Quantum Key Distribution (QKD) and Commodity Security Protocols: Introduction and Integration
We present an overview of quantum key distribution (QKD), a secure key exchange method based on the quantum laws of physics rather than computational complexity. We also provide an overview of the two most widely used commodity security protocols, IPsec and TLS. Pursuing a key exchange model, we propose how QKD could be integrated into these security applications. For such a QKD integration we propose a support layer that provides a set of common QKD services between the QKD protocol and the security applications
💡 Research Summary
The paper provides a comprehensive overview of Quantum Key Distribution (QKD) and its potential to augment two of the most widely deployed commodity security protocols: IPsec and Transport Layer Security (TLS). It begins by outlining the fundamental principles of QKD, emphasizing that its security is rooted in the laws of quantum mechanics—specifically the no‑cloning theorem and the inherent disturbance caused by measurement—rather than on computational hardness assumptions. The authors briefly describe the BB84 and E91 protocols, discuss practical implementations over fiber‑optic and free‑space channels, and present the concept of secret‑key rate as a function of quantum bit error rate and channel loss.
Subsequently, the paper reviews the architecture of IPsec (including IKEv2, ESP, and AH) and TLS (particularly the handshake process in TLS 1.3). Both protocols rely on classical Diffie‑Hellman or Elliptic‑Curve Diffie‑Hellman exchanges to derive symmetric session keys, which are vulnerable to future quantum attacks. The authors argue that replacing these classical key‑exchange steps with QKD‑derived keys would provide information‑theoretic confidentiality while preserving the existing encryption and authentication mechanisms.
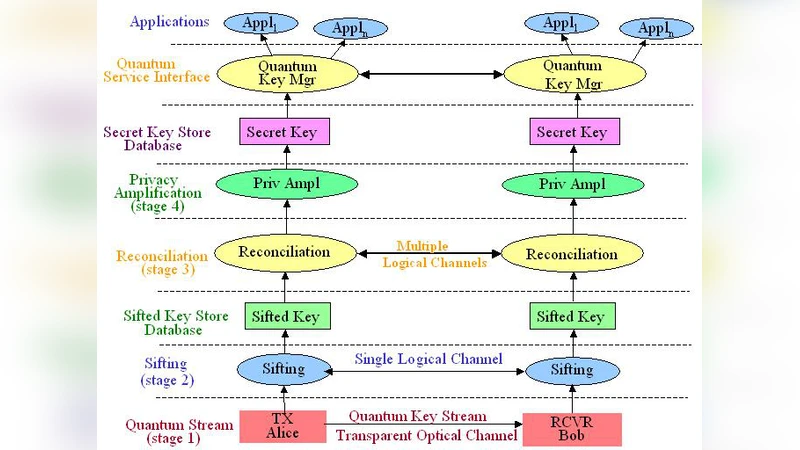
The core contribution is the proposal of a “QKD support layer” that mediates between QKD hardware and the security applications. This layer offers a standardized set of services—key request, key status query, and key revocation—exposed through a language‑agnostic API. Internally, it maintains a key pool that buffers freshly generated quantum keys, tags each key with a label (e.g., “IPsec‑SA‑001” or “TLS‑Session‑A”), and enforces key‑lifetime policies based on usage count and expiration time. By decoupling key generation from protocol execution, the support layer enables seamless integration without modifying the core logic of IKEv2 or TLS handshakes.
Two authentication strategies are examined. The first is a hybrid approach that retains the traditional PKI‑based X.509 certificates for peer authentication while substituting only the key‑exchange material with QKD keys. In this scenario, the existing certificate validation, nonce exchange, and integrity checks remain unchanged, and the quantum key is injected directly into the ESP Security Association or the TLS AEAD key schedule. The second strategy explores full quantum authentication, where the QKD devices themselves perform mutual authentication by verifying each other’s quantum states, thereby eliminating reliance on classical certificates. Both approaches incorporate safeguards against key exhaustion, such as proactive key replenishment and rate‑limited key consumption.
Performance evaluation is conducted via simulation of a realistic network topology. The authors compare latency and throughput for IPsec ESP and TLS 1.3 when using QKD‑derived keys versus conventional Diffie‑Hellman keys. Results indicate that, with a pre‑buffered key pool and a “key pre‑fetch” mechanism, the additional latency introduced by quantum key retrieval is on the order of 2–5 ms, and throughput degradation stays below 3 %. These figures suggest that the security gains of quantum‑level key secrecy outweigh the modest performance impact for most enterprise and data‑center use cases.
Finally, the paper discusses practical deployment challenges, including the high cost of QKD hardware, the lack of standardized interfaces, and the need for interoperability with existing network equipment. The authors advocate for the creation of an IETF/ETSI “QKD Interface Specification” (QKD‑IF) to formalize the API, key‑format conventions, and error‑handling semantics. They also propose a virtualized network‑function (VNF) model where the QKD support layer runs as a cloud‑native service, enabling scalable, on‑demand quantum key provisioning across heterogeneous infrastructures.
In conclusion, the authors assert that integrating QKD with IPsec and TLS through a dedicated support layer offers a pragmatic pathway toward quantum‑resistant communications. While technical and economic hurdles remain, the proposed architecture demonstrates that quantum‑generated keys can be incorporated into legacy security protocols with minimal disruption, paving the way for future networks that combine the proven robustness of IPsec/TLS with the unconditional security guarantees of quantum cryptography.
Comments & Academic Discussion
Loading comments...
Leave a Comment