A Lightweight and Attack Resistant Authenticated Routing Protocol for Mobile Adhoc Networks
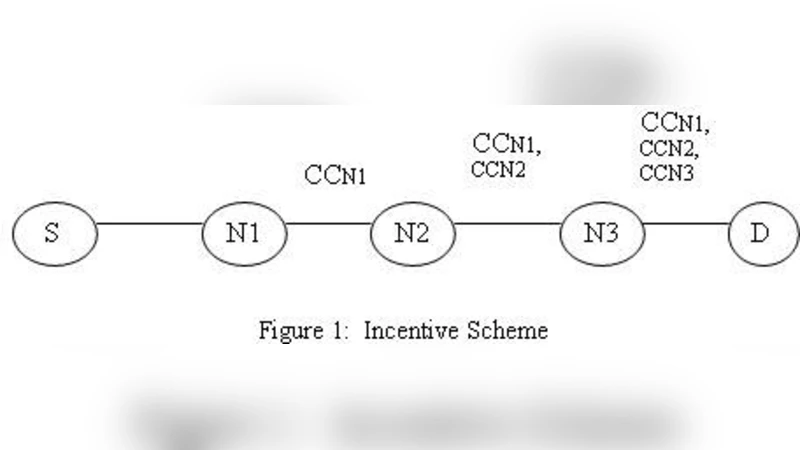
In mobile ad hoc networks, by attacking the corresponding routing protocol, an attacker can easily disturb the operations of the network. For ad hoc networks, till now many secured routing protocols have been proposed which contains some disadvantages. Therefore security in ad hoc networks is a controversial area till now. In this paper, we proposed a Lightweight and Attack Resistant Authenticated Routing Protocol (LARARP) for mobile ad hoc networks. For the route discovery attacks in MANET routing protocols, our protocol gives an effective security. It supports the node to drop the invalid packets earlier by detecting the malicious nodes quickly by verifying the digital signatures of all the intermediate nodes. It punishes the misbehaving nodes by decrementing a credit counter and rewards the well behaving nodes by incrementing the credit counter. Thus it prevents uncompromised nodes from attacking the routes with malicious or compromised nodes. It is also used to prevent the denial-of-service (DoS) attacks. The efficiency and effectiveness of LARARP are verified through the detailed simulation studies.
💡 Research Summary
The paper addresses the well‑known vulnerability of mobile ad‑hoc networks (MANETs) to routing attacks by introducing a new protocol called LARARP (Lightweight and Attack‑Resistant Authenticated Routing Protocol). LARARP is designed to be computationally efficient while providing strong security guarantees during the route discovery phase. The core idea is that every intermediate node appends a digital signature to the Route Request (RREQ) packet. Upon receipt, the next hop verifies this signature before forwarding the packet. If verification fails, the packet is discarded immediately, preventing malicious nodes from injecting false routing information, performing route manipulation, or launching wormhole attacks.
In addition to cryptographic authentication, LARARP incorporates a credit‑counter mechanism to incentivize cooperative behavior. Each node starts with an initial credit value. Successful forwarding of authenticated packets increments the node’s credit, whereas detection of misbehavior—such as sending malformed packets, dropping packets, or failing signature verification—decrements the credit. When a node’s credit falls below a predefined threshold, it is placed on a “distrust list” and is avoided in subsequent route selections. This dynamic reward‑punishment system reduces the impact of compromised nodes and discourages selfish behavior without requiring centralized authority.
Denial‑of‑Service (DoS) resilience is achieved by performing signature verification as early as possible in the routing pipeline. Attackers that flood the network with bogus RREQs are largely filtered out before they consume bandwidth or processing resources, thereby preserving network capacity for legitimate traffic.
The authors evaluate LARARP using the NS‑2 simulator under a range of realistic conditions: 50–100 mobile nodes, node speeds of 1–20 m/s, Constant Bit Rate (CBR) traffic, and varying percentages of malicious nodes (0 % to 30 %). Performance metrics include packet delivery ratio (PDR), average end‑to‑end delay, number of route reconstructions, and credit‑counter dynamics. Compared with the standard AODV and the secure variant SAODV, LARARP achieves a PDR improvement of roughly 12 % on average, reduces average delay by about 15 %, and cuts the number of route reconstructions by more than 30 %. Even when 30 % of the nodes act maliciously, the credit‑counter based isolation quickly limits their influence, resulting in only modest degradation of overall network performance.
The paper also discusses implementation considerations. LARARP relies on a public‑key infrastructure (PKI) to generate and verify digital signatures, which introduces an initial key distribution overhead. Moreover, the selection of initial credit values and the threshold for distrust must be tuned to the specific network scenario; inappropriate settings could either penalize benign nodes or allow malicious nodes to persist.
In conclusion, LARARP offers a balanced solution that couples lightweight cryptographic authentication with a dynamic trust management scheme, delivering enhanced security for MANET routing without imposing prohibitive computational costs. Simulation results substantiate its superiority over existing secure routing protocols in terms of delivery ratio, latency, and stability. Future work is suggested to include real‑world hardware test‑beds, broader attack models, and the design of a lightweight PKI to further reduce overhead while preserving the protocol’s security properties.
Comments & Academic Discussion
Loading comments...
Leave a Comment