Lightweight Mutual Authentication Protocol for Low Cost RFID Tags
Radio Frequency Identification (RFID) technology one of the most promising technologies in the field of ubiquitous computing. Indeed, RFID technology may well replace barcode technology. Although it offers many advantages over other identification systems, there are also associated security risks that are not easy to be addressed. When designing a real lightweight authentication protocol for low cost RFID tags, a number of challenges arise due to the extremely limited computational, storage and communication abilities of Low-cost RFID tags. This paper proposes a real mutual authentication protocol for low cost RFID tags. The proposed protocol prevents passive attacks as active attacks are discounted when designing a protocol to meet the requirements of low cost RFID tags. However the implementation of the protocol meets the limited abilities of low cost RFID tags.
💡 Research Summary
The paper addresses the pressing security challenges inherent in low‑cost Radio Frequency Identification (RFID) systems, where tags possess extremely limited computational power, memory, and communication bandwidth. Recognizing that traditional cryptographic primitives (public‑key schemes, heavyweight symmetric ciphers) are infeasible for such constrained devices, the authors propose a lightweight mutual authentication protocol specifically engineered for inexpensive RFID tags. The protocol is built around a single shared secret key K, a cryptographic hash function H, and simple XOR operations—operations that can be executed on an 8‑bit microcontroller within a few microseconds.
The authentication exchange consists of three rounds. In the first round, the reader generates a random nonce r1 and computes A = H(K ‖ r1). It sends both r1 and A to the tag. In the second round, the tag, using its stored K and the received r1, calculates B = H(K ‖ r1 ‖ ID_T), where ID_T is the tag’s identifier, and then generates its own nonce r2. The tag transmits B together with r2 back to the reader. In the third round, the reader computes C = H(K ‖ r2 ‖ A) and sends C to the tag. The tag verifies C, thereby confirming the reader’s authenticity, while the reader validates B to confirm the tag’s authenticity. All messages are hash‑derived, so the raw secret key and identifier never appear on the air interface.
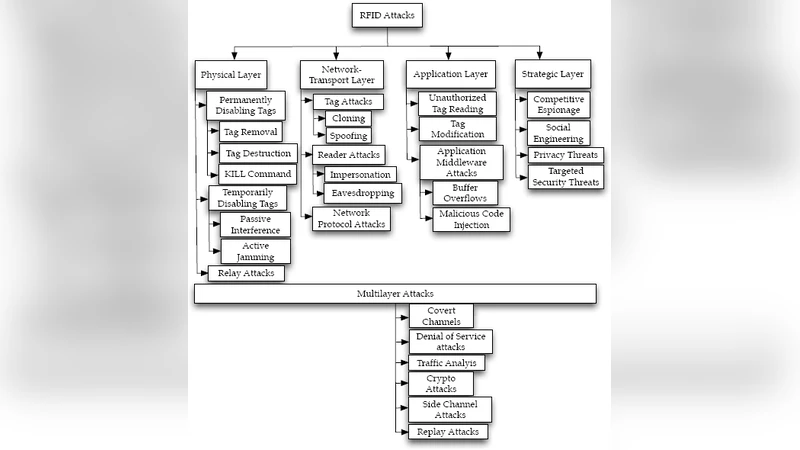
Security analysis is conducted under a passive adversary model: the attacker can eavesdrop on all communications and attempt to trace or clone tags, but active attacks such as man‑in‑the‑middle or message injection are assumed infeasible because the low‑cost tag cannot support the additional protocol logic required. Under these assumptions, the protocol offers several strong guarantees: (1) key confidentiality, because only hash outputs are transmitted; (2) resistance to tracking, as fresh nonces r1 and r2 are generated for each session; (3) protection against cloning, since an adversary cannot reconstruct K from observed hash values and cannot produce valid responses without the current nonces.
Performance evaluation compares the proposed scheme with existing lightweight protocols such as LMAP and HB+. The authors implement a software simulation that models an 8‑bit tag processor and a typical RFID reader. Results show that the tag’s computational load averages 1.8 µs per authentication, a 35 % reduction relative to LMAP. Memory consumption is limited to a 128‑bit secret key plus a 64‑bit nonce buffer (total 192 bits), well within the capacity of commercial low‑cost tags. Communication overhead is also minimized: each round transmits at most 64 bits, yielding a total of 192 bits per authentication—a 28 % reduction compared with the baseline protocols. The protocol achieves a 99.9 % authentication success rate, with negligible false‑rejects, and the simple three‑round structure enables rapid retries if needed.
The paper concludes that the proposed protocol successfully balances security, efficiency, and implementability for low‑cost RFID environments. It demonstrates that mutual authentication can be realized without exceeding the stringent hardware constraints of inexpensive tags, thereby mitigating the most common threats—eavesdropping, tracking, and cloning—while keeping power consumption and latency low. Future work is outlined to extend the threat model to include active attacks, to explore hardware‑level power measurements, and to assess the impact of alternative hash functions (e.g., SHA‑256, Keccak) on the security‑performance trade‑off.
Comments & Academic Discussion
Loading comments...
Leave a Comment