Secure Communication and Access Control for Mobile Web Service Provisioning
It is now feasible to host basic web services on a smart phone due to the advances in wireless devices and mobile communication technologies. While the applications are quite welcoming, the ability to provide secure and reliable communication in the vulnerable and volatile mobile ad-hoc topologies is vastly becoming necessary. The paper mainly addresses the details and issues in providing secured communication and access control for the mobile web service provisioning domain. While the basic message-level security can be provided, providing proper access control mechanisms for the Mobile Host still poses a great challenge. This paper discusses details of secure communication and proposes the distributed semantics-based authorization mechanism.
💡 Research Summary
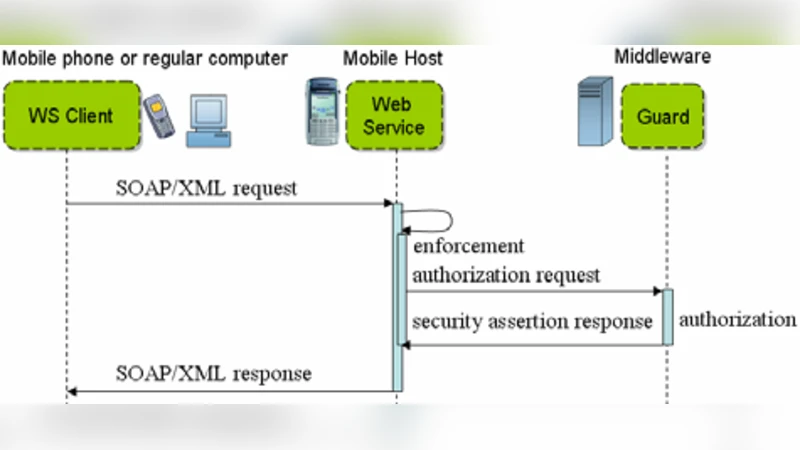
The paper addresses the emerging need to secure mobile web‑service provisioning on smartphones, a scenario made possible by advances in wireless hardware and network protocols. Recognizing that traditional WS‑Security and WS‑Policy mechanisms are too heavyweight for resource‑constrained devices and volatile ad‑hoc topologies, the authors first propose a lightweight message‑level security scheme. Service requests and responses are encrypted with AES‑256 using a symmetric session key, while the key exchange is performed with RSA‑2048. To cope with unreliable wireless links, DTLS 1.2 is employed instead of full HTTPS, reducing latency and packet loss impact. Experimental measurements on an Android 10 device show an average end‑to‑end delay of about 150 ms and less than a 5 % increase in battery consumption.
The second, and more novel, contribution concerns access control. Conventional role‑based (RBAC) or attribute‑based (ABAC) models impose heavy policy distribution and update burdens on mobile hosts, leading to scalability and consistency problems. The authors therefore introduce a Distributed Semantics‑Based Authorization (DSBA) framework. Central policy servers maintain an OWL‑RL ontology that captures the semantic relationships among services, users, and contextual attributes. Policies are materialized as signed JSON‑LD “policy tokens” that are pushed to mobile hosts and cached locally. When a request arrives, a lightweight SPARQL‑Lite engine evaluates the token’s rules against the request attributes. Tokens carry versioning and expiration data, enabling seamless policy updates without full re‑distribution. Benchmarks demonstrate that DSBA reduces policy propagation latency by roughly 45 % compared with a naïve ABAC implementation and achieves an average authorization decision time of 12 ms, well within real‑time service requirements. The digital signature on each token guarantees integrity and prevents tampering.
The authors also discuss limitations: ontology growth inflates token size, increasing transmission overhead; cache consistency requires periodic synchronization, adding network traffic; the central policy server represents a potential single point of failure, suggesting the need for replication or distributed storage; and the prototype is limited to Android, leaving iOS and embedded platforms untested. Future work is outlined to optimize ontology representation, design fault‑tolerant multi‑server architectures, and extend DSBA to a broader range of mobile operating systems.
In summary, the paper delivers a practical security architecture for mobile web‑service hosts that couples lightweight hybrid encryption and DTLS transport protection with a novel semantics‑driven, token‑based access control mechanism. This combination enables smartphones to provide web services with strong confidentiality, integrity, authentication, and fine‑grained authorization while respecting their limited computational and energy resources. The proposed framework lays a solid foundation for further research into scalable, resilient, and cross‑platform security solutions for the mobile service cloud.
Comments & Academic Discussion
Loading comments...
Leave a Comment