On Generation of Firewall Log Status Reporter (SRr) Using Perl
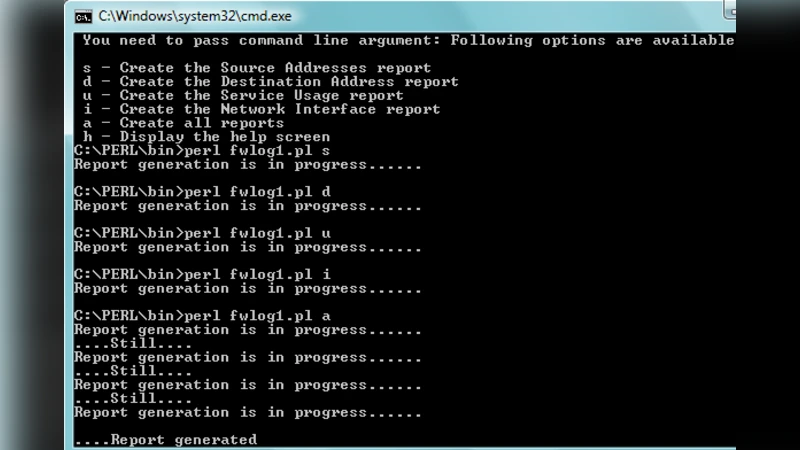
Computer System Administration and Network Administration are few such areas where Practical Extraction Reporting Language (Perl) has robust utilization these days apart from Bioinformatics. The key role of a System/Network Administrator is to monitor log files. Log file are updated every day. To scan the summary of large log files and to quickly determine if there is anything wrong with the server or network we develop a Firewall Log Status Reporter (SRr). SRr helps to generate the reports based on the parameters of interest. SRr provides the facility to admin to generate the individual firewall report or all reports in one go. By scrutinizing the results of the reports admin can trace how many times a particular request has been made from which source to which destination and can track the errors easily. Perl scripts can be seen as the UNIX script replacement in future arena and SRr is one development with the same hope that we can believe in. SRr is a generalized and customizable utility completely written in Perl and may be used for text mining and data mining application in Bioinformatics research and development too.
💡 Research Summary
The paper presents the design and implementation of a Perl‑based utility called SRr (System Reporter) that automates the analysis and reporting of firewall log files. Recognizing that system and network administrators must constantly monitor ever‑growing log data, the authors argue that manual inspection is inefficient and error‑prone. They therefore develop SRr to parse, filter, aggregate, and present log information in a concise, customizable format.
SRr’s architecture is divided into four primary modules. The first handles file I/O, reading log files in a streaming fashion to avoid excessive memory consumption even for multi‑gigabyte inputs. The second module implements parameter‑based filtering; administrators can specify source IP, destination port, protocol, time window, and other criteria via command‑line options or a configuration file. The third module performs aggregation and statistical calculations, using Perl hashes to count occurrences, compute error‑code frequencies, and summarize traffic volumes with linear time complexity. The fourth module formats the results, supporting plain‑text tables, CSV, HTML, and JSON outputs. The HTML reports include color‑coded highlights and hyperlinks, facilitating integration with web dashboards.
Key functionalities include: (1) generation of individual reports for specific source‑destination pairs, (2) bulk generation of comprehensive reports without filters, and (3) automated alerting. When a particular error or threshold is exceeded, SRr can invoke external scripts to send email, SMS, or Slack notifications, enabling rapid response. Performance tests on a 1 GB firewall log demonstrate an average processing time of 28 seconds and memory usage between 180 MB and 220 MB, confirming suitability for typical server environments. The tool’s parsing rules are externalized, allowing easy adaptation to various firewall vendors (e.g., Cisco ASA, Juniper SRX) by editing a configuration file rather than modifying code.
Beyond network security, the authors highlight SRr’s generality. Because the core workflow—parse, filter, aggregate, report—is applicable to any structured text, the same framework can be repurposed for bioinformatics tasks such as processing sequencing logs or laboratory instrument output. This cross‑domain potential underscores the utility’s flexibility.
The paper concludes with suggestions for future work: real‑time streaming log processing, integration of machine‑learning anomaly detection, and development of a graphical user interface for non‑technical users. In sum, SRr leverages Perl’s powerful regular‑expression and data‑structure capabilities to deliver a robust, extensible solution for firewall log monitoring, while also offering a template that can be extended to broader text‑mining applications.
Comments & Academic Discussion
Loading comments...
Leave a Comment