e can think of the following quantity p m | ρ A ≡ T r D A → B m ρ A , as a conditional probability p m | ρ A of recei ving the classical message m when the state ρ A is input. In this article, a quantum instrument functions as Bob’ s decoder of classical and quantum information. W e abbreviate a capacity r egion by the noiseless resources in volv ed: classical communication (C), quantum communica- tion (Q), or entanglement (E), but we abbreviate a pr otocol with a different name corresponding either to its in ventors or an appropriate acronym. For example, we speak of the C, Q, or CE capacity theorems for classical communication, quantum communication, and entanglement-assisted classical communication, respectiv ely , but the corresponding protocols are Holev o-Schumacher-W estmoreland coding (HSW), Lloyd- Shor-De vetak coding (LSD), and entanglement-assisted clas- sical coding (EAC). W e note some other points before beginning. The trace norm k A k 1 of an operator A is as follows: k A k 1 ≡ T r n √ A † A o . The maximally entangled state on system T A and T B is Φ T A T B . The omission of a superscript implies a reduced state, e.g., the state Φ T A is the reduced state of Φ T A T B on T A . Y ard’ s thesis [21] provides a good introduction to quantum Shannon theory , and we point the reader there for properties such as strong subadditivity [22] and the quantum data processing inequality [23]. I I I . A G E N E R A L P RO TO C O L F O R E N T A N G L E M E N T - A S S I S T E D C O M M U N I C A T I O N O F C L A S S I C A L A N D Q UA N T U M I N F O R M AT I O N W e begin by defining a general protocol for entanglement- assisted communication of classical and quantum information (EA CQ) for a noisy quantum channel connecting a sender Alice to a recei ver Bob . Alice would like to communicate two items to Bob: 1) An arbitrary quantum state ρ A 1 in a system A 1 with dimension 2 nQ . 2) One of 2 nC classical messages. Alice and Bob also share entanglement in the form of a maximally entangled state Φ T A T B prior to communication. Alice possesses the system T A , Bob possesses the system T B , and the dimension of each system is 2 nE . W e can think of this state as possessing nE ebits of entanglement because it is equiv alent by local isometries to nE “gold standard” ebits in the state | Φ + i AB ≡ ( | 00 i AB + | 11 i AB ) / √ 2 . Alice performs a conditional quantum encoder E M A 1 T A → A 0 n that encodes both her quantum systems A 1 and T A and the classical message in system M . The encoding operation E M A 1 T A → A 0 n prepares a system A 0 n for input to a noisy quantum channel N A 0 n → B n . The channel N A 0 n → B n represents n independent uses of the noisy quantum channel N A 0 → B : N A 0 n → B n ≡ N A 0 → B ⊗ n . She then sends her state through the quantum channel N A 0 n → B n . Bob receives the system B n and performs a decoding instrument D B n T B → B 1 B E ˆ M on the channel output B n and his half of the entanglement T B . The instrument D B n T B → B 1 B E ˆ M produces a system B 1 with the quantum information that Alice sent, a classical register ˆ M containing Alice’ s classical message, and another system B E that does not contain any useful information. Bob should be able to identify the classical message with high probability and recover the state ρ A 1 with high fidelity . Figure 1 provides a detailed illustration of this protocol. It is useful to consider the isometric extension U A 0 → B E N of the channel N A 0 → B where Alice controls the channel input system A 0 , Bob has access to the channel output system B , and the environment Eve has access to the system E . 2 For an independent and identically distributed (IID) channel N A 0 n → B n as defined abov e, we write its isometric extension as U A 0 n → B n E n N . Also, it is useful to think of Alice’ s quantum system ρ A 1 as a restriction of some pure state ϕ ˆ RA 1 where Alice does not have access to the purification system ˆ R . 2 It should be clear from context when E refers to Ev e’ s system or when it refers to the entanglement consumption rate. 4 M A1 R T A T B A’ A’ A’ E E E B B B B B B B1 E ve A lic e B ob R ef er enc e t t f U D E U U E E E ^ Fig. 1. (Color online) The abov e figure depicts a general EA CQ protocol. A sender Alice would like to communicate the quantum information in system A 1 and the classical information in system M . Her system T A represents shared maximal entanglement with the receiv er’ s system T B . Alice encodes her information and uses the noisy channel a large number of times. The en vironment Eve obtains part of the output and the receiv er Bob obtains the other part. Bob combines his receiv ed systems with his half of the entanglement and performs a decoding operation to recov er both the classical and quantum information. W e formalize the EA CQ quantum information processing task as follows. Define an ( n, C , Q, E , ) EA CQ code by • Alice’ s conditional quantum encoder E M A 1 T A → A 0 n with encoding maps {E A 1 T A → A 0 n m } m ∈ [2 nC ] . This encoder en- codes both her quantum information and classical in- formation. Define the following states for each classical message m : ω ˆ RA 0 n T B m ≡ E A 1 T A → A 0 n m ( ϕ ˆ RA 1 ⊗ Φ T A T B ) , (6) where the dimension of system A 1 is 2 nQ and the dimension of system T A is 2 nE . The density operator that includes the classical register M and averages ov er all classical messages is as follows: ω M ˆ RA 0 n T B ≡ 1 | M | X m | m i h m | M ⊗ ω ˆ RA 0 n T B m , (7) where | M | is the size of the classical register M . The output of the channel given that Alice sent classical message m is then as follows: ω ˆ RB n E n T B m ≡ U A 0 n → B n E n N ω ˆ RA 0 n T B m . The av erage output of the channel is as follows: ω M ˆ RB n E n T B ≡ U A 0 n → B n E n N ω M ˆ RA 0 n T B . (8) • Bob’ s decoding instrument D B n T B → B 1 B E ˆ M , whose ac- tion is defined in (5), is a collection of completely- positiv e trace-reducing maps {D B n T B → B 1 B E m } m ∈ [2 nC ] . The decoding instrument decodes both the quantum in- formation and classical information that Alice sends. The density operator corresponding to Bob’ s output state is as follows: ω M ˆ RB 1 B E ˆ M E n ≡ D B n T B → B 1 B E ˆ M ω M ˆ RB n E n T B . The classical probability of successful transmission of mes- sage m is as follows: Pr { ˆ M = m | M = m } = T r { ( D B n T B → B 1 B E m )( ω ˆ RB n E n T B m ) } , where ˆ M denotes the random v ariable corresponding to Bob’ s receiv ed classical message. The final state on the reference system ˆ R and Bob’ s quantum system B 1 is Υ ˆ RB 1 where Υ ˆ RB 1 ≡ T r ˆ M B E E n {D B n T B → B 1 B E ˆ M ( ω ˆ RB n E n T B m ) } . For the ( n, C , Q, E , ) EACQ code to be “ -good, ” the following two conditions should hold for all classical messages m ∈ [2 nC ] : 1) Bob decodes any of the classical messages m with high probability Pr { ˆ M = m | M = m } ≥ 1 − , (9) 2) The state Υ ˆ RB 1 should be -close to the ideal state ϕ ˆ RB 1 ≡ id A 1 → B 1 ( ϕ ˆ RA 1 ) : Υ ˆ RB 1 − ϕ ˆ RB 1 1 ≤ , (10) so that Bob recovers the quantum information in system A 1 with high fidelity . A rate triple ( C, Q, E ) is achievable if there e xists an ( n, C − δ, Q − δ, E + δ, ) EA CQ code for any , δ > 0 and suf ficiently large n . The capacity region C ( N ) is a three-dimensional region containing all achiev able rate triples ( C, Q, E ) . I V . T H E E N TA N G L E M E N T - A S S I S T E D C L A S S I C A L A N D Q UA N T U M C A P AC I T Y T H E O R E M W e now state our main theorem: the entanglement-assisted classical and quantum capacity (CQE) theorem that inv olves all three noiseless resources. Theor em 1: The capacity re gion C CQE ( N ) of an entanglement-assisted quantum channel N for simultaneously transmitting both quantum information and classical information is equal to the following expression: C CQE ( N ) = ∞ [ k =1 1 k C (1) CQE ( N ⊗ k ) , (11) where the overbar indicates the closure of a set. The “one- shot” region C (1) CQE ( N ) is the union of the regions C (1) CQE ,σ ( N ) : C (1) CQE ( N ) ≡ [ σ C (1) CQE ,σ ( N ) , where C (1) CQE ,σ ( N ) is the set of all C , Q, E ≥ 0 , such that C + 2 Q ≤ I ( AX ; B ) σ , (12) Q ≤ I ( A i B X ) σ + E , (13) C + Q ≤ I ( X ; B ) σ + I ( A i B X ) σ + E . (14) The abo ve entropic quantities are with respect to a “one-shot” quantum state σ X AB E where σ X AB E ≡ X x p ( x ) | x i h x | X ⊗ U A 0 → B E N ( φ AA 0 x ) , (15) 5 E AC CEF-SD -ED CEQ LSD CEF E AQ CEF- TP En tanglemen t c onsumption r a t e Q uan tum c ommunica tion r a te Classical c ommunica tion r a t e I II 0.9 0.8 0.7 0.6 0.5 0.4 0.3 0.2 0.1 0 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 1.5 1 0.5 0 III Fig. 2. (Color online) An example of the one-shot, one-state achiev able region C (1) CQE, σ ( N ) corresponding to a state σ X ABE that arises from a qubit dephasing channel with dephasing parameter p = 0 . 2 . The state input to the channel N is σ X AA 0 , defined in (16). The plot features seven achiev able corner points of the one-shot, one-state region. W e can achie ve the con vex hull of these eight points by time-sharing any two different coding strate gies. W e can also achieve any point abov e an achievable point by consuming more entanglement than necessary . The seven achiev able points correspond to the father protocol (EA Q) [13], [14], the De vetak-Shor protocol for classically-enhanced quantum communication (CEQ) [7], Shor’ s protocol for entanglement-assisted classical communication with limited entanglement (EAC) [12], quantum communication (LSD) [4], [5], [6], combining CEF with entanglement distrib ution and super-dense coding (CEF-SD-ED) as detailed in Section VI-F, the classically-enhanced father protocol (CEF) outlined in Section VI, and combining the classically-enhanced father protocol with teleportation [24] (CEF-TP). Observe that we can obtain EA C by combining CEF with super-dense coding as detailed in Section VI-F, so that the points CEQ, CEF , EAC, and CEF-SD-ED all lie in plane III. Observe that we can obtain CEQ from CEF by entanglement distribution and we can obtain LSD from EA Q and EAQ from CEF-TP , both by entanglement distribution. Thus, the points CEF , CEQ, LSD, EA Q, and CEF-TP all lie in plane II. Finally , observe that we can obtain all corner points by combining CEF with the unit protocols in (61-63). This one-shot, one-state achiev able region for the state σ X ABE is tight. The bounds in (12-14) uniquely specify the respectiv e planes I-III. W e obtain the full achiev able re gion by taking the union ov er all states σ of the one-shot, one-state regions C (1) σ ( N ) and taking the regularization, as outlined in Theorem 1. The abov e region is a translation of the unit resource capacity region to the classically-enhanced father protocol. the states φ AA 0 x are pure, and it is sufficient to consider |X | ≤ min {| A 0 | , | B |} 2 + 1 by the method in Ref. [25]. The capacity region in Theorem 1 is a union of general polyhedra, each specified by (12-14), where the union is ov er all possible states of the form (15) and a potentially infinite number of uses of the channel. Figure 2 illustrates an example of the general polyhedron specified by (12-14), where the channel is the qubit dephasing channel 3 with dephasing parameter p = 0 . 2 , and the input state is σ X AA 0 ≡ 1 2 ( | 0 i h 0 | X ⊗ φ AA 0 0 + | 1 i h 1 | X ⊗ φ AA 0 1 ) , (16) where | φ 0 i AA 0 ≡ p 1 / 4 | 00 i AA 0 + p 3 / 4 | 11 i AA 0 , | φ 1 i AA 0 ≡ p 3 / 4 | 00 i AA 0 + p 1 / 4 | 11 i AA 0 . The state σ X AB E resulting from the channel is U A 0 → B E N ( σ X AA 0 ) where U N is an isometric e xtension of the qubit dephasing channel. The figure caption provides a 3 The action of the qubit dephasing channel with dephasing parameter p on a density operator ρ is ρ → (1 − p ) ρ + pZ ρZ . detailed explanation of the one-shot, one-state region C (1) CQE ,σ (note that Figure 2 displays the one-shot, one-state region and does not display the full capacity region). The above capacity region has the simple interpretation. In Ref. [26], we determined a unit resource capacity region. This unit resource region outlines what is achiev able if one does not possess a noisy channel, but only possesses the three noiseless resources of classical communication, quantum communication, and entanglement. There, we found that the optimal strategy is to combine teleportation, super -dense cod- ing, and entanglement distribution. Interestingly , the above set of inequalities demonstrates that the one-shot, one-state region is a translation of the unit resource capacity region to the classically-enhanced father protocol. Indeed, eliminating the entropic quantities from (12-14) re veals that the inequalities are the same as those that specify the unit resource capacity region. Proving that Theorem 1 holds consists of proving it in two steps, traditionally called the dir ect coding theorem and the con verse . For our case, the direct coding theor em proves that the region corresponding to the right hand side of (11) is an achiev able rate region. It constructs an EACQ protocol whose 6 rates are in the region of the right hand side of (11) and sho ws that its fidelity of quantum communication is high and its probability of error of classical communication is small. The con verse assumes that a good code with high fidelity and lo w probability of error exists and shows that the region on the right hand side of (11) bounds the achiev able rate region. W e prov e the conv erse in Section V and the direct coding theorem in Section VI. A. Special Cases of the Capacity Theorem W e first consider fiv e special cases of the abov e capacity theorem that arise when Q and E both v anish, C and E both vanish, or one of C , Q , or E v anishes. The first two cases cor- respond respectiv ely to the Holev o-Schumacher-W estmoreland coding theorem and the Lloyd-Shor -Dev etak coding theorem. Each of the other special cases traces out a two-dimensional achiev able rate region in the three-dimensional capacity re- gion. The five coding scenarios are as follows: 1) Classical communication (C) when there is no entangle- ment assistance or quantum communication [1], [2]. The achiev able rate region lies on the ( C , 0 , 0) ray extending from the origin. 2) Quantum communication (Q) when there is no entan- glement assistance or classical communication [4], [5], [6]. The achiev able rate region lies on the (0 , Q, 0) ray extending from the origin. 3) Entanglement-assisted quantum communication (QE) when there is no classical communication [13], [14]. The achiev able rate region lies in the (0 , Q, E ) quarter-plane of the three-dimensional region in (11). 4) Classically-enhanced quantum communication (CQ) when there is no entanglement assistance [7]. The achiev- able rate region lies in the ( C , Q, 0) quarter-plane of the three-dimensional region in (11). 5) Entanglement-assisted classical communication (CE) when there is no quantum communication [12]. The achiev able rate region lies in the ( C, 0 , E ) quarter-plane of the three-dimensional region in (11). 1) Classical Capacity: The following theorem giv es the one-dimensional capacity region C C ( N ) of a quantum channel N for classical communication [1], [2]. Theor em 2: The classical capacity region C C ( N ) is giv en by C C ( N ) = ∞ [ k =1 1 k C (1) C ( N ⊗ k ) . (17) The “one-shot” region C (1) C ( N ) is the union of the regions C (1) C ,σ ( N ) , where C (1) C ,σ ( N ) is the set of all C ≥ 0 , such that C ≤ I ( X ; B ) σ + I ( A i B X ) σ . (18) The entropic quantity is with respect to the state σ X AB E in (15). The bound in (18) is a special case of the bound in (14) with Q = 0 and E = 0 . The abo ve characterization of the classical capacity region may seem slightly dif ferent from the original HSW characterization, until we make a few observations. First, we rewrite the coherent information I ( A i B X ) σ as H ( B | X ) σ − H ( E | X ) σ . Then I ( X ; B ) σ + I ( A i B X ) σ = H ( B ) σ − H ( E | X ) σ . Next, pure states of the form | ϕ i A 0 x are sufficient to attain the classical capacity of a quantum channel [12]. W e briefly recall this ar gument. An ensemble of the following form realizes the classical capacity of a quantum channel: ρ X A 0 ≡ X x p X ( x ) | x i h x | X ⊗ ρ A 0 x . This ensemble itself is a restriction of the ensemble in (15) to the systems X and A 0 . Each mix ed state ρ A 0 x admits a spectral decomposition of the form ρ A 0 x = P y p Y | X ( y | x ) ψ A 0 x,y where ψ A 0 x,y is a pure state. W e can define an augmented classical- quantum state θ X Y A 0 as follo ws: θ X Y A 0 ≡ X x,y p Y | X ( y | x ) p X ( x ) | x i h x | X ⊗ | y i h y | Y ⊗ ψ A 0 x,y , so that Tr Y { θ X Y A 0 } = ρ X A 0 . Sending the A 0 system of the states ρ X A 0 and θ X Y A 0 leads to the respectiv e states ρ X B and θ X Y B . Then the following equality and inequality hold: I ( X ; B ) ρ = I ( X ; B ) θ ≤ I ( X Y ; B ) θ , where the equality holds because T r Y { θ X Y A 0 } = ρ X A 0 and the inequality follows from quantum data processing. Redefin- ing the classical variable as the joint random variable X , Y rev eals that it is suf ficient to consider pure state ensembles for the classical capacity . Returning to our main argument, then H ( E | X ) σ = H ( B | X ) σ so that I ( X ; B ) σ + I ( A i B X ) σ = H ( B ) σ − H ( B | X ) σ = I ( X ; B ) σ for states of this form. Thus, the expression in (18) can nev er exceed the classical capacity and finds its maximum exactly at the Holev o information. 2) Quantum Capacity: The following theorem giv es the one-dimensional quantum capacity region C Q ( N ) of a quan- tum channel N [4], [5], [6]. Theor em 3: The quantum capacity region C Q ( N ) is given by C Q ( N ) = ∞ [ k =1 1 k C (1) Q ( N ⊗ k ) . (19) The “one-shot” region C (1) Q ( N ) is the union of the regions C (1) Q ,σ ( N ) , where C (1) Q ,σ ( N ) is the set of all Q ≥ 0 , such that Q ≤ I ( A i B X ) σ . (20) The entropic quantity is with respect to the state σ X AB E in (15) with the restriction that the density p ( x ) is degenerate. The bound in (20) is a special case of the bound in (13) with E = 0 . The other bounds in Theorem 1 are looser than the bound in (13) when C, E = 0 . 3) Entanglement-Assisted Quantum Capacity: The follo w- ing theorem giv es the two-dimensional entanglement-assisted quantum capacity region C QE ( N ) of a quantum channel N [13], [14]. 7 Theor em 4: The entanglement-assisted quantum capacity region C QE ( N ) is giv en by C QE ( N ) = ∞ [ k =1 1 k C (1) QE ( N ⊗ k ) . (21) The “one-shot” region C (1) QE ( N ) is the union of the regions C (1) QE ,σ ( N ) , where C (1) QE ,σ ( N ) is the set of all Q, E ≥ 0 , such that Q ≤ 1 2 I ( AX ; B ) σ , (22) Q ≤ E + I ( A i B X ) σ . (23) The entropic quantities are with respect to the state σ X AB E in (15) with the restriction that the density p ( x ) is degenerate. The bounds in (22) and (23) are a special case of the respectiv e bounds in (12) and (13) with C = 0 . The other bounds in Theorem 1 are looser than the bounds in (12) and (13) when C = 0 . Observe that the re gion is a union of general pentagons (see the QE -plane in Figure 2 for an example of one of these general pentagons in the union). 4) Classically-Enhanced Quantum Capacity: The follo w- ing theorem giv es the two-dimensional capacity region C CQ ( N ) for classically-enhanced quantum communication through a quantum channel N [7]. Theor em 5: The classically-enhanced quantum capacity re- gion C CQ ( N ) is giv en by C CQ ( N ) = ∞ [ k =1 1 k C (1) CQ ( N ⊗ k ) . (24) The “one-shot” region C (1) CQ ( N ) is the union of the regions C (1) CQ ,σ ( N ) , where C (1) CQ ,σ ( N ) is the set of all C, Q ≥ 0 , such that C + Q ≤ I ( X ; B ) σ + I ( A i B X ) σ , (25) Q ≤ I ( A i B X ) σ . (26) The entropic quantities are with respect to the state σ X AB E in (15). The bounds in (25) and (26) are a special case of the respectiv e bounds in (13) and (14) with E = 0 . Observe that the region is a union of trapezoids (see the C Q -plane in Figure 2 for an example of one of these rectangles in the union). The above characterization is a slightly improved charac- terization of the Dev etak-Shor region from Ref. [7]. Indeed, the one-shot, one-state region there was a union of rectangles giv en by the following set of inequalities: C ≤ I ( X ; B ) σ , (27) Q ≤ I ( A i B X ) σ . (28) These rectangles are inside the trapezoids abov e. Though, our characterization in (25-26) is the same as theirs when we consider the union over all the one-shot, one-state regions. 5) Entanglement-assisted Classical Capacity with Limited Entanglement: Theor em 6: The entanglement-assisted classical capacity region C CE ( N ) of a quantum channel N is C CE ( N ) = ∞ [ k =1 1 k C (1) CE ( N ⊗ k ) . (29) The “one-shot” region C (1) CE ( N ) is the union of the regions C (1) CE ,σ ( N ) , where C (1) CE ,σ ( N ) is the set of all C, E ≥ 0 , such that C ≤ I ( AX ; B ) σ , (30) C ≤ I ( X ; B ) σ + I ( A i B X ) σ + E . (31) where the entropic quantities are with respect to the state σ X AB E in (15). The bounds in (30) and (31) are a special case of the respectiv e bounds in (12) and (14) with Q = 0 . Observe that the region is a union of general polyhedra (see the CE-plane in Figure 2 for an example of one of these general polyhedra in the union). The above characterization of the CE achiev able region is again an improvement ov er the characterization in Refs. [11], [12], [14]. It specifies a union of general trapezoids. The region in Refs. [11], [12], [14] was a union of general rectangles of the form: C ≤ I ( AX ; B ) σ , (32) E ≥ H ( A | X ) σ . (33) These general rectangles are inside the above general trape- zoids (note that the bounds in (30-31) intersect at E = H ( A | X ) σ ), but the regions coincide when we take the union ov er all the one-shot, one-state regions. V . T H E C O N V E R S E P RO O F Our method for proving the con verse of Theorem 1 is to apply standard entropic bounds that are av ailable in Ref. [8]. W e first recall the Fannes inequality for continuity of en- tropy , the Alicki-Fannes inequality for continuity of coherent information, and another inequality of the Fannes class for continuity of quantum mutual information. Theor em 7 (F annes Inequality [27]): Suppose two states ρ A and σ A are close: ρ A − σ A 1 ≤ . Then their respective entropies are close: | H ( A ) ρ − H ( A ) σ | ≤ log | A | + H 2 ( ) . (34) | A | is the dimension of the system A and H 2 ( ) is the binary entropy function that has the property lim → 0 H 2 ( ) = 0 . Theor em 8 (Alicki-F annes Inequality [28]): Suppose two states ρ AB and σ AB are close: ρ AB − σ AB 1 ≤ . Then their respective coherent informations are close: | I ( A i B ) ρ − I ( A i B ) σ | ≤ 4 log | A | + 2 H 2 ( ) . (35) 8 Cor ollary 1: Suppose two states ρ AB and σ AB are close: ρ AB − σ AB 1 ≤ . Then their respecti ve quantum mutual informations are close: | I ( A ; B ) ρ − I ( A ; B ) σ | ≤ 5 log | A | + 3 H 2 ( ) . (36) Pr oof: The proof follows in two steps by applying Theo- rems 7 and 8. First, monotonicity of the trace distance under the discarding of subsystems implies that ρ A − σ A 1 ≤ . Theorem 7 then applies. The corollary then follows from the equality I ( A ; B ) = H ( A ) + I ( A i B ) and the triangle inequality . Con verse: Section III describes the most general EACQ protocol and this most general case is the one we consider in proving the con verse. Suppose Alice shares the maximally en- tangled state Φ ˆ RA 1 with the reference system ˆ R (the protocol should be able to transmit the entanglement in state Φ ˆ RA 1 with -accuracy if it can approximately transmit the entanglement with system ˆ R for any pure state on ˆ R and A 1 ). Alice also shares the maximally entangled state Φ T A T B with Bob . Alice combines her system A 1 of the quantum state Φ ˆ RA 1 with her system T A of the state Φ T A T B and the classical register M that contains her classical information. The most general encoding operation that she can perform on her three registers M , A 1 , and T A is a conditional quantum encoder E M A 1 T A → A 0 n consisting of a collection {E A 1 T A → A 0 n m } m of CPTP maps. For now , we assume this general form of the encoder b ut later show in Appendix E that it is only necessary to consider a collection of isometries. Each element E A 1 T A → A 0 n m of the conditional quantum encoder produces the following state: ω ˆ RA 0 n E 0 T B m ≡ U A 1 T A → A 0 n E 0 E m (Φ ˆ RA 1 ⊗ Φ T A T B ) , where we consider the isometric extension U A 1 T A → A 0 n E 0 E m of each element E A 1 T A → A 0 n m . The average density operator over all classical messages is then as follows: 1 | M | X m | m i h m | M ⊗ ω ˆ RA 0 n E 0 T B m . Alice sends the A 0 n system through the noisy channel U A 0 n → B n E n N , producing the following state: ω M ˆ RB n E n E 0 T B (37) ≡ 1 | M | X m | m i h m | M ⊗ U A 0 n → B n E n N ( ω ˆ RA 0 n E 0 T B m ) . Define A ≡ ˆ RT B so that the state in (37) is a particular n th extension of the state in (15). The above state is the state at time t in Figure 1. Bob receiv es the above state and performs a decoding instrument D B n T B → B 1 B E ˆ M . The protocol ends at time t f . Let ( ω 0 ) M ˆ RB 1 B E ˆ M E n E 0 be the state at time t f after Bob processes ω M ˆ RB n E n E 0 T B with the decoding instrument D B n T B → B 1 B E ˆ M . Suppose that an ( n, C − δ, Q − δ, E + δ, ) EA CQ protocol as gi ven abov e exists. W e prove that the following bounds apply to the elements of its rate triple ( C − δ, Q − δ, E + δ ) : C + 2 Q − δ ≤ 1 n I ( AM ; B n ) ω , (38) Q − δ ≤ 1 n I ( A i B n M ) ω + E , (39) C + Q − δ ≤ 1 n ( I ( M ; B n ) ω + I ( A i B n M ) ω ) + E , (40) for any , δ > 0 and all suf ficiently large n . In the ideal case, the identity quantum channel acts on system A 1 to produce the maximally entangled state Φ ˆ RB 1 . So for our case, the following inequality ( ω 0 ) ˆ RB 1 − Φ ˆ RB 1 1 ≤ (41) holds because the protocol is -good for quantum communica- tion according to the criterion in (10). Also, in the ideal case, the identity classical channel acts on system M to produce the maximally correlated state Φ M ˆ M where Φ M ˆ M ≡ 1 | M | X m | m ih m | M ⊗ | m ih m | ˆ M . (42) So for our case, the following inequality ( ω 0 ) M ˆ M − Φ M ˆ M 1 ≤ (43) holds because the protocol is -good for classical communica- tion according to the criterion in (9). W e first prove the upper bound in (38) on the classical and quantum rates. Shor’ s ver - sion [12] of the entanglement-assisted classical capacity theo- rem [10], [11] states that the rate I ( AM ; B n ) /n is achiev able and serves as a multi-letter upper bound. This bound implies that the unlimited entanglement-assisted quantum capacity is I ( AM ; B n ) / 2 n . If it were not so, then one could con vert all of the quantum communication to classical communication by super-dense coding and beat the rate I ( AM ; B n ) /n . But this result contradicts the optimality of the unlimited entanglement- assisted classical capacity . These two results imply the bounds C ≤ I ( AM ; B n ) /n and 2 Q ≤ I ( AM ; B n ) /n . But we can go further and prove that the sum rate is bounded as well. Suppose there exists a protocol that beats the sum rate in (38). With more entanglement, one could con vert all of the quantum communication to classical communication by super- dense coding. But this result again contradicts the optimality of the unlimited entanglement-assisted classical capacity . So the bound C + 2 Q − δ ≤ I ( AM ; B n ) ω /n holds. W e next pro ve the upper bound in (39) on the quantum communication rate: n ( Q − δ ) = I ( ˆ R i B 1 ) Φ ˆ RB 1 ≤ I ( ˆ R i B 1 ) ω 0 + 4 nQ + H 2 ( ) ≤ I ( ˆ R i B 1 M ) ω 0 + 4 nQ + H 2 ( ) ≤ I ( ˆ R i B n T B M ) ω + 4 nQ + H 2 ( ) ≤ I ( ˆ RT B i B n M ) ω + H ( T B | M ) ω + 4 nQ + H 2 ( ) ≤ I ( A i B n M ) ω + nE + 4 nQ + H 2 ( ) . (44) The first equality follows by e valuating the coherent informa- tion for the state Φ ˆ RB 1 . The first inequality follo ws from (41) 9 and the Alicki-Fannes inequality in Theorem 8. The second inequality is from strong subadditivity , and the third inequality is quantum data processing. The fourth inequality follows because H ( T B | B n M ) ≤ H ( T B | M ) (conditioning reduces entropy). The last inequality follows from the definition A ≡ ˆ RT B and the fact that H ( T B | M ) ω ≤ nE . The inequality in (39) follows by redefining δ as δ 0 ≡ δ + 4 Q + H 2 ( ) n . W e prov e the upper bound in (40) on the classical and quantum rates: n ( C + Q − δ ) = I ( M ; ˆ M ) Φ M ˆ M + I ( ˆ R i B 1 ) Φ ˆ RB 1 ≤ I ( M ; ˆ M ) ω 0 + I ( ˆ R i B 1 ) ω 0 + 5 nC + 4 nQ + 5 H 2 ( ) ≤ I ( M ; B n T B ) ω 0 + I ( ˆ R i B n T B M ) ω 0 + nδ 0 = I ( M ; B n ) ω 0 + I ( M ; T B | B n ) ω 0 + H ( B n T B | M ) ω 0 − H ( ˆ RB n T B | M ) ω 0 + nδ 0 = I ( M ; B n ) ω 0 + H ( T B | B n ) ω 0 + H ( B n | M ) ω 0 − H ( ˆ RB n T B | M ) ω 0 + nδ 0 ≤ I ( M ; B n ) ω 0 + H ( T B ) ω 0 + I ˆ RT B i B n M ω 0 + nδ 0 = I ( M ; B n ) ω 0 + I ( A i B n M ) ω 0 + nE + nδ 0 . The first equality follows because the mutual information I ( M ; ˆ M ) of the maximally correlated state Φ M ˆ M is equal to nC . The first inequality follo ws by applying (43) and Corollary 1 to the mutual information I ( M ; ˆ M ) , and (41) and the Alicki-Fannes’ inequality to the coherent information I ( ˆ R i B 1 ) . The second inequality follows by applying the quantum data processing inequality and strong subadditivity as we did in the proof of the pre vious bound and by defining δ 0 ≡ 5 C + 4 Q + 5 H 2 ( ) /n . The second and third equalities follow by manipulating entropies. The third inequality follo ws from the definition of coherent information and because con- ditioning does not increase entropy . The last inequality follows from the definition A ≡ ˆ RT B and because nE is the maximal value that H ( T B ) can take. V I . T H E D I R E C T C O D I N G T H E O R E M In this section, we prove the direct coding theorem for entanglement-assisted communication of classical and quan- tum information by gi ving a combination of strategies that can achieve the rates in Theorem 1. The most important dev el- opment is the introduction of the classically-enhanced father protocol and its corresponding proof in the next section. This protocol yields a corner point in the achiev able region (see, for example, the point labeled CEF in Figure 2). Section VI-F shows that combining this protocol with teleportation, super- dense coding, and entanglement distribution allows us to obtain all other corner points of the achiev able rate region. Thus, this protocol is the most general one available for the channel coding scenario. A. The Classically-Enhanced F ather Pr otocol W e can phrase the classically-enhanced father protocol as a r esour ce inequality (see Ref. [14] for the theory of resource inequalities): hN A 0 → B i + 1 2 I ( A ; E | X ) σ [ q q ] ≥ 1 2 I ( A ; B | X ) σ [ q → q ] + I ( X ; B ) σ [ c → c ] . (45) The precise statement of the classically-enhanced father re- source inequality is a statement of achiev ability . For any , δ > 0 and sufficiently large n , there exists a protocol that consumes n uses of the noisy channel N A 0 → B and consumes ≈ nI ( A ; E | X ) σ / 2 ebits. In doing so, the protocol communicates ≈ nI ( A ; B | X ) σ / 2 qubits with 1 − fidelity and ≈ nI ( X ; B ) σ classical bits with probability of error . The entropic quantities are with respect to the state σ X AB E in (15). The proof of the achiev ability of the classically-enhanced father protocol proceeds in several steps. W e first establish some definitions relev ant to an entanglement-assisted quantum code, or father code for short, and recall the direct coding theo- rem for entanglement-assisted quantum (EA Q) communication [13], [14], [15]. W e then define a random father code, gi ve a few relev ant definitions and properties, and prove a version of the EA Q coding theorem that applies to random father codes. In particular, we show random father codes exist whose expected channel input is close to a product state (similar to result of the random quantum coding theorem in Appendix D of Ref. [6]). W e follow this dev elopment by showing ho w to “paste” random father codes together so that the expected channel input of the pasted random code is close to a product state containing a classical message. A random classically- enhanced father code is then a collection of “pasted” father codes. The closeness of each expected channel input to a product state allows us to apply the HSW coding theorem [1], [2] so that Bob can decode the classical message while causing almost no disturbance to the encoded quantum infor- mation. Based on the classical message, Bob determines which random father code he should be decoding for . This method of efficiently coding classical and quantum information is the “piggybacking” technique introduced in Ref. [7] and applied again in Refs. [25], [29]. The final arguments consist of a series of Shannon-theoretic arguments of derandomization and expur gation. The result is a deterministic classically-enhanced father code that performs well and achiev es the rates in the capacity region in Theorem 1. B. F ather Codes The unencoded state of a father code is as follows | ϕ i ˆ RA 1 ⊗ | Φ i T A T B , (46) where | ϕ i ˆ RA 1 ≡ 2 nQ X k =1 α k | k i ˆ R | k i A 1 , | Φ i T A T B ≡ 1 √ 2 nE 2 nE X m =1 | m i T A | m i T B . 10 The isometric encoder E A 1 T A → A 0 n of the father code maps kets on the systems A 1 and T A as follo ws | φ k,m i A 0 n ≡ E A 1 T A → A 0 n | k i A 1 | m i T A , where the states | φ k,m i A 0 n are mutually orthogonal. Therefore, the encoder E A 1 T A → A 0 n maps the unencoded state in (46) to the follo wing encoded state: E A 1 T A → A 0 n | ϕ i ˆ RA 1 ⊗ | Φ i T A T B = 2 nQ X k =1 α k | k i ˆ R | φ k i A 0 n T B , where we define the states | φ k i A 0 n T B in the follo wing defini- tion. Definition 1: The set C ≡ {| φ k i A 0 n T B } k is a representation of the father code. The EA Q codewor ds are as follo ws: | φ k i A 0 n T B ≡ 1 √ 2 nE 2 nE X m =1 | φ k,m i A 0 n | m i T B . (47) The EA Q code density oper ator ρ A 0 n T B ( C ) is a uniform mixture of the EA Q codew ords: ρ A 0 n T B ( C ) ≡ 1 2 nQ 2 nQ X k =1 | φ k i h φ k | A 0 n T B . The channel input density operator ρ A 0 n ( C ) is the part of the code density operator ρ A 0 n T B ( C ) that is input to the channel: ρ A 0 n ( C ) ≡ T r T B n ρ A 0 n T B ( C ) o . The abov e definitions imply the following two results: ρ A 0 n T B ( C ) = E A 1 T A → A 0 n π A 1 ⊗ Φ T A T B , ρ A 0 n ( C ) = 1 2 n ( Q + E ) 2 nQ X k =1 2 nE X m =1 | φ k,m i h φ k,m | A 0 n . The direct coding theorem for entanglement-assisted quan- tum communication giv es a method for achieving the multi- letter quantum communication rate and entanglement con- sumption rate. Pr oposition 1 (EAQ Coding Theor em): Consider a quan- tum channel N A 0 → B and its isometric extension U A 0 → B E N . F or any , δ > 0 and all suf ficiently large n , there exists an ( n, ) entanglement-assisted quantum code defined by isometries ( E , D ) , such that the trace distance between the actual output ( D B n T B → B 1 B E ◦ U A 0 n → B n E n N ◦ E A 1 T A → A 0 n )( ϕ ˆ RA 1 ⊗ Φ T A T B ) , and the ideal decoupled output ϕ ˆ RB 1 ⊗ ρ E n B E , (48) is no larger than , for any state ϕ ˆ RA 1 with dimension 2 nQ in the system A 1 and any maximally entangled Φ T A T B equiv alent to nE ebits. The rate of quantum communication is Q − δ = 1 2 I ( A ; B ) φ provided that the rate of entanglement consumption is at least E + δ = 1 2 I ( A ; E ) φ . The entropic quantities are with respect to the following state: | φ i AB E ≡ U A 0 → B E N | ψ i AA 0 , (49) where | ψ i AA 0 is the purification of some state ρ A 0 . Pr oof: See Ref. [15]. C. Random F ather Codes W e cannot say much about the channel input density op- erator ρ A 0 n ( C ) for a particular EA Q code C . But we can say something about the expected channel input density operator of a random EA Q code C (where C itself becomes a random variable). Definition 2: A random EAQ code is an ensemble { p C , C } of codes where each code C occurs with probability p C . The expected code density operator ρ A 0 n T B is as follows: ρ A 0 n T B ≡ E C n ρ A 0 n T B ( C ) o . The expected channel input density operator ρ A 0 n is as fol- lows: ρ A 0 n ≡ E C n ρ A 0 n ( C ) o . A random EA Q code is “ ρ -like” if the expected channel input density operator is close to a tensor po wer of some state ρ : ρ A 0 n − ρ ⊗ n 1 ≤ . (50) It follo ws from the abov e definition that ρ A 0 n T B = X C p C ρ A 0 n T B ( C ) , ρ A 0 n = T r T B n ρ A 0 n T B o . W e no w state a version of the direct coding theorem that applies to random father codes. The proof shows that we can produce a random f ather code with an e xpected channel input density operator close to a tensor power state. Pr oposition 2: For any , δ > 0 and all sufficiently large n , there exists a random ρ A 0 -like EA Q code for a channel N A 0 → B . In particular , the random EA Q code has quan- tum rate 1 2 I ( A ; B ) φ − δ and entanglement consumption rate 1 2 I ( A ; E ) φ + δ . The entropic quantities are with respect to the state in (49) and the state ρ A 0 is that state’ s restriction to the system A 0 . Pr oof: The proof is in the Appendix A. D. Associating a Random F ather Code with a Classical String Suppose that we have an ensemble { p ( x ) , ρ x } x ∈X of quantum states. Let x n ≡ x 1 · · · x n denote a classical string generated by the density p ( x ) where each symbol x i ∈ X . Then there is a density operator ρ x n corresponding to the string x n where ρ x n ≡ n O i =1 ρ x i . Suppose that we label a random father code by the string x n and let ρ A 0 n x n denote its e xpected channel input density operator . Definition 3: A random father code is ( ρ x n ) -like if the expected channel input density operator ρ A 0 n x n is close to the state ρ x n : ρ A 0 n x n − ρ x n 1 ≤ . Pr oposition 3: Suppose we hav e an ensemble as above. Consider a quantum channel N A 0 → B with its isometric ex- tension U A 0 → B E N . Then there exists a random ( ρ x n ) -like 11 entanglement-assisted quantum code for the channel N A 0 → B for any , δ > 0 , for all sufficiently large n , and for any classical string x n in the typical set T X n δ [30]. Its quantum communication rate is I ( A ; B | X ) / 2 − c 0 δ and its entanglement consumption rate is I ( A ; E | X ) / 2 + c 00 δ for some constants c 0 , c 00 where the entropic quantities are with respect to the state in (15) with a trivial system E 0 . The state ρ x n is generated from the restriction of the ensemble { p ( x ) , φ AA 0 x } x ∈X to the A 0 system. The states φ AA 0 x in the ensemble correspond to the states φ AA 0 x in (15). Pr oof: The method of proof in volves “pasting” random father codes together . The proof is in the Appendix B. E. Construction of a Classically-Enhanced F ather Code The HSW coding theorem gi ves an achiev able method for sending classical information ov er a noisy quantum channel. The crucial property that we exploit is that it uses a product- state input for sending classical information. This tensor- product structure is what allows us to “piggyback” classical information onto father codes. Pr oposition 4 (HSW Coding Theor em [1], [2]): Consider an input ensemble { p ( x ) , ρ A 0 x } that giv es rise to a classical- quantum state σ X B where σ X B ≡ X x ∈X p ( x ) | x i h x | X ⊗ N A 0 → B ( ρ A 0 x ) . Let C = I ( X ; B ) σ − c 0 δ for an y δ > 0 and for some constant c 0 . Then for all > 0 and for all suf ficiently large n , there exists a classical encoding map f : 2 nC → T X n δ , and a decoding PO VM Λ B n ≡ (Λ B n m ) m ∈ [2 nC ] , that allows Bob to decode any classical message m ∈ [2 nC ] with high probability: T r { τ B n m Λ B n m } ≥ 1 − . The density operators τ B n m are the channel outputs τ B n m ≡ N A 0 n → B n ( ρ A 0 n f ( m ) ) , (51) and the channel input states ρ A 0 n x n are a tensor product of states in the ensemble: ρ A 0 n x n ≡ n O i =1 ρ A 0 x i . W e are now in a position to prov e the direct coding part of the classically-enhanced father capacity theorem. The proof is similar to that in Ref. [7]. Dir ect Coding Theor em: Define the classical mes- sage set 2 nC , the classical encoding map f , the channel output states τ B n m , and the decoding PO VM Λ B n as in Proposition 4. In voking Proposition 3, we know that for each m ∈ [2 nC ] , there e xists a random ( ρ A 0 n f ( m ) ) -like fa- ther code C m whose probability density is p C m . The ran- dom father code C m has encoding-decoding isometry pairs ( E A 1 T A → A 0 n C m , D B n T B → B 1 B E C m ) for each of its realizations. It transmits n [ I ( A ; B | X ) / 2 − c 0 δ ] qubits provided Alice and Bob share at least n [ I ( A ; E | X ) / 2 + c 00 δ ] ebits. Let C denote the random classically-enhanced father code that is the collection of random father codes {C m } m ∈ [2 nC ] . W e first prove that the expectation of the classical error probability for message m is small. The expectation is with respect the random father code C m . Let τ B n C m denote the channel output density operator corresponding to the father code C m : τ B n C m ≡ T r T B n N A 0 n → B n E A 1 T A → A 0 n C m ( π A 1 ⊗ Φ T A T B ) o . Let τ B n m denote the expected channel output density operator of the random father code C m : τ B n m ≡ E C m n τ B n C m o = X C m p C m τ B n C m . The follo wing inequality holds ρ A 0 n f ( m ) − ρ A 0 n f ( m ) 1 ≤ |X | because the random father code C m is ( ρ A 0 n f ( m ) ) -like. Then the expected channel output density operator τ B n m is close to the tensor product state τ B n m in (51): τ B n m − τ B n m 1 ≤ |X | , (52) because the trace distance is monotone under the quantum operation N A 0 n → B n . It then follows that the PO VM element Λ B n m has a high probability of detecting the expected channel output density operator τ B n m : T r { Λ B n m τ B n m } ≥ T r { Λ B n m τ B n m } − τ B n m − τ B n m 1 ≥ 1 − − |X | . (53) The first inequality follows from the following lemma [21] that holds for any two quantum states ρ and σ and a positi ve operator Π where 0 ≤ Π ≤ I : T r { Π ρ } ≥ Tr { Π σ } − k ρ − σ k 1 . The second inequality follows from Proposition 4 and (52). W e define Bob’ s decoding instrument D B n T B → B 1 B E ˆ M C for the random classically-enhanced father code C as follows: D B n T B → B 1 B E ˆ M C ρ B n T B ≡ X m D B n T B → B 1 B E C m q Λ B n m ρ B n T B q Λ B n m ⊗ | m i h m | ˆ M , where D B n T B → B 1 B E C m is the decoding isometry for the father code C m and each map D B n T B → B 1 B E C m ( p Λ B n m ρ p Λ B n m ) is trace reducing. The induced quantum operation corresponding to this instrument is as follows: D B n T B → B 1 B E C ( ρ ) = T r ˆ M n D B n T B → B 1 B E ˆ M C ( ρ ) o . Let p e ( C m ) denote the classical error probability for each classical message m of the classically-enhanced father code C : p e ( C m ) ≡ 1 − Pr { M 0 = m | M = m } = 1 − Tr D B n T B → B 1 B E C m q Λ B n m τ B n C m q Λ B n m . 12 Then by the above definition, (53), and the fact that the trace does not change under the isometry D B n T B → B 1 B E C m , it holds that the expectation of the classical error probability p e ( C m ) with respect to the random father code C m is lo w: E C m { p e ( C m ) } ≤ (1 + |X | ) . (54) W e no w prove that the expectation of the quantum error is small (the expectation is with respect to the random father code C m ). Input the state Φ ˆ RA 1 ⊗ Φ T A T B to the encoder E A 1 T A → A 0 n C m followed by the channel N A 0 n → B n . The resulting state is an extension Ω ˆ RT B B n C m of τ B n C m : Ω ˆ RT B B n C m ≡ N A 0 n → B n E A 1 T A → A 0 n C m (Φ ˆ RA 1 ⊗ Φ T A T B ) . Let Ω ˆ RT B B n m denote the expectation of Ω ˆ RT B B n C m with respect to the random code C m : Ω ˆ RT B B n m ≡ E C m n Ω ˆ RT B B n C m o . It follows that Ω ˆ RT B B n m is an extension of τ B n m . The following inequality follo ws from (53): T r { Ω ˆ RT B B n m Λ B n m } ≥ 1 − (1 + |X | ) . (55) The above inequality is then suf ficient for us to apply a modified version of the gentle measurement lemma (Lemma 1 in the Appendix C) so that the follo wing inequality holds E C m q Λ B n m Ω ˆ RT B B n C m q Λ B n m − Ω ˆ RT B B n C m 1 ≤ p 8(1 + |X | ) . (56) Monotonicity of the trace distance giv es an inequality for the trace-reducing maps of the quantum decoding instrument: E C m D B n T B → B 1 B E C m p Λ B n m Ω ˆ RT B B n C m p Λ B n m − D B n T B → B 1 B E C m Ω ˆ RT B B n C m 1 ≤ p 8(1 + |X | ) . (57) The follo wing inequality also holds E C m D B n T B → B 1 B E C Ω ˆ RT B B n C m − D B n T B → B 1 B E C m p Λ B n m Ω ˆ RT B B n C m p Λ B n m 1 ≤ E C m X m 0 6 = m D B n T B → B 1 B E C m 0 q Λ B n m 0 Ω ˆ RT B B n C m q Λ B n m 0 1 = E C m X m 0 6 = m q Λ B n m 0 Ω ˆ RT B B n C m q Λ B n m 0 1 = E C m X m 0 6 = m T r n Λ B n m 0 Ω ˆ RT B B n C m o = 1 − Tr Λ B n m Ω ˆ RT B B n m ≤ (1 + |X | ) . (58) The first inequality follows from definitions and the triangle inequality . The first equality follows because the trace distance is inv ariant under isometry . The second equality follows be- cause the operator Λ B n m Ω ˆ RT B B n C m is positiv e. The third equality follows from some algebra, and the second inequality follows from (53). The fidelity of quantum communication for all classical messages m and codes C m is high F D B n T B → B 1 B E C m Ω ˆ RT B B n C m , Φ ˆ RB 1 ≥ 1 − because each code C m in the random father code is good for quantum communication. It then follows that E C m n D B n T B → B 1 B E C m Ω ˆ RT B B n C m − Φ ˆ RB 1 1 o ≤ 2 √ (59) because of the relation between the trace distance and fidelity [21]. Application of the triangle inequality to (59), (58), and (57) gives the following bound on the e xpected quantum error E C m { q e ( C m ) } ≤ 0 (60) where 0 ≡ (1 + |X | ) + p 8(1 + |X | ) + 2 √ , and where we define the quantum error q e ( C m ) of the code C m as follo ws: q e ( C m ) ≡ D B n T B → B 1 B E C Ω ˆ RT B B n C m − Φ ˆ RB 1 1 . The abov e random classically-enhanced father code relies on Alice and Bob having access to a source of common randomness. W e no w show that the y can eliminate the need for common randomness and select a good classically-enhanced father code C that has a low quantum error q e ( C m ) and low classical error p e ( C m ) for all classical messages m in a large subset of 2 nC . By the bounds in (54) and (60), the following bound holds for the expectation of the av eraged summed error probabilities: E C m ( 1 2 nC X m p e ( C m ) + q e ( C m ) ) ≤ 0 + (1 + |X | ) . If the above bound holds for the expectation over all random codes, it follows that there exists a particular classically- enhanced father code C = {C m } m ∈ [2 nC ] with the following bound on its averaged summed error probabilities: 1 2 nC X m p e ( C m ) + q e ( C m ) ≤ 0 + (1 + |X | ) . W e fix the code C and expurgate the worst half of the father codes—those father codes with classical messages m that hav e the highest value of p e ( C m ) + q e ( C m ) . This derandom- ization and expurgation yields a classically-enhanced father code that has each classical error p e ( C m ) and each quantum error q e ( C m ) upper bounded by 2 ( 0 + (1 + |X | ) ) for the remaining classical messages m . This expur gation decreases the classical rate by a negligible factor of 1 n . Note that the abov e proof is a scheme for entanglement transmission. This task is equi valent to the task of subspace transmission (quantum communication) by the methods in Ref. [31]. 13 F . Child Pr otocols W e detail fiv e protocols that are children of the classically- enhanced father protocol in the sense of Ref. [14]. Recall the classically-enhanced father resource inequality in (45). Recall the three respectiv e unit resource inequalities for teleportation, super-dense coding, and entanglement distrib ution: 2 [ c → c ] + [ q q ] ≥ [ q → q ] , (61) [ q q ] + [ q → q ] ≥ 2 [ c → c ] , (62) [ q → q ] ≥ [ q q ] . (63) W e can first append entanglement distribution to the classically-enhanced father resource inequality . This append- ing gives rise to the classically-enhanced quantum commu- nication protocol in Ref. [7]. The de velopment proceeds as follows: hN A 0 → B i + 1 2 I ( A ; E | X ) [ q q ] ≥ 1 2 I ( A ; B | X ) [ q → q ] + I ( X ; B ) [ c → c ] = 1 2 I ( A ; E | X ) + I ( A i B X ) [ q → q ] + I ( X ; B ) [ c → c ] ≥ 1 2 I ( A ; E | X ) [ q q ] + I ( A i B X ) [ q → q ] + I ( X ; B ) [ c → c ] , where the first inequality is the classically-enhanced father resource inequality , the first equality exploits the identity in (2), and the last inequality follows from entanglement distri- bution. By the cancellation lemma (Lemma 4.6 of Ref. [14]), the follo wing resource inequality holds hN A 0 → B i + o [ q q ] ≥ I ( A i B X ) [ q → q ] + I ( X ; B ) [ c → c ] , (64) where o [ q q ] represents a sublinear amount of entanglement. The abov e resource inequality is equiv alent to the classically- enhanced quantum communication protocol in Ref. [7] (mod- ulo the sublinear entanglement). Combining the above re- source inequality further with entanglement distribution gives the classically-enhanced entanglement generation protocol from Ref. [7]: hN A 0 → B i + o [ q q ] ≥ I ( A i B X ) [ q q ] + I ( X ; B ) [ c → c ] . W e can combine the classically-enhanced father protocol with super-dense coding and entanglement distribution. Let CEF-SD-ED denote the resulting protocol. The dev elopment proceeds by first using qubits at a rate 1 2 H ( A | X ) for entan- glement distribution: hN A 0 → B i + 1 2 I ( A ; E | X ) [ q q ] ≥ 1 2 I ( A ; B | X ) [ q → q ] + I ( X ; B ) [ c → c ] = 1 2 H ( A | X ) + 1 2 I ( A i B X ) [ q → q ] + I ( X ; B ) [ c → c ] ≥ 1 2 H ( A | X ) [ q q ] + 1 2 I ( A i B X ) [ q → q ] + I ( X ; B ) [ c → c ] After this step, the above protocol is equiv alent to the follow- ing one: hN i + o [ q q ] ≥ 1 2 I ( A i B X ) ([ q q ]+[ q → q ])+ I ( X ; B ) [ c → c ] , so that it has generated entanglement at a net rate of 1 2 I ( A i B X ) ebits. W e can then further combine with super- dense coding to achieve the protocol CEF-SD-ED: hN A 0 → B i + o [ q q ] ≥ I ( A i B X ) [ c → c ] + I ( X ; B ) [ c → c ] . W e can combine the classically-enhanced father protocol with super-dense coding to get Shor’ s entanglement-assisted classical (EA C) communication protocol [12]: hN A 0 → B i + H ( A | X ) [ q q ] = hN A 0 → B i + 1 2 I ( A ; E | X ) [ q q ] + 1 2 I ( A ; B | X ) [ q q ] ≥ 1 2 I ( A ; B | X ) [ q → q ] + I ( X ; B ) [ c → c ] + 1 2 I ( A ; B | X ) [ q q ] ≥ I ( X ; B ) [ c → c ] + I ( A ; B | X ) [ c → c ] = I ( AX ; B ) [ c → c ] . (65) The first equality uses the identity in (1). The first inequality uses the classically-enhanced father resource inequality . The second inequality uses super -dense coding, and the last equal- ity uses the chain-rule identity in (4). The above rates are the same as those in Refs. [12], [14]. T eleportation is the last unit resource inequality with which we can combine the classically-enhanced father protocol. Let CEF-TP (classically-enhanced father combined with tele- portation) denote the resulting protocol. Consider that the classically-enhanced father protocol generates classical com- munication at a rate I ( X ; B ) . Alice and Bob can teleport quantum information if they have an extra I ( X ; B ) / 2 ebits of entanglement. The development proceeds as follo ws: hN A 0 → B i + 1 2 I ( A ; E | X ) [ q q ] + 1 2 I ( X ; B ) [ q q ] ≥ 1 2 I ( A ; B | X ) [ q → q ] + I ( X ; B ) [ c → c ] + 1 2 I ( X ; B ) [ q q ] ≥ 1 2 I ( A ; B | X ) [ q → q ] + 1 2 I ( X ; B ) [ q → q ] = 1 2 I ( AX ; B ) [ q → q ] . W e apply teleportation to get the second inequality and the chain rule in (4) to get the last equality . W e can rewrite the abov e protocol as follo ws: hN A 0 → B i + 1 2 ( I ( A ; E | X ) + I ( X ; B )) [ q q ] ≥ 1 2 I ( AX ; B ) [ q → q ] . This protocol is the same as the father protocol if random variable X has a degenerate distribution. V I I . S I N G L E - L E T T E R E X A M P L E S Theorem 1 is a general theorem that determines the capacity region of any entanglement-assisted channel for classical and quantum communication. Unfortunately , the theorem is of a multi-letter nature, implying that it is an intractable problem to compute the capacity region corresponding to an arbitrary channel. 14 In the forthcoming subsections, we provide se veral exam- ples of channels for which we can exactly compute their corresponding capacity regions. The first example is the trivial completely depolarizing channel (the channel that replaces the input state with the maximally mixed state). W e find this ex- ample interesting despite its triviality because it coincides with our results in Ref. [26]. The second example is the quantum erasure channel [32]. The adv antage of the quantum erasure channel is that we can apply simple reasoning to determine the outer bound of its corresponding capacity region. W e then show that the inner bound corresponding to the achie vable region of this channel matches the outer bound. Thus, we kno w the full capacity region for the quantum erasure channel. The final channel that we single-letterize is the qubit dephasing channel. Perhaps surprisingly , we are able to do so by arguing that the Dev etak-Shor CQ re gion and the Shor CE re gion each single-letterize. A. The Completely Depolarizing Channel The first single-letter example that we consider is the completely depolarizing channel. This channel simply replaces the input state with the maximally mixed state. Therefore, no classical or quantum information can tra verse it, even with the help of entanglement. Cor ollary 2: The following set of inequalities specifies the entanglement-assisted capacity of the completely depolarizing channel: C + 2 Q ≤ 0 , Q ≤ E , C + Q ≤ E . Pr oof: The proof follows by considering that the mutual information I ( AX ; B ) and the Hole vo information I ( X ; B ) in Theorem 1 vanish for any k -qudit state transmitted through the completely depolarizing channel and the coherent information is either negati ve or zero for any input state. Then the inequalities (12-14) there become the respectiv e inequalities abov e. One should observe that the region is actually trivial (it is empty) because C + 2 Q ≤ 0 . Nev ertheless, we still find the inequalities in Corollary 2 interesting because they coincide with those that we found in Ref. [26] for the “unit resource capacity” region 4 (modulo a different sign con vention with the entanglement rate E ). The proof techniques in Ref. [26] in volv e r eductio ad absurdum arguments that show how points outside the region conflict with physical law , whereas the arguments in the con verse proof of Theorem 1 are information theoretic. One should expect that the set of inequalities in Corollary 2 coincide with those for the unit resource capacity region because having access to the completely depolarizing channel is equiv alent to having no quantum channel at all— Bob can actually simulate this resource locally merely by preparing the maximally mixed state in his laboratory . 4 The unit resource capacity region is the set of rates that are achiev able without the aid of a noisy resource. Capacity Rate Triple ( C , Q, E ) Entanglement-assisted classical capacity (EAC) (2 (1 − ) , 0 , 1) Quantum capacity (LSD) (0 , 1 − 2 , 0) Classical capacity (HSW) (1 − , 0 , 0) Entanglement-assisted quantum capacity (EA Q) (0 , 1 − , ) T ABLE I T H E L E F T C O LU M N G I VE S A PA RT I CU L A R T Y P E O F C A P AC I T Y F O R T H E Q UA N TU M E R A SU R E C H A NN E L , A N D T H E R I GH T C O L UM N G I V ES T HE C O RR E S P ON D I NG O PT I M AL R A T E T R I P LE . B. The Quantum Erasur e Channel The quantum erasure channel is perhaps one of the simplest noisy quantum channels [32], because it has a simple speci- fication and its known transmission capacities admit simple formulas [33]. A quantum erasure channel passes the input state along to the en vironment and giv es Bob an erasure state | e i with probability . It passes the input state along to Bob and gi ves the en vironment an erasure state | e i with probability 1 − . It induces the following map on a density operator ρ A 0 : ρ A 0 → (1 − ) ρ B + | e i h e | B , and its isometric extension acts as follows: | ψ i AA 0 → √ 1 − | ψ i AB | e i E + √ | ψ i AE | e i B , where | ψ i AA 0 is some purification of ρ A 0 . T able I lists the known optimal transmission capacities for the quantum erasure channel. Bennett et al . determined the classical capacity of the quantum erasure channel with an intuiti ve argument (the outer bound exploits the Holev o bound [8] and the inner bound uses an encoding with or- thogonal states), and they determined its quantum capacity with a different intuiti ve argument (the well-known no-cloning argument combined with linear interpolation for the outer bound and one-way random hashing for the inner bound [33]). The optimality of the classical rate 2 (1 − ) and the quantum rate 1 − of an entanglement-assisted quantum erasure channel follows from the arguments in Ref. [10]. The optimality of the respectiv e entanglement consumption rates follows from our forthcoming arguments. Finally , note that we can obtain the quantum capacity result by combining the father protocol (entanglement-assisted quantum communica- tion) with entanglement distribution at a rate , and we can obtain entanglement-assisted classical communication from entanglement-assisted quantum communication by consuming all of its quantum communication at rate 1 − with super -dense coding. Corollary 3 below sho ws that the CQE capacity region of a quantum erasure channel admits a simple characterization in terms of three inequalities. W e pro ve the con verse by intuitiv e reasoning that one would perhaps expect to be able to apply to the quantum erasure channel, giv en earlier intuitive reasoning that authors have applied to this channel. W e prove the direct coding theorem by giving an explicit ensemble that reaches all of the bounds in the inequalities in Corollary 3. The result 15 is that time-sharing 5 between the four protocols in T able I is the optimal coding strategy . Cor ollary 3: Suppose a quantum erasure channel has an erasure probability . The follo wing set of inequalities specifies the capacity region of this entanglement-assisted channel for transmitting classical and quantum information: C + 2 Q ≤ 2 (1 − ) , (66) 1 − 2 1 − C + Q ≤ E + (1 − 2 ) , (67) C + (1 + ) Q ≤ (1 − ) (1 + E ) . (68) Pr oof: W e first prov e the con verse. The first bound in (66) holds because the sum rate C + 2 Q can nev er exceed 2 (1 − ) . Otherwise, one could beat the entanglement-assisted classical capacity by dense coding or one could beat the entanglement- assisted quantum capacity by teleportation. W e next consider the second bound in (67). W e first prove that time-sharing between the HSW point and the LSD point is an optimal strategy 6 and then show that this result implies the bound in (67). Consider a scheme of quantum error correction for an erasure channel with erasure parameter . If Alice transmits n qubits, then Bob recei ves n (1 − ) of these and the environment receiv es n of them (for the case of large n ). From these n (1 − ) physical qubits, Bob can perform a decoding to obtain n (1 − 2 ) logical qubits, by the quantum capacity result for the erasure channel. This implies an optimal “decoding ratio” of n (1 − 2 ) decoded qubits for the n (1 − ) receiv ed qubits: (1 − 2 ) / (1 − ) . Now let us consider a Dev etak- Shor-lik e code for the erasure channel. Suppose that Alice can achiev e the rate triple ( λ (1 − ) , (1 − λ )(1 − 2 ) + δ , 0) where δ is some small positive number (so that this rate triple represents any point that beats the time-sharing limit). Now if Alice transmits n qubits, Bob receiv es n (1 − ) of them and the environment again recei ves n of them. But this time, Bob performs measurements on nλ (1 − ) of them in order to obtain the classical information. Thus, these qubits are no longer av ailable for decoding quantum information because the measurements completely dephase them. This leav es n (1 − ) − nλ (1 − ) = n (1 − λ )(1 − ) qubits available for decoding the quantum information. If Bob could decode n ((1 − λ )(1 − 2 ) + δ ) logical qubits, this would contradict the optimality of the above “decoding ratio” because n ((1 − λ )(1 − 2 ) + δ ) / ( n (1 − λ )(1 − )) = (1 − 2 ) / (1 − ) + δ / (1 − λ )(1 − ) is greater than the optimal decoding ratio (1 − 2 ) / (1 − ) . Therefore, he must only be able to decode n (1 − λ )(1 − 2 ) logical qubits. This prov es that time-sharing between HSW and LSD is an optimal strategy for the quantum erasure channel. Now , the capacity region excludes any point lying above the C Q -plane 5 T ime-sharing is a simple method of combining coding strategies [30]. As an example, consider the case of time-sharing a channel between an ( n, Q 1 , ) quantum code and another ( n, Q 2 , ) quantum code. For any λ where 0 < λ < 1 , the sender uses the first code for a fraction λ of the channel uses and uses the other code for a fraction (1 − λ ) of the channel uses. This time- sharing strategy produces a quantum code with rate λQ 1 + (1 − λ ) Q 2 and error at most 2 . Time-sharing immediately giv es that the conv ex hull of any set of achiev able points is an achie vable region. 6 Dev etak and Shor stated (but did not explicitly prove) that time-sharing between HSW and LSD is optimal for the erasure channel [7]. with which we can combine with entanglement distribution to reach a point on the C Q -plane outside the Dev etak-Shor time-sharing bound (otherwise, we would be able to beat the time-sharing bound between HSW and LSD by combining this point with entanglement distribution). In particular, this means that achiev able points cannot be outside the plane containing the v ector connecting LSD to HSW and the vector of entanglement distribution. It is straightforward to calculate the equation for this plane. The vector connecting LSD to HSW is (0 , 1 − 2 , 0) − (1 − , 0 , 0) = ( − (1 − ) , 1 − 2 , 0) . The vector of entanglement distribution is (0 , − 1 , − 1) . A normal vector for the plane containing the two vectors is − 1 − 2 1 − , − 1 , 1 . Then the equation for the plane is − 1 − 2 1 − ( C − (1 − )) − Q + E = 0 , implying that achiev able points must obey the bound in (67) because they cannot lie outside this plane. The abo ve ar gument also shows that the EA Q rate triple (0 , 1 − , ) is optimal (in particular , that the entanglement consumption rate is optimal) because it lies at the intersection of the two bounds in (66) and (67). W e now prove the last bound in (68) in three steps. W e first prove that the entanglement consumption rate of the EA C protocol is optimal. W e then prov e that time-sharing between EA C and HSW is optimal, and finally rule out all points outside a plane containing the vector connecting EAC to HSW and the vector of super-dense coding. Consider the EA C rate triple (2 (1 − ) , 0 , 1) . The entanglement consumption rate of one ebit per channel use is optimal, i.e., one cannot achieve the classical rate of 2 (1 − ) with less than one ebit per channel use. The state that achie ves capacity is the maximally entangled state | Φ + i . The minimum amount of entanglement that this capacity-achieving state requires is H ( A ) = 1 ebit (we giv e a more detailed proof in Appendix D). Thus, no lower amount of entanglement could suf fice for achieving the maximal classical rate. W e now prov e that time-sharing between EA C and HSW is optimal by an argument similar to the argument for our other time-sharing bound. Consider a scheme of entanglement-assisted classical communication for an erasure channel with erasure parameter . If Alice transmits n qubits (that could potentially be entangled with n qubits of Bob’ s), then Bob receiv es n (1 − ) of these and the en vironment recei ves n of them (for the case of large n ). From these n (1 − ) physical qubits (and his halves of the ebits), Bob can perform a decoding to obtain n 2(1 − ) classical bits, by the entanglement-assisted classical capacity result for the erasure channel. This implies an optimal “EA decoding ratio” of n 2(1 − ) decoded bits for the n (1 − ) receiv ed qubits: 2(1 − ) / (1 − ) . No w let us consider a Shor- like code 7 for the erasure channel. Suppose that Alice can achiev e the rate triple ( λ (1 − ) + (1 − λ )2(1 − ) + δ, 0 , 1 − λ ) where δ is some small positiv e number (so that this rate triple 7 “Shor-like” in the sense of Ref. [12]. 16 represents any point that beats the time-sharing limit). Now if Alice transmits n qubits, then Bob recei ves n (1 − ) of them and the environment again receiv es n of them. But this time, Bob performs some measurement on nλ (1 − ) of them in order to obtain some of the classical information. Thus, these qubits are no longer a vailable for decoding any more classical information because they have already been decoded. This leaves n (1 − ) − nλ (1 − ) = n (1 − λ )(1 − ) qubits av ailable for decoding the extra classical information. If Bob could decode n ((1 − λ )2(1 − ) + δ ) extra classical bits, this would contradict the optimality of the abov e “EA decoding ratio” because n ((1 − λ )2(1 − ) + δ ) / ( n (1 − λ )(1 − )) = 2(1 − ) / (1 − ) + δ / (1 − λ )(1 − ) is greater than the optimal decoding ratio 2(1 − ) / (1 − ) . Therefore, he must only be able to decode n (1 − λ )2(1 − ) classical bits. This proves that time- sharing between HSW and EA C is an optimal strategy for the quantum erasure channel. Now , the capacity region excludes any point lying to the right of the C E -plane with which we can combine with super -dense coding to reach a point on the C E - plane outside the time-sharing bound (otherwise, we would be able to beat the time-sharing bound between HSW and EA C by combining this point with super-dense coding). In particular, this means that achiev able points cannot be outside the plane containing the vector connecting HSW to EA C and the vector of super-dense coding. It is straightforward to calculate the equation for this plane. Consider that the vector between EA C and HSW is (2 (1 − ) , 0 , 1) − (1 − , 0 , 0) = (1 − , 0 , 1) . The vector of dense coding is (2 , − 1 , 1) . A normal vector for this plane is ( − 1 , − (1 + ) , 1 − ) . The equation for the plane is − ( C − (1 − )) − (1 + ) Q + (1 − ) E = 0 , implying that achiev able points must obey the bound in (68) because they cannot lie outside this plane. W e ha ve now completed the proof of the outer bound. W e prov e the direct coding theorem. The simple way to prove it follows simply by time-sharing between the four protocols HSW , LSD, EA Q, and EA C, but it is interesting to explore a particular ensemble of states of the form (15) in Theorem 1 that achiev es the capacity . W e consider transmitting the A 0 system of the follo wing classical-quantum state through the channel: σ X AA 0 ≡ 1 2 | 0 i h 0 | X ⊗ ψ AA 0 0 + | 1 i h 1 | X ⊗ ψ AA 0 1 , (69) where | ψ 0 i AA 0 ≡ √ µ | 00 i AA 0 + p 1 − µ | 11 i AA 0 , | ψ 1 i AA 0 ≡ p 1 − µ | 00 i AA 0 + √ µ | 11 i AA 0 , and µ ∈ 0 , 1 2 . This classical-quantum state is a purified version of the ensemble considered in Ref. [7]. W e can I III II 2 1.8 1.6 1.4 1.2 1 0.8 0.6 0.4 0.2 0 0.8 0.6 0.4 0.2 0 0.7 0.5 0.3 0.1 1.5 0.5 1 0 E AC HSW LSD E AQ En tanglemen t c onsumption r a t e Q uan tum c ommunica tion r a t e Classical c ommunica tion r a t e Fig. 3. (Color online) The capacity region of the quantum erasure channel with erasure parameter = 1 / 4 . Planes I, II, and III correspond to the respectiv e bounds in (66-68). The optimal strategy is to time-share between classical coding (HSW), quantum coding (LSD), entanglement-assisted quan- tum coding (EAQ), and entanglement-assisted classical coding (EAC). The classically-enhanced father protocol does not giv e any impro vement over time- sharing for a quantum erasure channel. ev aluate various relev ant entropic quantities for this state: H ( B ) σ = 1 − + H 2 ( ) , H ( A ) σ = H 2 ( µ ) , H ( A | X ) σ = H 2 ( µ ) , H ( B | X ) σ = (1 − ) H 2 ( µ ) + H 2 ( ) , H ( E | X ) σ = H 2 ( µ ) + H 2 ( ) , where the state σ is the state resulting from sending the A 0 system through the erasure channel. It then follo ws that I ( X ; B ) σ = (1 − ) (1 − H 2 ( µ )) , I ( A i B X ) σ = (1 − 2 ) H 2 ( µ ) , 1 2 I ( A ; B | X ) σ = (1 − ) H 2 ( µ ) , 1 2 I ( A ; E | X ) σ = (1 − ) H 2 ( µ ) , I ( AX ; B ) = (1 + H 2 ( µ )) (1 − ) . A quick glance o ver the above information quantities re- veals that exploiting coding strategies such as the classically- enhanced father protocol gives no improvement over time- sharing because H 2 ( µ ) varies between zero and one as µ varies between zero and 1 / 2 (the classically-enhanced father protocol gi ves exactly the same performance as time-sharing, as does the classically-enhanced quantum communication strategy of De vetak and Shor [7]). Thus, the region obtained as the union of the one-shot, one-state regions is indeed equiv alent to the outer bound giv en above. Figure 3 plots this region for a quantum erasure channel with erasure parameter = 1 / 4 , demonstrating that this region is equiv alent to the outer bound. The follo wing corollary applies to the noiseless qubit chan- nel by simply plugging in = 0 . Cor ollary 4: The following set of inequalities specifies the entanglement-assisted capacity of the noiseless qubit channel 17 for transmitting classical and quantum information: C + 2 Q ≤ 2 , C + Q ≤ E + 1 . C. The Qubit Dephasing Channel In this section, we show that we can compute the full capacity region of a qubit dephasing channel and plot it in Figure 4 for a channel with dephasing parameter p = 0 . 2 . W e show also that the classically-enhanced father protocol can beat time-sharing for a qubit dephasing channel (the example is an extension of the ar gument in Ref. [7]). 1) Single-Letterization: W e first show that the classically- enhanced father trade-off curve is optimal in the sense that it lies along the boundary of the capacity region for the qubit dephasing channel. A surprisingly simple argument proves this result by resorting to the result of Devetak and Shor in Ref. [7]. There, they showed that the following trade-off curve in the C Q -plane is optimal: { ( C CQ ( µ ) , Q CQ ( µ ) , 0) : 0 ≤ µ ≤ 1 / 2 } , (70) where C CQ ( µ ) ≡ 1 − H 2 ( µ ) , Q CQ ( µ ) ≡ H 2 ( µ ) − H 2 ( g ( p, µ )) , g ( p, µ ) ≡ 1 2 + 1 2 r 1 − 16 · p 2 1 − p 2 µ (1 − µ ) . Now , consider the surface formed by the following set of points: { ( C CQ ( µ ) , Q CQ ( µ ) + E , E ) : 0 ≤ µ ≤ 1 / 2 , E ≥ 0 } . (71) This surface is an outer bound for the capacity region (if it were not so, one could combine points outside this surface with entanglement distribution and beat the optimal bound in (70) for the Devetak-Shor case). Now consider sending the µ -parametrized ensemble in (69), where µ ∈ [0 , 1 / 2] , through the qubit dephasing channel with dephasing parameter p . It is straightforward to show that the various entropic quantities in the classically-enhanced father protocol are as follows for the µ -parametrized ensemble: C CEF ( µ ) ≡ I ( X ; B ) σ = 1 − H 2 ( µ ) , Q CEF ( µ ) ≡ 1 2 I ( A ; B | X ) = H 2 ( µ ) − 1 2 H 2 ( g ( p, µ )) , E CEF ( µ ) ≡ 1 2 I ( A ; E | X ) = 1 2 H 2 ( g ( p, µ )) . Thus, the following set of points contains all points along the classically-enhanced father trade-off curve: { ( C CEF ( µ ) , Q CEF ( µ ) , E CEF ( µ )) : 0 ≤ µ ≤ 1 / 2 } . All points along the classically-enhanced father lie along the boundary because the y are of the form in (71) with E = H 2 ( g ( p, µ )) / 2 . This proves that the points along the classically-enhanced father trade-of f curve are optimal. One can also achie ve an y point along the surf ace in (71) with entan- glement consumption below the classically-enhanced father by combining the classically-enhanced father with entanglement distribution. W e now outline the proof that Shor’ s trade-of f curve for entanglement-assisted classical communication single- letterizes for the qubit dephasing channel (full details appear in Ref. [34]—the ar gument complements the argument in Ap- pendix B of Ref. [7]). Any point along Shor’ s trade-of f curve achiev es a classical communication rate of I ( AX ; B n ) at an entanglement consumption rate of H ( A | X ) [14]. Therefore, to determine a point along the trade-of f curve, we would like to maximize the classical communication rate while minimizing the entanglement consumption rate. T o do so, we can define the follo wing function f λ N ⊗ n ≡ max σ ( I ( AX ; B n ) − λH ( A | X )) , where λ > 0 and the maximization is ov er all states of the form (15), with the exception that the E 0 system is not necessary for Shor’ s trade-off curve [14]. By a sequence of arguments similar to those in Appendix B of Ref. [7], we can show that f λ N ⊗ n ≤ nh λ ( N ) , where h λ ( N ) ≡ max σ µ ( H ( Y ) + (1 − λ ) H ( A | X ) − H ( E | X )) , Y is the completely dephased version of B , and σ µ is a state that arises after sending the A 0 system of a state of the form in (69) through a single use of the qubit dephasing channel. This then shows that the region single-letterizes and that states of the form in (69) giv e rise to optimal points that lie along Shor’ s trade-off curve. Shor’ s trade-off curve in the CE-plane has the following form: { ( C CE ( µ ) , 0 , E CE ( µ )) : 0 ≤ µ ≤ 1 / 2 } , (72) where C CE ( µ ) ≡ 1 + H 2 ( µ ) − H 2 ( g ( p, µ )) , E CE ( µ ) ≡ H 2 ( µ ) . W e can now exploit Shor’ s trade-off curve to outline a bounding surface in the CQE space (just as we did before with the Devetak-Shor curve and entanglement distribution). Consider the surface formed by the follo wing set of points: { ( C CE ( µ ) − 2 E , E , E CE ( µ ) − E ) : 0 ≤ µ ≤ 1 / 2 , E ≥ 0 } . (73) This surface is an outer bound for the capacity region (if it were not so, one could combine points outside this surface with super-dense coding and beat the optimal bound in (72)). Interestingly , this surface intersects the surface in (71) at exactly the classically-enhanced father trade-off curve. W e can finally outline the full capacity region by combining the two surfaces in (71) and (73) with the bound: C + 2 Q ≤ 2 − H 2 ( g ( p, 1 / 2)) . (74) The above bound is the largest that the entanglement-assisted classical capacity can be and therefore bounds the sum rate C + 2 Q as we hav e argued previously . The intersection of these three surfaces forms a single-letter bound for the capacity 18 Shor ’ s cur v e En tanglemen t c onsumption r a t e 2 1.8 1.6 1.4 1.2 1 0.8 0.6 0.4 0.2 0 0.8 0.6 0.4 0.2 0 2 1.5 1 0.5 0 DS cur v e CEF cur v e Q uan tum c ommunica tion r a t e Classical c ommunica tion r a t e Fig. 4. (Color online) The above figure plots the full capacity region for the qubit dephasing channel with dephasing parameter p = 0 . 2 . It outlines Shor’ s trade-off curve, the Devetak-Shor (DS) trade-off curve, and the classically- enhanced father (CEF) trade-off curve. The surface between Shor’ s curv e and the CEF curve is that in (73). The surface between the CEF curve and the DS curve is that in (71). Finally , (74) specifies the solid plane. This region is a union of re gions formed by translating the unit resource capacity re gion from Ref. [26] along the classically-enhanced father trade-off curve. This point is perhaps more clear in Ref. [26] where we plot the full triple trade-off. region, and all points on the boundary are achiev able by combining the classically-enhanced father trade-off curve with entanglement distrib ution, super-dense coding, or the wasting of entanglement. Figure 4 plots the full capacity region. 2) The Classically-Enhanced F ather Pr otocol can beat T ime-Sharing: An important question for entanglement- assisted classical-quantum coding is whether a time-sharing strategy is optimal for all channels or if the classically- enhanced father protocol can gi ve an improvement over time- sharing. There are three time-sharing strategies that one could employ in EA CQ coding. In all three strategies, we suppose that the sender and recei ver share some finite amount of entanglement E . The three strategies are as follows: 1) Use an entanglement-assisted quantum code with rate triple (0 , Q 1 , E 1 ) and an HSW code with rate triple ( C 2 , 0 , 0) . If E = λE 1 , then time-sharing produces an EA CQ code with rate triple ((1 − λ ) C 2 , λQ 1 , E ) . 2) Use an entanglement-assisted classical code with rate triple ( C 1 , 0 , E 1 ) and a quantum channel code with rate triple (0 , Q 2 , 0) . If E = λE 1 , then time-sharing produces an EA CQ code with rate triple ( λC 1 , (1 − λ ) Q 2 , E ) . 3) Use an entanglement-assisted quantum code with rate triple (0 , Q 1 , E 1 ) and an entanglement-assisted classi- cal code with rate triple ( C 2 , 0 , E 2 ) . If E = λE 1 + (1 − λ ) E 2 , then time-sharing produces an EA CQ code with rate triple ((1 − λ ) C 2 , λQ 1 , E ) . W e should compare the classically-enhanced father protocol to the first time-sharing strategy because the two points EA Q and HSW are special cases of it. For the second time-sharing strategy , it is clear that this strategy is not optimal because the line connecting EA C to LSD is strictly inside the capacity region. F or the third time-sharing strategy , time-sharing is the optimal strategy . If it were not (in the sense that one could achiev e a higher quantum or classical rate than a point along the time-sharing bound), then one could beat the bound in (12) by combining this protocol with either teleportation or super-dense coding. W e now consider the first case for the qubit dephasing channel and show that the classically-enhanced father protocol can beat a time-sharing strate gy . Consider the qubit dephasing channel with dephasing parameter p = 0 . 2 . The classical capacity of this channel is one bit per channel use, and the entanglement-assisted quantum capacity is about 0.7655 qubits per channel use while using about 0.2345 ebits per channel use. The solid red line in Figure 5(a) corresponds to the time- sharing line between these two optimal points. The blue dotted line in Figure 5(a) corresponds to the v arious points along the classically-enhanced father protocol. In comparing the time- sharing line to the classically-enhanced f ather trade-off curv e, we see that the classically-enhanced father protocol achie ves more quantum communication for less entanglement consump- tion for any point along the time-sharing line that achieves the same amount of classical communication. Figure 5(b) makes this statement precise by comparing the difference in quantum communication and entanglement consumption for all points along the trade-off curve that achiev e the same amount of classical communication as a time-sharing point. V I I I . C O N C L U S I O N W e have prov en the entanglement-assisted classical and quantum capacity theorem. This theorem determines the ul- timate rates at which a noisy quantum channel can com- municate both classical and quantum information reliably , while consuming entanglement to do so. The coding strat- egy exploits a new entanglement-assisted classical-quantum coding strategy , the classically-enhanced father pr otocol , and the unit protocols of teleportation, super-dense coding, and entanglement distrib ution. Sev eral protocols in the family tree of quantum Shannon theory are now child protocols of the classically-enhanced father . W e also ha ve provided example channels whose corresponding CQE capacity regions single- letterize, so that we can actually determine the region for these channels, and we have sho wn that classically-enhanced father protocol beats a time-sharing strategy for the case of a qubit dephasing channel. W e discuss follo w-up work and sev eral open problems in what follows. A. The Full T riple T rade-off The present article addresses only one octant of the channel coding scenario—the octant where we consume entanglement and generate classical and quantum communication. W e char- acterize the full triple trade-off region in Ref. [26], where we show that the classically-enhanced father protocol combined with the unit resource protocols in (61-63) achie ves the full capacity region for all octants. 19 0 0.25 0.5 0.75 0.2 0.4 0.6 0.8 0 0.05 0.1 0.15 0.2 0.25 Q C E Classically−enhanced father protocol Time−sharing HSW to Father 0 1 2 3 4 x 10 −3 −4. 5 −4 −3. 5 −3 −2. 5 −2 −1. 5 −1 −0. 5 0 0.5 x 10 −3 Q E Extra quantum communication with less entanglement consumption (a) (b) Fig. 5. (Color online) (a) The figure on the left displays the points achiev able by time-sharing between entanglement-assisted quantum coding and classical coding on the solid red line, and it displays the points achiev able with the classically-enhanced father protocol on the dotted blue line. The channel for which we are coding is the qubit dephasing channel with dephasing parameter p = 0 . 2 . The figure demonstrates that one can achiev e more quantum communication with less entanglement consumption, while ha ving the same rate of classical communication, by emplo ying the classically-enhanced father protocol instead of a time-sharing strate gy . (b) The figure on the right makes the previous statement precise, by showing the difference between quantum communication and entanglement consumption for achiev able points on the classically-enhanced father trade-of f curv e that attain the same rate of classical communication as a time-sharing strategy . B. The Structur e of Classically-Enhanced F ather Codes In Ref. [20], one of the authors constructed a classically- enhanced father code that uses only ancilla qubits for encoding classical information. In Ref. [19], the other author constructed a classically-enhanced father code that uses both ancilla qubits and ebits for encoding classical information. One might think that using ebits in addition to ancilla qubits for encoding classical information could improve performance and it was unclear which coding structure might perform better . The structure of our classically-enhanced father protocol actually giv es a hint for constructing classically-enhanced father codes that achiev e the rates in Theorem 1. Consider the protocol in the proof of the direct coding part of Theo- rem 1. Bob decodes the classical information by measuring the channel outputs only . He does not need to measure his half of the entanglement to decode the classical information. This decoding implies that he is not using the entanglement for sending classical information—if he were, he would need to measure his half of the entanglement as well. This observation lends creedence to the conjecture that it is sufficient to encode classical information into ancilla qubits when attempting to construct codes that achie ve the trade-off rate triple in Theo- rem 1. C. Other Issues Another issue remains with the “pasting” proof technique. It relies on the assumption that the channel is IID and thus does not apply in a straightforward way to channels with memory . Many proof techniques in quantum Shannon theory rely on a “one-shot” lemma applied to the IID case. The usefulness of this method of proof is that the one-shot result can apply to more general scenarios such as channels that hav e memory . So it may be useful to de velop a one-shot result for the code pasting technique. I X . A C K N O W L E D G E M E N T S The authors thank Kamil Br ´ adler , Igor Dev etak, Patrick Hayden, Dave T ouchette, and Andreas W inter for useful discussions. The authors thank Chung-Hsien Chou and the National Center for Theoretical Science (South) for hosting M.-H.H. as a visitor and thank Martin R ¨ otteler and NEC Lab- oratories America for hosting M.M.W . as a visitor . M.M.W . acknowledges support from the National Research Foundation & Ministry of Education, Singapore. The authors acknowledge support from the MDEIE (Qu ´ ebec) PSR-SIIRI international collaboration grant. A P P E N D I X A P RO O F O F P R O P O S I T I O N 2 The proof of Proposition 2 is an extension of the de velop- ment in Appendix D of Ref. [6]. Pr oposition 2: Consider an arbitrary density operator ρ A 0 whose spectral decomposition is as follows: ρ A 0 = X x ∈X p ( x ) | x i h x | A 0 . The n th extension of the above state as a tensor power state is as follows: ρ A 0 n ≡ ( ρ A 0 ) ⊗ n = X x n ∈X n p n ( x n ) | x n i h x n | A 0 n . 20 W e define the pruned distribution p 0 n as follo ws: p 0 n ( x n ) ≡ p n ( x n ) / P x n ∈ T X n δ p n ( x n ) : x n ∈ T X n δ 0 : else , where T X n δ denotes the δ -typical set of sequences with length n . Let e ρ A 0 n denote the following “pruned state”: e ρ A 0 n ≡ X x n ∈ T X n δ p 0 n ( x n ) | x n i h x n | A 0 n . (75) For any > 0 and sufficiently large n , the state ρ A 0 n is close to e ρ A 0 n by the gentle measurement lemma [35] and the typical subspace theorem [8]: ρ A 0 n − e ρ A 0 n 1 ≤ 2 . For any density operator ρ A 0 , it is possible to construct an entanglement-assisted quantum code that achieves the quan- tum communication rate and entanglement consumption rate in Proposition 2. Ref. [15] provides group-theoretical and other clever arguments to show how to achie ve the rates in Proposition 2. Another method for achieving the rates in Proposition 2 is to exploit the connection between quantum priv acy and quantum coherence in constructing quantum codes [6], [36]. Indeed, in Ref. [37], one of the current authors showed how to construct secret-ke y-assisted pri vate classical codes for a quantum channel. Using the methods of [6], [36], it is possible to make “coherent” versions, i.e., entanglement- assisted quantum codes, of these secret-key-assisted priv ate classical codes. Let [ k ] denote a set of size ∼ 2 nQ and let [ m ] denote a set of size ∼ 2 nE . Let U k,m denote ∼ 2 n ( Q + E ) random variables that we choose according to the pruned distribution p 0 n ( x n ) . The realizations u k,m of the random variables U k,m are sequences in X n and are the basis for constructing an entanglement-assisted quantum code C whose codew ords are as follo ws C = {| φ k i A n T B } k . The entanglement-assisted quantum codewords | φ k i A n T B in C are as follows | φ k i A n T B ≡ 1 √ 2 nE 2 nE X m =1 | φ u k,m i A 0 n | m i T B , where | φ u k,m i A 0 n ≡ | u k,m i A 0 n . W e then expurgate this code to improve its performance and this expurgation has a minimal impact on the rate of the code. After expur gation, the code forms a good entanglement- assisted quantum code, resulting in failure with probability + 10 4 √ by the arguments in Refs. [6], [36]. Suppose that we choose a particular entanglement-assisted quantum code C according to the abov e prescription. Its code density operator is ρ A 0 n T B ( C ) = 1 2 nQ 2 nQ X k =1 | φ k i h φ k | A 0 n T B , and its input code density operator is ρ A 0 n ( C ) = T r T B n ρ A 0 n T B ( C ) o = 1 2 n ( Q + E ) 2 nE X m =1 2 nQ X k =1 | φ u k,m ih φ u k,m | A 0 n . Suppose we now consider the entanglement-assisted code chosen according to the above prescription as a random code C (where C is now a random variable). Let ρ 0 A 0 n ( C ) be the channel input density operator for the random code before expur gation and ρ A 0 n ( C ) its channel input density operator after expur gation: ρ 0 A 0 n ( C ) ≡ 1 2 n ( Q 0 + E 0 ) 2 nQ 0 X k =1 2 nE 0 X m =1 | φ U k,m ih φ U k,m | A 0 n , ρ A 0 n ( C ) ≡ 1 2 n ( Q + E ) 2 nQ X k =1 2 nE X m =1 | φ U k,m ih φ U k,m | A 0 n , where the primed rates are the rates before expurgation and the unprimed rates are those after expurgation (they are slightly different b ut identical for large n ). Let ρ 0 A 0 n and ρ A 0 n denote the expectation of the abov e channel input density operators: ρ 0 A 0 n ≡ E C n ρ 0 A 0 n ( C ) o , ρ A 0 n ≡ E C n ρ A 0 n ( C ) o . Choosing our code in the particular way that we did leads to an interesting consequence. The expectation of the density oper- ator corresponding to Alice’ s restricted codeword | φ U k,m i A 0 n is equal to the pruned state in (75): E C n | φ U k,m ih φ U k,m | A 0 n o = X x n p 0 n ( x n ) | φ x n i h φ x n | A 0 n , because we choose the codewords | φ U k,m i randomly according to the pruned distribution p 0 n ( x n ) . Then the expected channel input density operator ρ 0 A 0 n is as follows: ρ 0 A 0 n = E C n ρ 0 A 0 n ( C ) o (76) = 1 2 n ( Q 0 + E 0 ) 2 nQ 0 X k =1 2 nE 0 X m =1 E C n | φ U k,m ih φ U k,m | A 0 n o (77) = X x n p 0 n | φ x n i h φ x n | A 0 n . (78) Then we know that the following inequality holds for ρ 0 A 0 n and the tensor power state ρ A 0 n ρ 0 A 0 n − ρ A 0 n 1 ≤ 2 (79) by the typical subspace theorem and the gentle measurement lemma. The expur gation of any entanglement-assisted code C has a minimal effect on the resulting channel input density operator [6]: ρ 0 A 0 n ( C ) − ρ A 0 n ( C ) 1 ≤ 4 4 √ . 21 The above inequality implies that the following one holds for the expected channel input density operators ρ 0 A 0 n and ρ A 0 n ρ 0 A 0 n − ρ A 0 n 1 ≤ 4 4 √ , (80) because the trace distance is con vex. The follo wing inequality holds ρ A 0 n − ρ A 0 n 1 ≤ 2 + 4 4 √ , (81) by applying the triangle inequality to (79) and (80). Therefore, the random entanglement-assisted quantum code is ρ -like. A P P E N D I X B P RO O F O F P R O P O S I T I O N 3 W e now prov e Proposition 3 that applies to a random father code that has an associated classical string. Pr oposition 3: The proof is similar to the proof of Proposition 5 in Ref. [7]. Suppose that we hav e an en- semble { p x , ρ A 0 x } where each density operator ρ A 0 x has a purification ψ AA 0 x and state φ AB E x = U A 0 → B E N ( ψ AA 0 x ) arising from the channel N A 0 → B . By Proposition 2, for suf ficiently large n and for all x ∈ X , there exists a random ρ A 0 x -like entanglement-assisted ( n [ p x − δ ] , ) code of quantum rate Q x = I ( A ; B ) φ x / 2 − δ and entanglement consumption rate E x = I ( A ; E ) φ x / 2 + δ . Its expected channel input density operator ρ A 0 n [ p x − δ ] x is close to a tensor po wer of the state ρ A 0 x : ρ A 0 n [ p x − δ ] x − ρ ⊗ n [ p x − δ ] x 1 ≤ . The code’ s quantum rate is Q x = 1 2 I ( A ; B ) φ x − δ because it transmits n [ p x − δ ] Q x qubits for n [ p x − δ ] uses of the channel. The code’ s entanglement consumption rate is E x = 1 2 I ( A ; E ) φ x + δ because it consumes at least n [ p x − δ ] E x ebits for n [ p x − δ ] uses of the channel. W e produce an ( n − |X | δ, |X | ) entanglement-assisted code with expected channel input density operator ρ A 0 n (1 −|X | δ ) = O x ρ A 0 n [ p x − δ ] x by “pasting” |X | of these codes together (one for each x ). Ap- plying the triangle inequality |X | times, the expected channel input density operator ρ A 0 n (1 −|X | δ ) of the pasted code is close to a pasting of the tensor power states { ρ ⊗ n [ p x − δ ] x } x : ρ A 0 n (1 −|X | δ ) − O x ρ ⊗ n [ p x − δ ] x 1 ≤ |X | . (82) Consider the classical sequence x n . Let random variable X hav e the probability distrib ution p and define the typical set T X n δ = { x n : ∀ x | n x − np x | ≤ δ n } , where n x ≡ N ( x | x n ) is the number of occurrences of the symbol x in x n . If x n lies in the typical set T X n δ , then we can construct a conditional permutation operation that permutes the elements of the input sequence as follo ws [38]: x n → x 1 · · · x 1 | {z } n [ p x 1 − δ ] x 2 · · · x 2 | {z } n [ p x 2 − δ ] · · · x |X | · · · x |X | | {z } n h p x |X | − δ i x g where x g (for “ x garbage”) denotes the remaining n |X | δ symbols in x n . The density operator ρ x n corresponds to the input sequence x n . W e can construct a conditional permutation unitary that acts on the density operator ρ x n and changes the ordering of the state ρ x n as follo ws: ρ x n → O x ρ n [ p x − δ ] x ⊗ ρ x g where dim ρ x g ≤ n |X | δ log d A 0 . W e modify the random entanglement-assisted code slightly by inserting |X | δ “garbage states” with density operator ρ x g and define the expected channel input density operator ρ A 0 n for the full code as follows: ρ A 0 n ≡ ρ A 0 n (1 −|X | δ ) ⊗ ρ x g . Then the expected channel input density operator ρ A 0 n is close to the permuted version of ρ x n ρ A 0 n − O x ρ n [ p x − δ ] x ⊗ ρ x g 1 ≤ |X | . The quantum rate Q for the random “pasted” father code is as follo ws: Q = P x nQ x [ p x − δ ] n = X x Q x [ p x − δ ] = X x p x I ( A ; B ) φ x 2 − δ − δ Q x = I ( A ; B | X ) 2 − c 0 δ, where c 0 ≡ 1 + X x Q x . The entanglement consumption rate E is as follo ws: E = P x nE x [ p x − δ ] n = X x E x [ p x − δ ] = X x p x I ( A ; E ) φ x 2 − δ − δ E x = I ( A ; E | X ) 2 − c 00 δ, where c 00 ≡ 1 + X x E x . A permutation relates the states ρ x n and N x ρ n [ p x − δ ] x ⊗ ρ x g . Therefore, there e xists an ( n, |X | ) random entanglement- asissted code of the same quantum communication rate and entanglement consumption rate with an e xpected channel input density operator ρ 0 A 0 n that is close to the tensor po wer state ρ x n : ρ 0 A 0 n − ρ x n 1 ≤ |X | , because the action of the IID channel N ⊗ n is in variant under permutations of the input Hilbert spaces. 22 A P P E N D I X C G E N T L E M E A S U R E M E N T F O R E N S E M B L E S Lemma 1 (Gentle Measurement for Ensembles): Let { p x , ρ x } be an ensemble with av erage ρ ≡ P x p x ρ x . Gi ven a positiv e operator X with X ≤ I and Tr { ρX } ≥ 1 − where ≤ 1 , then X x p x ρ x − √ X ρ x √ X 1 ≤ √ 8 . Pr oof: W e can apply the same steps in the proof of the gentle measurement lemma [39] to get the following inequality: ρ x − √ X ρ x √ X 2 1 ≤ 8 (1 − Tr { ρ x X } ) . Summing ov er both sides produces the following inequality: X x p x ρ x − √ X ρ x √ X 2 1 ≤ 8 (1 − Tr { ρX } ) ≤ 8 . T aking the square root of the above inequality gives the following one: s X x p x ρ x − √ X ρ x √ X 2 1 ≤ √ 8 . Concavity of the square root implies then implies the result: X x p x r ρ x − √ X ρ x √ X 2 1 ≤ √ 8 . A P P E N D I X D E N T A N G L E M E N T C O N S U M P T I O N R A T E O F T H E E AC C L A S S I C A L C A PAC I T Y W e prove that the entanglement consumption rate corre- sponding to the maximal EAC rate is one ebit. Consider a general qubit density operator ρ A 0 that Alice can input to the erasure channel. Let ψ AA 0 denote the purification of ρ A 0 . Suppose that ρ has the spectral decomposition ρ = p | φ 0 ih φ 0 | + (1 − p ) | φ 1 ih φ 1 | for some orthonormal states | φ 0 i , | φ 1 i . After Alice transmits this density operator through an erasure channel with erasure parameter , Bob has the following state: σ B ≡ (1 − ) ρ + | e ih e | , and Eve has σ E ≡ ρ + (1 − ) | e ih e | , where | e i is an erasure state. The entropies H ( A ) , H ( B ) , and H ( E ) are as follo ws: H ( A ) = H 2 ( p ) , H ( B ) = (1 − ) H 2 ( p ) + H 2 ( ) , H ( E ) = H 2 ( p ) + H 2 ( ) , and the mutual information I ( A ; B ) is as follows: I ( A ; B ) = H ( A ) + H ( B ) − H ( E ) = 2(1 − ) H 2 ( p ) . This quantity is maximized only when p = 1 2 , implying that the entanglement consumed for this state is exactly one ebit because H ( A ) = H 2 ( p ) . Thus, Alice and Bob cannot consume entanglement at a lower rate than this amount in order to achiev e the EA C capacity . A P P E N D I X E I S O M E T R I C E N C O D I N G S S U FFI C E I N T H E C Q E T H E O R E M W e pro ve that it is only necessary to consider isometric en- codings for achieving points in the CQE capacity region. Our argument follo ws the technique of Ref. [14], by showing that a protocol can only impro ve upon measuring the en vironment of a non-isometric encoder . Suppose that we exploit the following state that results from a non-isometric encoder, rather than the state in (15): e σ X AB E E 0 ≡ X x p ( x ) | x i h x | X ⊗ U A 0 → B E N ( φ AA 0 E 0 x ) . (83) The inequalities in (12-14) for the CQE capacity region inv olve the mutual information I ( AX ; B ) e σ , the Holev o information I ( X ; B ) e σ , and the coherent information I ( A i B X ) e σ . As we show below , each of these entropic quantities can only improv e if Alice measures the system E 0 . This improv ement then im- plies that it is only necessary to consider isometric encodings in the CQE capacity theorem. Suppose that Alice sends the system E 0 through a com- pletely dephasing channel ∆ E 0 → Y to obtain a classical vari- able Y (this simulates a measurement). Let σ X Y AB E denote this later state, a state of the form: σ X Y AB E ≡ X x p ( x, y ) | x i h x | X ⊗ | y i h y | Y ⊗ U A 0 → B E N ( ψ AA 0 x,y ) . (84) This state is actually a state of the form in (15) if we subsume the classical variables X and Y into one classical variable. The follo wing three inequalities each follo w from an appli- cation of the quantum data processing inequality (or, equi va- lently , strong subadditivity): I ( X ; B ) e σ = I ( X ; B ) σ ≤ I ( X Y ; B ) σ , (85) I ( AX ; B ) e σ = I ( AX ; B ) σ ≤ I ( AX Y ; B ) σ (86) I ( A i B X ) e σ = I ( A i B X ) σ ≤ I ( A i B X Y ) σ (87) Each of these inequalities proves the desired result for the re- spectiv e Hole vo information, mutual information, and coherent information. R E F E R E N C E S [1] A. S. Holevo, “The capacity of the quantum channel with general signal states, ” IEEE T ransactions on Information Theory , vol. 44, no. 1, pp. 269–273, 1998. [2] B. Schumacher and M. D. W estmoreland, “Sending classical information via noisy quantum channels, ” Physical Revie w A , vol. 56, no. 1, pp. 131– 138, July 1997. [3] C. E. Shannon, “ A mathematical theory of communication, ” Bell System T echnical Journal , v ol. 27, pp. 379–423, 1948. [4] S. Lloyd, “Capacity of the noisy quantum channel, ” Physical Review A , vol. 55, no. 3, pp. 1613–1622, March 1997. [5] P . W . Shor, “The quantum channel capacity and coherent information, ” in Lectur e Notes, MSRI W orkshop on Quantum Computation , 2002. [6] I. Devetak, “The priv ate classical capacity and quantum capacity of a quantum channel, ” IEEE T ransactions on Information Theory , vol. 51, pp. 44–55, January 2005. 23 [7] I. Devetak and P . W . Shor, “The capacity of a quantum channel for simultaneous transmission of classical and quantum information, ” Communications in Mathematical Physics , vol. 256, pp. 287–303, 2005. [8] M. A. Nielsen and I. L. Chuang, Quantum Computation and Quantum Information . Cambridge University Press, 2000. [9] C. H. Bennett and S. J. Wiesner , “Communication via one- and two- particle operators on Einstein-Podolsky-Rosen states, ” Physical Review Letters , vol. 69, no. 20, pp. 2881–2884, November 1992. [10] C. H. Bennett, P . W . Shor, J. A. Smolin, and A. V . Thapliyal, “Entanglement-assisted classical capacity of noisy quantum channels, ” Physical Review Letters , v ol. 83, no. 15, pp. 3081–3084, October 1999. [11] ——, “Entanglement-assisted capacity of a quantum channel and the rev erse Shannon theorem, ” IEEE T ransactions on Information Theory , vol. 48, pp. 2637–2655, 2002. [12] P . W . Shor, Quantum Information, Statistics, Probability (Dedicated to A. S. Holevo on the occasion of his 60th birthday) . Rinton Press, Inc., (quant-ph/0402129), 2004, ch. “The classical capacity achie vable by a quantum channel assisted by limited entanglement”, pp. 144–152. [13] I. Devetak, A. W . Harrow , and A. W inter, “ A family of quantum pro- tocols, ” Physical Revie w Letters , vol. 93, no. 23, p. 230504, December 2004. [14] ——, “ A resource framework for quantum Shannon theory , ” IEEE T ransactions on Information Theory , vol. 54, no. 10, pp. 4587–4618, October 2008. [15] A. Abeyesinghe, I. Dev etak, P . Hayden, and A. Winter , “The mother of all protocols: restructuring quantum information’ s family tree, ” Pro- ceedings of the Royal Society A , vol. 465, no. 2108, pp. 2537–2563, 2009. [16] J. Oppenheim, “State redistribution as merging: introducing the coherent relay , ” , 2008. [17] A. Abeyesinghe and P . Hayden, “Generalized remote state preparation: T rading cbits, qubits, and ebits in quantum communication, ” Physical Review A , v ol. 68, no. 6, p. 062319, December 2003. [18] M.-H. Hsieh, I. De vetak, and A. W inter , “Entanglement-assisted capacity of quantum multiple-access channels, ” IEEE Tr ansactions on Informa- tion Theory , vol. 54, no. 7, pp. 3078–3090, 2008. [19] I. Kremsky , M.-H. Hsieh, and T . A. Brun, “Classical enhancement of quantum-error-correcting codes, ” Physical Re view A , v ol. 78, no. 1, p. 012341, 2008. [20] M. M. W ilde and T . A. Brun, “Unified quantum conv olutional coding, ” in Proceedings of the IEEE International Symposium on Information Theory (arXiv:0801.0821) , July 2008, pp. 359–363. [21] J. Y ard, “Simultaneous classical-quantum capacities of quantum multiple access channels, ” Ph.D. dissertation, Stanford Uni versity (arXi v:quant- ph/0506050), June 2005. [22] E. H. Lieb and M. B. Ruskai, “Proof of the strong subadditivity of quantum-mechanical entropy , ” Journal of Mathematical Physics , v ol. 14, pp. 1938–1941, 1973. [23] B. Schumacher and M. A. Nielsen, “Quantum data processing and error correction, ” Physical Review A , vol. 54, no. 4, pp. 2629–2635, October 1996. [24] C. H. Bennett, G. Brassard, C. Cr ´ epeau, R. Jozsa, A. Peres, and W . K. W ootters, “T eleporting an unknown quantum state via dual classical and Einstein-Podolsky-Rosen channels, ” Physical Review Letters , vol. 70, no. 13, pp. 1895–1899, March 1993. [25] J. Y ard, P . Hayden, and I. Devetak, “Capacity theorems for quantum multiple-access channels: Classical-quantum and quantum-quantum ca- pacity regions, ” IEEE T ransactions on Information Theory , vol. 54, no. 7, pp. 3091–3113, July 2008. [26] M.-H. Hsieh and M. M. W ilde, “Trading classical communication, quan- tum communication, and entanglement in quantum Shannon theory , ” arXiv:0901.3038 , 2009. [27] M. Fannes, “ A continuity property of entropy density for spin lattice systems, ” Communications in Mathematical Physics , vol. 31, pp. 291– 294, 1973. [28] R. Alicki and M. Fannes, “Continuity of quantum conditional informa- tion, ” J ournal of Physics A: Mathematical and General , vol. 37, no. 5, pp. L55–L57, 2004. [29] J. Y ard and I. Dev etak, “Optimal quantum source coding with quantum information at the encoder and decoder, ” IEEE T ransactions on Infor- mation Theory , vol. 55, no. 11, pp. 5339–5351, November 2009. [30] T . M. Cover and J. A. Thomas, Elements of Information Theory . Wile y- Interscience, 1991. [31] H. Barnum, E. Knill, and M. A. Nielsen, “On quantum fidelities and channel capacities, ” IEEE T ransactions on Information Theory , v ol. 46, no. 4, pp. 1317–1329, July 2000. [32] M. Grassl, T . Beth, and T . Pellizzari, “Codes for the quantum erasure channel, ” Physical Re view A , vol. 56, no. 1, pp. 33–38, July 1997. [33] C. H. Bennett, D. P . DiV incenzo, and J. A. Smolin, “Capacities of quantum erasure channels, ” Physical Review Letters , vol. 78, no. 16, pp. 3217–3220, April 1997. [34] K. Br ´ adler , P . Hayden, D. T ouchette, and M. M. W ilde, “Trade- off capacities of the quantum Hadamard channels, ” , January 2010. [35] A. W inter, “Coding theorem and strong conv erse for quantum channels, ” IEEE T ransactions on Information Theory , vol. 45, no. 7, pp. 2481– 2485, 1999. [36] I. Devetak and A. Winter , “Relating quantum priv acy and quantum coherence: An operational approach, ” Physical Review Letters , vol. 93, no. 8, p. 080501, August 2004. [37] M.-H. Hsieh, Z. Luo, and T . Brun, “Secret-key-assisted priv ate classical communication capacity over quantum channels, ” Physical Review A , vol. 78, no. 4, p. 042306, 2008. [38] H. Krovi and I. De vetak, “Local purity distillation with bounded classical communication, ” Physical Re view A , vol. 76, no. 1, p. 012321, 2007. [39] A. Winter , “Coding theorems of quantum information theory , ” Ph.D. dissertation, Univ ersit ¨ at Bielefeld (arXiv:quant-ph/9907077), 1999.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment