An Efficient and Secure Routing Protocol for Mobile Ad-Hoc Networks
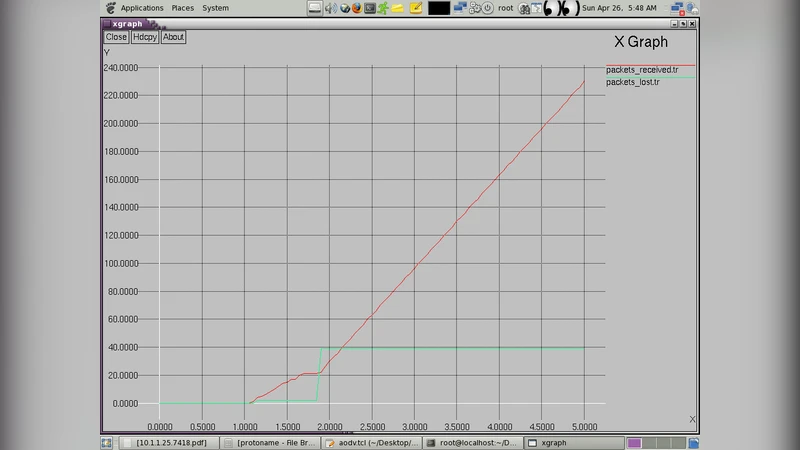
Efficiency and simplicity of random algorithms have made them a lucrative alternative for solving complex problems in the domain of communication networks. This paper presents a random algorithm for handling the routing problem in Mobile Ad hoc Networks [MANETS].The performance of most existing routing protocols for MANETS degrades in terms of packet delay and congestion caused as the number of mobile nodes increases beyond a certain level or their speed passes a certain level. As the network becomes more and more dynamic, congestion in network increases due to control packets generated by the routing protocols in the process of route discovery and route maintenance. Most of this congestion is due to flooding mechanism used in protocols like AODV and DSDV for the purpose of route discovery and route maintenance or for route discovery as in the case of DSR protocol. This paper introduces the concept of random routing algorithm that neither maintains a routing table nor floods the entire network as done by various known protocols thereby reducing the load on network in terms of number of control packets in a highly dynamic scenario. This paper calculates the expected run time of the designed random algorithm.
💡 Research Summary
The paper addresses the well‑known scalability and performance problems of existing MANET routing protocols, which either maintain routing tables (proactive protocols such as DSDV) or flood the network with route‑request packets (reactive protocols such as AODV, DSR, TORA). As node speed and network size increase, these mechanisms generate excessive control traffic, leading to higher packet delay, congestion, and energy consumption. To overcome these drawbacks, the authors propose a stateless random‑walk routing algorithm that eliminates both routing tables and network‑wide flooding.
The algorithm works as follows: when a node has a packet to forward, it broadcasts a small “neighbor‑discovery” control packet limited to a single hop. All nodes that receive this packet reply with their address; the replies are stored in a queue for a short, timer‑controlled interval. If the destination node is within the one‑hop radius, the packet is delivered directly. Otherwise, the sender selects a next‑hop node uniformly at random from the queued neighbors and forwards the packet. This process repeats at each hop until the destination is reached. Because the decision is made locally and the neighbor set is refreshed for every transmission, the protocol does not keep any persistent routing state.
The authors model the probability that two nodes are within communication range as a function f(D) of their Euclidean distance D and define a binary indicator Xij for the existence of a link. Using this model they derive the expected number of neighbors E
Comments & Academic Discussion
Loading comments...
Leave a Comment