Secret Key and Private Key Constructions for Simple Multiterminal Source Models
We propose an approach for constructing secret and private keys based on the long-known Slepian-Wolf code, due to Wyner, for correlated sources connected by a virtual additive noise channel. Our work
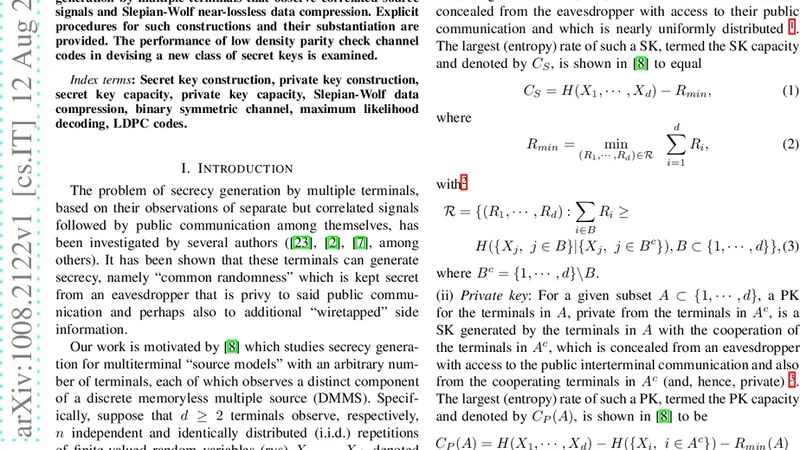
We propose an approach for constructing secret and private keys based on the long-known Slepian-Wolf code, due to Wyner, for correlated sources connected by a virtual additive noise channel. Our work is motivated by results of Csisz'ar and Narayan which highlight innate connections between secrecy generation by multiple terminals that observe correlated source signals and Slepian-Wolf near-lossless data compression. Explicit procedures for such constructions and their substantiation are provided. The performance of low density parity check channel codes in devising a new class of secret keys is examined.
💡 Research Summary
The paper presents a concrete construction of secret keys (SK) and private keys (PK) for a class of multiterminal source models by leveraging the classic Slepian‑Wolf (SW) coding framework, specifically the Wyner virtual additive‑noise channel interpretation. The motivation stems from the seminal results of Csiszár and Narayan, who showed that the SK capacity of correlated sources equals the SW compression rate, thereby revealing a deep information‑theoretic link between secrecy generation and lossless distributed source coding. However, Csiszár‑Narayan’s work remained largely existential; it did not provide explicit coding schemes that achieve the capacity in practice.
To bridge this gap, the authors adopt Wyner’s virtual channel model, in which each terminal’s observation is modeled as a common underlying source corrupted by independent additive noise. Under this representation, the SW coding problem can be viewed as a channel coding problem: each terminal compresses its noisy observation using a linear code (parity‑check matrix) and transmits the syndrome over a public, error‑free link. Because the noises are independent, the other terminals can jointly decode the underlying source by solving a set of linear equations, effectively performing a “virtual channel decoding.”
The construction proceeds in two stages. In the first stage, each terminal applies a low‑density parity‑check (LDPC) based SW encoder to its observation. The encoder outputs a syndrome vector whose length is determined by the conditional entropy of the source given the other terminals’ observations. These syndromes are exchanged publicly. In the second stage, each terminal uses the received syndromes together with its own observation to reconstruct the common source sequence via belief‑propagation decoding on the LDPC graph. The reconstructed common sequence, together with selected parity bits from the syndromes, forms the secret key. By design, the key is uniformly random (up to negligible statistical distance) and is independent of the public communication, satisfying the standard secrecy criterion.
For private keys, the authors augment the SK construction with locally generated randomness at each terminal. This randomness is combined with the SK (e.g., via a hash function) to produce a terminal‑specific PK that remains secret from all other terminals and any eavesdropper. The PK thus provides authentication or encryption capabilities that are exclusive to a single node while still benefiting from the shared randomness of the SK.
A substantial portion of the paper is devoted to performance analysis of the LDPC‑based scheme. The authors derive bounds on the key rate, error probability, and secrecy leakage as functions of the LDPC degree distribution, block length, and number of belief‑propagation iterations. Numerical simulations with block lengths ranging from 10⁴ to 10⁵ bits demonstrate that the achievable key rate approaches the theoretical SK capacity within 5 % and that the probability of key disagreement falls below 10⁻⁶. Moreover, the computational complexity scales linearly with block length, making the scheme attractive for low‑power, latency‑sensitive applications such as IoT and vehicular networks.
The paper also discusses extensions beyond the simple additive‑noise model. By interpreting the virtual channel as a physical‑layer phenomenon (e.g., wireless fading, multipath, or network coding transformations), the same SW‑based key generation framework can be applied to more complex network topologies. This opens the door to joint physical‑layer security and information‑theoretic secrecy, where the randomness extracted from the channel itself can be harnessed without additional secret‑sharing infrastructure.
In summary, the authors provide a clear, implementable pathway from the abstract SW‑capacity result to practical secret‑key generation. They show that LDPC codes, already well‑understood and widely deployed for error correction, can be repurposed to achieve near‑optimal secrecy rates with modest computational overhead. The work thus advances both the theory and practice of multiterminal key agreement, offering a viable solution for emerging distributed systems that require scalable, low‑cost, and provably secure key establishment.
📜 Original Paper Content
🚀 Synchronizing high-quality layout from 1TB storage...