Quantum Three-Pass protocol: Key distribution using quantum superposition states
This letter proposes a novel key distribution protocol with no key exchange in advance, which is secure as the BB84 quantum key distribution protocol. Our protocol utilizes a photon in superposition state for single-bit data transmission instead of a classical electrical/optical signal. The security of this protocol relies on the fact, that the arbitrary quantum state cannot be cloned, known as the no-cloning theorem. This protocol can be implemented with current technologies.
💡 Research Summary
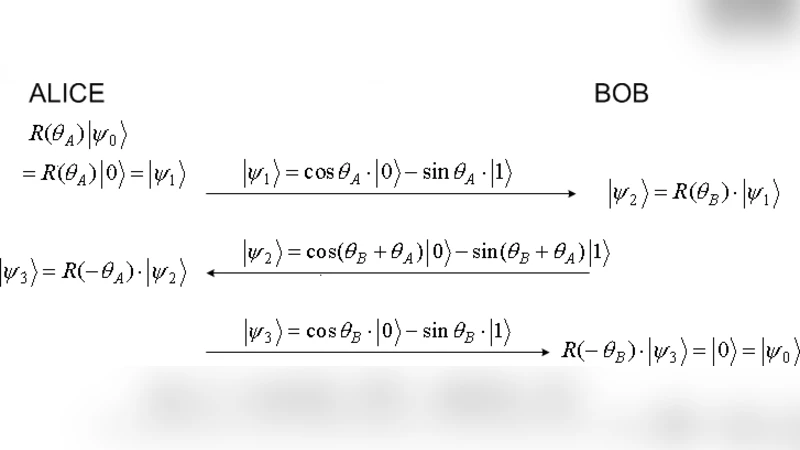
The paper introduces a novel quantum key distribution scheme called the Quantum Three‑Pass Protocol (Q3P), which eliminates the need for any pre‑shared secret or basis agreement between the communicating parties. The protocol is inspired by Shamir’s classical three‑pass encryption but is realized entirely with quantum superposition states of single photons. In the first pass, Alice prepares a qubit in an arbitrary superposition |ψ⟩ = α|0⟩ + βe^{iθ_A}|1⟩, where the amplitudes and phase are chosen secretly. She sends this photon to Bob. In the second pass, Bob applies his own unitary operation U_B(θ_B, φ_B) – for example a rotation on the Bloch sphere – and returns the modified photon to Alice. In the third pass, Alice removes her own operation by applying the inverse U_A†, leaving a state that encodes only Bob’s transformation of the original bit. Bob finally applies the inverse of his operation U_B†, measures in the computational basis, and recovers the original classical bit that Alice intended to transmit.
Security rests on two fundamental quantum principles. First, the no‑cloning theorem guarantees that an eavesdropper (Eve) cannot make a perfect copy of the unknown superposition, so any attempt to intercept and duplicate the photon inevitably disturbs the state. Second, quantum measurement is inherently invasive; any measurement performed by Eve collapses the superposition, producing detectable errors when Alice and Bob compare a subset of their bits. The authors analyze three attack models: simple interception, man‑in‑the‑middle, and cloning attacks. In each case, the protocol’s random, secret unitaries on both sides ensure that Eve cannot predict the final state, and any deviation from the expected error rate reveals her presence.
From an implementation perspective, the protocol requires only standard components: a single‑photon source, polarization or path‑based superposition preparation, fast electro‑optic phase modulators to enact the secret unitaries, low‑loss optical fiber for transmission, and single‑photon detectors for measurement. The authors argue that current technology can achieve the necessary fidelity, and they provide simulation results showing that, after applying error‑correction and privacy‑amplification, the secret‑key rate of Q3P matches or slightly exceeds that of BB84 under comparable loss and detector‑efficiency conditions.
The paper also discusses practical limitations. Photon loss, detector dark counts, and imperfect unitary implementations introduce a baseline quantum bit error rate (QBER). However, the protocol’s structure allows straightforward integration of existing QKD post‑processing techniques to keep the QBER below the security threshold. Moreover, because no basis reconciliation is required, the classical communication overhead is reduced, simplifying the overall system architecture.
In conclusion, the Quantum Three‑Pass Protocol offers a conceptually simple yet powerful alternative to conventional QKD. By leveraging the impossibility of cloning arbitrary quantum states and the disturbance caused by measurement, it achieves unconditional security without any prior key exchange. Its reliance on readily available optical hardware makes it a promising candidate for near‑term deployment in fiber‑based quantum networks, and the authors suggest future work on multi‑bit extensions, network routing, and integration with quantum memory for long‑distance applications.
Comments & Academic Discussion
Loading comments...
Leave a Comment