Radio Frequency Identification (RFID) technology one of the most promising technologies in the field of ubiquitous computing. Indeed, RFID technology may well replace barcode technology. Although it offers many advantages over other identification systems, there are also associated security risks that are not easy to be addressed. When designing a real lightweight authentication protocol for low cost RFID tags, a number of challenges arise due to the extremely limited computational, storage and communication abilities of Low-cost RFID tags. This paper proposes a real mutual authentication protocol for low cost RFID tags. The proposed protocol prevents passive attacks as active attacks are discounted when designing a protocol to meet the requirements of low cost RFID tags. However the implementation of the protocol meets the limited abilities of low cost RFID tags.
Deep Dive into Lightweight Mutual Authentication Protocol for Low Cost RFID Tags.
Radio Frequency Identification (RFID) technology one of the most promising technologies in the field of ubiquitous computing. Indeed, RFID technology may well replace barcode technology. Although it offers many advantages over other identification systems, there are also associated security risks that are not easy to be addressed. When designing a real lightweight authentication protocol for low cost RFID tags, a number of challenges arise due to the extremely limited computational, storage and communication abilities of Low-cost RFID tags. This paper proposes a real mutual authentication protocol for low cost RFID tags. The proposed protocol prevents passive attacks as active attacks are discounted when designing a protocol to meet the requirements of low cost RFID tags. However the implementation of the protocol meets the limited abilities of low cost RFID tags.
Radio Frequency Identification (RFID) system is the latest technology that plays an important role for object identification as ubiquitous infrastructure. RFID has many applications in access control, manufacturing automation, maintenance, supply chain management, parking garage management, automatic payment, tracking, and inventory control.
EPCglobal is a member-driven organization composed of leading firms and industries that are focused on creating global standards for the EPCglobal Network. EPCglobal is now leading the development of industry-driven standards for the Electronic Product Code (EPC) Network to support the use of Radio Frequency Identification (RFID) in today’s fast-moving, information rich trading networks [13].
An RFID system consists of three different components: RFID tag or transponder, Reader or interrogator, and backend server.
RFID tag: is a tiny radio chip that comprises a simple silicon microchip attached to a small flat aerial and mounted on a substrate. The whole device can then be encapsulated in different materials (such as plastic) dependent upon its intended usage. The tag can be attached to an object, typically an item, box, or pallet, and read remotely to ascertain its identity, position, or state. For an active tag there will also be a battery.
Reader or Interrogator: sends and receives RF data to and from the tag via antennas. A reader may have multiple antennas that are responsible for sending and receiving radio waves. Host Computer (backend server): the data acquired by the readers is then passed to a host computer, which may run specialist RFID software or middleware to filter the data and route it to the correct application, to be processed into useful information.
RFID offer several advantages over barcodes: data are read automatically, line of sight not required, and through non-conducting materials at high rate and far distance. The reader can read the contents of the tags by broadcasting RF signals via antennas. The tags data acquired by the readers is then passed to a host computer, which may run middleware (API). Middleware offers processing modules or services to reduce load and network traffic within the back-end systems. RFID basic operations can be summarized as in Figure 3. RFID systems are vulnerable to a broad range of malicious attacks ranging from passive eavesdropping to active interference. Unlike in wired networks, where computing systems typically have both centralized and host-based defenses (e.g. firewalls), attacks against RFID networks can target decentralized parts of the system infrastructure, since RFID readers and RFID tags operate in an inherently unstable and potentially noisy environment. Additionally, RFID technology is evolving quickly -the tags are multiplying and shrinking -and so the threats they are susceptible to, are similarly evolving. Thus, it becomes increasingly difficult to have a global view of the problem [1].
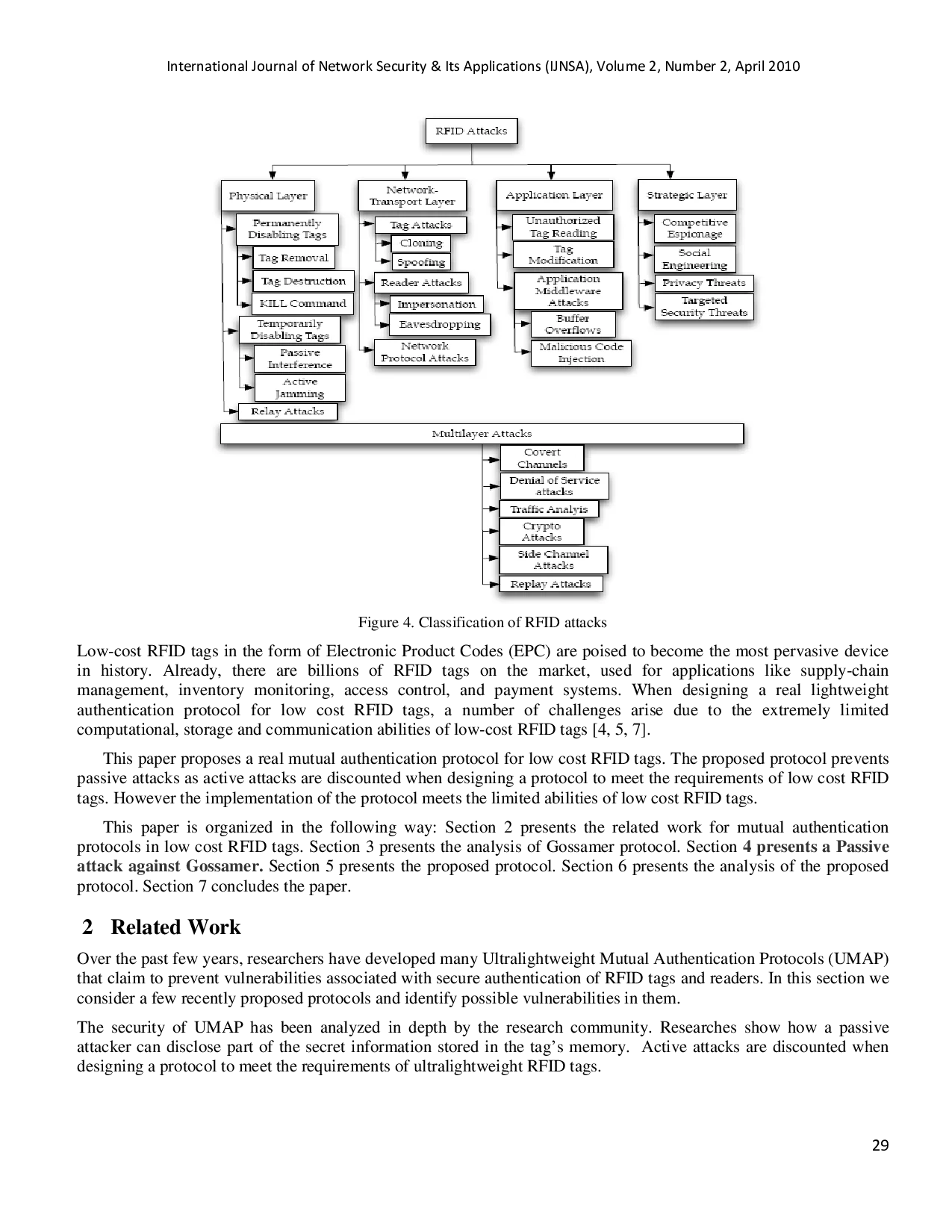
RFID tags may pose a considerable security and privacy risk to organizations and individuals using them. Since a typical tag answers its ID to any reader and the replied ID is always the same, an attacker can easily hack the system by reading out the data of a tag and duplicating it to bogus tags. Unprotected tags may have vulnerabilities to eavesdropping, location privacy, spoofing, or denial of service (DoS). Unauthorized readers may compromise privacy by accessing tags without adequate access control. Even when the content of the tags is protected, individuals may be tracked through predictable tag responses. Even though many cryptographic primitives can be used to remove these vulnerabilities, they cannot be applied to a RFID system due to the prohibitive cost of including protection for each and every RFID tag [3]. Low-cost RFID tags in the form of Electronic Product Codes (EPC) are poised to become the most pervasive device in history. Already, there are billions of RFID tags on the market, used for applications like supply-chain management, inventory monitoring, access control, and payment systems. When designing a real lightweight authentication protocol for low cost RFID tags, a number of challenges arise due to the extremely limited computational, storage and communication abilities of low-cost RFID tags [4,5,7]. This paper proposes a real mutual authentication protocol for low cost RFID tags. The proposed protocol prevents passive attacks as active attacks are discounted when designing a protocol to meet the requirements of low cost RFID tags. However the implementation of the protocol meets the limited abilities of low cost RFID tags. This paper is organized in the following way: Section 2 presents the related work for mutual authentication protocols in low cost RFID tags. Section 3 presents the analysis of Gossamer protocol. Section 4 presents a Passive attack against Gossamer. Section 5 presents the proposed protocol. Section 6 presents the analysis of the proposed protocol. Section 7 concludes t
…(Full text truncated)…
This content is AI-processed based on ArXiv data.