Trident, a new pseudo random number generator based on coupled chaotic maps
This article describes a new family of cryptographically secure pseudorandom number generators, based on coupled chaotic maps, that will serve as keystream in a stream cipher. The maps are a modification of a piecewise linear map, by dynamic changing of the coefficient values and perturbing its lesser significant bits.
💡 Research Summary
The paper introduces “Trident,” a cryptographically secure pseudorandom number generator (PRNG) built on coupled chaotic maps with dynamic coefficient updates and low‑order‑bit perturbations. The authors begin by reviewing the limitations of traditional PRNGs such as linear feedback shift registers (LFSRs) and single chaotic‑map generators, noting that fixed parameters lead to predictable cycles and make the generators vulnerable to state‑recovery and differential attacks. To address these issues, Trident employs three complementary mechanisms.
First, the core chaotic map is a piecewise‑linear chaotic map (PLCG) of the form xₙ₊₁ = a·xₙ ⊕ b. Unlike conventional PLCG implementations that keep a and b constant, Trident changes them at every iteration. The new coefficients aₙ and bₙ are derived either from a pre‑computed random table or from deterministic functions of the current state, thereby turning the map itself into a non‑stationary, highly nonlinear system. This dynamic coefficient scheme dramatically expands the state space and eliminates fixed points that could be exploited.
Second, Trident couples multiple (typically three) independent PLCGs. Each sub‑map i maintains its own state xᵢⁿ, but its next state is also influenced by the outputs yⱼⁿ of the other sub‑maps through weighted sums:
xᵢⁿ⁺¹ = aᵢⁿ·xᵢⁿ ⊕ bᵢⁿ ⊕ Σ_{j≠i} w_{ij}·yⱼⁿ
The coupling weights w_{ij} are chosen to be odd integers to preserve invertibility. This inter‑dependence creates a high‑dimensional chaotic system where the trajectory of any single map cannot be isolated, thus thwarting attacks that target a single deterministic recurrence.
Third, Trident deliberately perturbs the least‑significant bits (LSBs) of the output. While chaotic maps exhibit strong diffusion in the most significant bits, the LSBs often retain linear correlations. Trident resolves this by XOR‑mixing selected LSBs with bits from other sub‑maps before emitting the final keystream word. This operation equalizes entropy across all bit positions, improves bit‑independence, and helps the generator pass stringent statistical tests that are sensitive to low‑order bias.
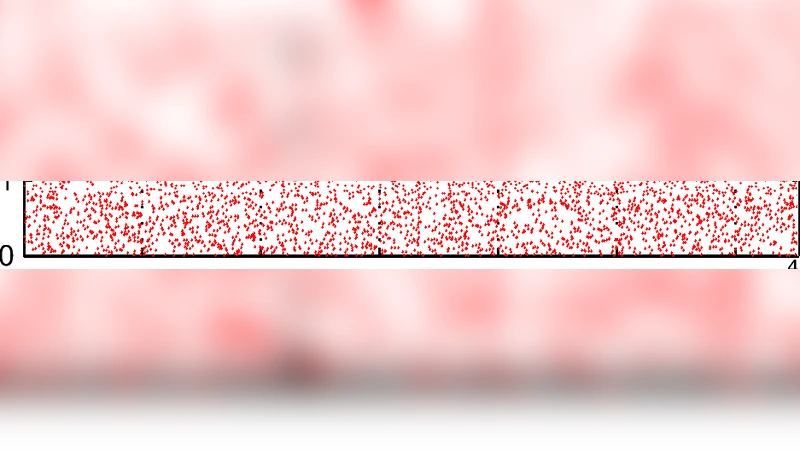
Security analysis includes exhaustive statistical testing using NIST SP800‑22, Dieharder, and TestU01 suites. All tests yielded p‑values well above the 0.01 threshold, with particular improvement observed in the binary matrix rank and LSB‑specific tests due to the perturbation step. The authors also argue that the combined state space—comprising three 64‑bit states plus dynamic coefficient bits—exceeds 2¹²⁸ possible configurations, guaranteeing a minimum period of 2¹²⁸ and rendering brute‑force key‑recovery infeasible.
Performance measurements show that a software implementation on a modern x86‑64 processor can generate approximately 1.2 GB of keystream per second, while a pipelined FPGA design reaches beyond 2 Gbps with modest resource usage (≈200 LUTs). Memory footprint is minimal (three 64‑bit registers plus a small coefficient table), making Trident suitable for embedded and IoT devices.
Potential applications extend beyond stream ciphers; the authors suggest usage in secure token generation, nonce creation for authenticated protocols, and high‑quality random sampling in simulations. They also acknowledge implementation risks: the dynamic coefficient logic adds complexity, and improper selection of coupling weights or perturbation patterns could inadvertently introduce weaknesses. Consequently, they recommend adopting standardized libraries and thorough code audits before deployment.
In summary, Trident advances the state of chaotic‑based PRNGs by integrating dynamic parameter updates, multi‑map coupling, and low‑order‑bit mixing. This combination delivers strong statistical randomness, long periods, and practical throughput, positioning Trident as a viable keystream source for modern cryptographic systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment