A Survey of RFID Authentication Protocols Based on Hash-Chain Method
Security and privacy are the inherent problems in RFID communications. There are several protocols have been proposed to overcome those problems. Hash chain is commonly employed by the protocols to improve security and privacy for RFID authentication. Although the protocols able to provide specific solution for RFID security and privacy problems, they fail to provide integrated solution. This article is a survey to closely observe those protocols in terms of its focus and limitations.
💡 Research Summary
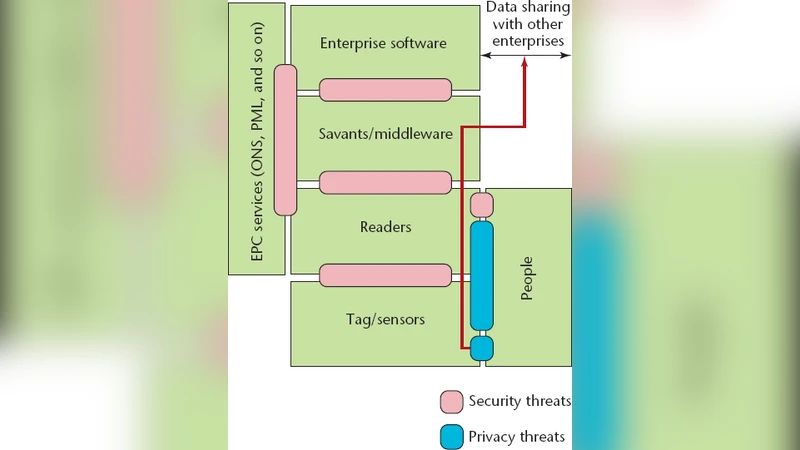
The paper presents a comprehensive survey of RFID authentication protocols that employ the hash‑chain technique, focusing on how each protocol addresses security and privacy concerns and where it falls short. After a brief introduction to RFID technology—its evolution from military identification systems to a cornerstone of the Internet of Things—the authors outline the fundamental security objectives (confidentiality, integrity, availability, authentication, authorization, non‑repudiation, and anonymity) and the specific privacy threats inherent to wireless, tag‑centric environments.
Section 2 categorizes the main attack vectors against RFID: physical tampering, jamming, man‑in‑the‑middle, eavesdropping, traffic analysis, cloning, and replay. Privacy is highlighted as a critical issue because passive tags broadcast static identifiers that can be linked to individuals and locations without the holder’s knowledge.
Section 3 explains the hash‑chain concept. Starting from a seed s, a one‑way hash function h is applied repeatedly to produce hⁿ(s). The “tip” of the chain (hⁿ(s)) cannot be inverted, yet knowledge of a lower‑order element allows verification of the higher‑order one. In RFID, this property enables a tag to send a hash of its current secret (G(sᵢ)) to a reader, then update its secret to H(sᵢ) for the next interaction. The back‑end server stores a list of (ID, sᵢ) pairs and authenticates a tag by recomputing the expected hash values.
Section 4 conducts a comparative analysis of ten representative protocols that adopt this basic scheme:
- Ohkubo et al. (2008) – Refreshes the tag identifier on each read using a hash chain, eliminating the need for random numbers. The protocol, however, is vulnerable to replay attacks.
- Weis et al. – Introduces hash‑locks; a static hash value can be read by any reader, making the tag traceable despite access control.
- Molnar et al. – Uses a hash‑tree to authenticate multiple tags. Loss of a single tag compromises the anonymity of the remaining subtree.
- Henrici – Requires only a hash function on the tag and back‑end management, offering location privacy and resistance to many attacks with a single message exchange. Yet, if the session is interrupted, the tag can be traced.
- Avoine – Modifies Ohkubo’s scheme to mitigate replay attacks but introduces synchronization problems; an attacker can force a tag out of sync with the server.
- Dimitriou – Provides forward privacy and cloning resistance through secret sharing and periodic refresh, but suffers from database‑side desynchronization and is vulnerable to man‑in‑the‑middle attacks.
- Rhee et al. – Proposes a hash‑based challenge‑response protocol that defends against replay and spoofing without updating the tag’s secret. It lacks forward secrecy; compromise of a tag reveals past communications.
- Lee et al. (2010) – Stores the previous identification number on the server to solve desynchronization. Because the hashed identifier remains constant, an active adversary can still trace the tag.
- Lee et al. (different work) – Adds an extra hash operation to protect against cloning, but the absence of a PRNG on low‑cost tags leads to desynchronization attacks.
- Han et al. – Introduces a monitoring component in the back‑end that continuously checks the synchronization of secret values between tag and reader, achieving mutual authentication and improved security, yet the solution incurs higher computational and storage overhead.
Across all protocols, the survey identifies recurring weaknesses: (a) desynchronization between tag and server when updates are missed; (b) lack of forward secrecy, allowing an attacker who captures a tag to reconstruct past sessions; (c) traceability due to static or insufficiently refreshed hash values; (d) availability attacks such as jamming or forced out‑of‑sync states; and (e) resource constraints that prevent the inclusion of robust random number generators or complex key‑management schemes on inexpensive tags.
The authors conclude that while hash‑chain based protocols provide an elegant, low‑cost method for enhancing RFID security, none of the surveyed solutions delivers a fully integrated protection covering privacy, forward secrecy, synchronization resilience, and denial‑of‑service resistance simultaneously. They recommend future research to explore hybrid designs that combine dynamic randomness, secure key‑exchange, and state‑synchronization mechanisms, possibly across the three RFID layers (physical, communication, application). Such a comprehensive approach would be necessary to meet the stringent security and privacy requirements of emerging IoT deployments that rely heavily on RFID technology.
Comments & Academic Discussion
Loading comments...
Leave a Comment