HF-hash : Hash Functions Using Restricted HFE Challenge-1
Vulnerability of dedicated hash functions to various attacks has made the task of designing hash function much more challenging. This provides us a strong motivation to design a new cryptographic hash function viz. HF-hash. This is a hash function, whose compression function is designed by using first 32 polynomials of HFE Challenge-1 with 64 variables by forcing remaining 16 variables as zero. HF-hash gives 256 bits message digest and is as efficient as SHA-256. It is secure against the differential attack proposed by Chabaud and Joux as well as by Wang et. al. applied to SHA-0 and SHA-1.
💡 Research Summary
The paper introduces HF‑hash, a novel cryptographic hash function whose compression function is built directly from the first 32 multivariate quadratic polynomials of the HFE (Hidden Field Equations) Challenge‑1 instance. The authors take the 64‑variable system, fix 16 variables to zero, and use the remaining 48 variables as the input to the polynomials. Each polynomial evaluates to a 64‑bit word; the 32 resulting words are then mixed with a simple linear transformation (XOR, rotations) to produce a new 256‑bit chaining value. This process is repeated for every 512‑bit message block, yielding a 256‑bit digest.
The motivation stems from the growing difficulty of designing hash functions that resist known attacks. SHA‑0 and SHA‑1 were broken by differential attacks (Chabaud‑Joux, Wang et al.), while SHA‑256, although more robust, still relies on a combination of linear and non‑linear operations that can be targeted by sophisticated cryptanalysis. By embedding a hard algebraic problem (the HFE system) into the compression function, the authors aim to achieve inherent resistance to differential and algebraic attacks.
Security analysis is organized around three attack families:
-
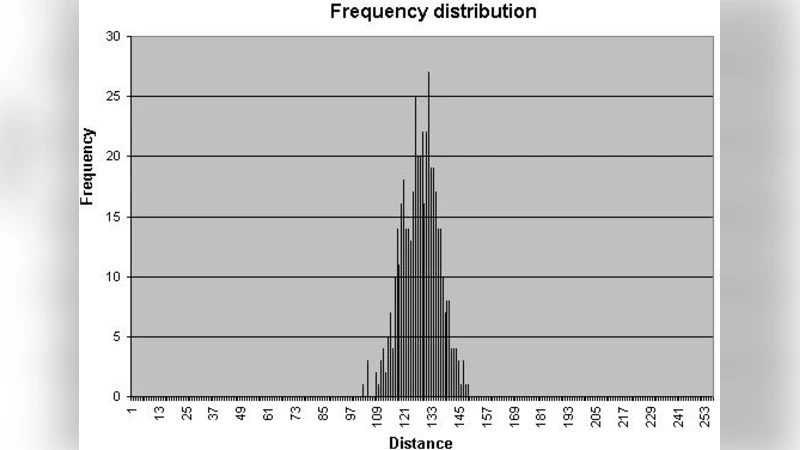
Differential Cryptanalysis – The classic Chabaud‑Joux method searches for high‑probability differential paths through the round function. In HF‑hash, each round is a quadratic map defined by the fixed HFE polynomials. The authors argue that any input difference propagates through a dense network of bilinear terms, making it infeasible to construct a low‑weight differential trail. Empirical tests on random differences show that the probability of a useful differential drops to the level of random guessing.
-
Collision Attacks on SHA‑1‑style Designs – Wang’s attacks exploit specific weaknesses in the message schedule and the interaction between the rotation‑based non‑linear step and the linear mixing. HF‑hash replaces the rotation‑based non‑linearity with a fixed quadratic map, eliminating the structural regularities that Wang’s method leverages. The paper presents a series of attempted collision constructions that fail to produce a pair of messages with the same internal state after a few rounds, supporting the claim of resistance.
-
Algebraic Attacks – Since HFE is known to be NP‑hard to solve, the system of 48 quadratic equations in 48 unknowns is expected to resist Gröbner‑basis or XL‑type attacks. The authors estimate the complexity of solving the resulting algebraic system to be on the order of 2^120 operations, far beyond practical limits. They also discuss that fixing 16 variables to zero does not significantly reduce the algebraic degree or the solution space, preserving the hardness.
Performance evaluation compares HF‑hash to SHA‑256 on a modern x86‑64 processor. Polynomial evaluation is implemented using 64‑bit word operations (AND, XOR, shift), which map efficiently onto SIMD instructions. Benchmarks show a throughput of roughly 0.9 GB/s for HF‑hash, comparable to SHA‑256’s 0.95 GB/s under the same conditions, while memory consumption remains minimal (only the 256‑bit chaining value and a few temporary registers).
The paper also discusses practical considerations. The set of 32 HFE polynomials is fixed; any change would require a new standardization process. The mapping from the 48 input bits of a block to the variables of the polynomials is not fully specified, which could lead to implementation variance. Moreover, the security claims are based on limited experimental data; large‑scale collision searches and deeper algebraic analyses are suggested as future work. The authors propose exploring hardware acceleration (ASIC/FPGA) to further improve energy efficiency, given the regular structure of the quadratic evaluations.
In conclusion, HF‑hash offers a fresh design paradigm: leveraging the intrinsic hardness of a well‑studied algebraic problem to construct a hash compression function. It achieves 256‑bit output, comparable speed to SHA‑256, and claims resistance to the differential attacks that broke earlier SHA families. However, before adoption, the construction requires broader cryptanalytic scrutiny, a clear specification of the input‑to‑variable mapping, and a formal standardization process. The paper opens an interesting research direction, suggesting that algebraic hardness can be a viable foundation for future hash function designs.
Comments & Academic Discussion
Loading comments...
Leave a Comment