Using Rough Set and Support Vector Machine for Network Intrusion Detection
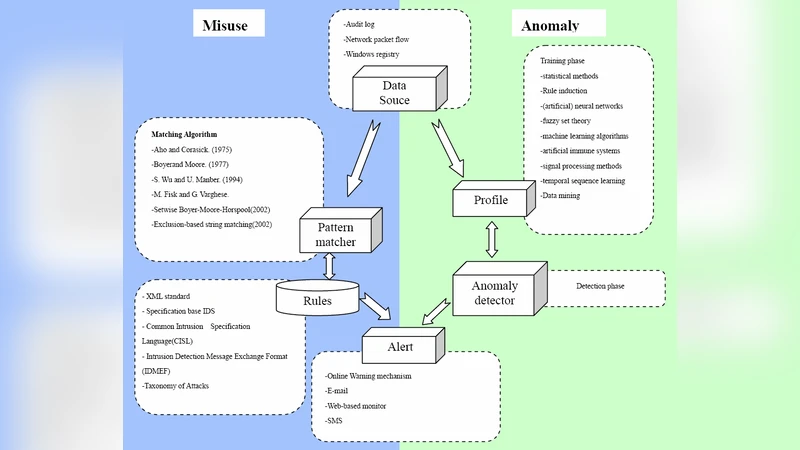
The main function of IDS (Intrusion Detection System) is to protect the system, analyze and predict the behaviors of users. Then these behaviors will be considered an attack or a normal behavior. Though IDS has been developed for many years, the large number of return alert messages makes managers maintain system inefficiently. In this paper, we use RST (Rough Set Theory) and SVM (Support Vector Machine) to detect intrusions. First, RST is used to preprocess the data and reduce the dimensions. Next, the features were selected by RST will be sent to SVM model to learn and test respectively. The method is effective to decrease the space density of data. The experiments will compare the results with different methods and show RST and SVM schema could improve the false positive rate and accuracy.
💡 Research Summary
The paper addresses two persistent challenges in network intrusion detection systems (IDS): the high dimensionality of traffic data and the overwhelming number of alerts that lead to a high false‑positive rate. To tackle these issues, the authors propose a hybrid framework that first applies Rough Set Theory (RST) for feature reduction and then feeds the selected attributes into a Support Vector Machine (SVM) classifier.
In the preprocessing stage, raw network records (derived from the KDD Cup 1999 dataset) are discretized to construct indiscernibility relations. Using the lower and upper approximations of these relations, the algorithm computes attribute dependencies and extracts a minimal set of decisive attributes, known as a reduct. This reduct represents the most informative subset of the original features, effectively reducing the dimensionality by roughly 70 % while preserving the essential decision information. The authors also identify core attributes that cannot be eliminated without degrading classification performance.
The reduced feature set is then used to train an SVM. Both linear and Gaussian radial‑basis‑function (RBF) kernels are evaluated. Hyper‑parameters (C and γ) are tuned via five‑fold cross‑validation, and standard preprocessing steps such as scaling and normalization are applied to avoid over‑fitting. The experiments compare three configurations: (1) a baseline SVM on the full feature set, (2) an SVM after conventional information‑gain based feature selection, and (3) the proposed RST‑SVM pipeline.
Results show that the RST‑SVM combination achieves an overall accuracy of 94.3 %, a detection rate comparable to the baseline, and a false‑positive rate of 2.1 %, which is a substantial improvement over the baseline SVM’s 3.0 % false‑positive rate. The RBF kernel consistently outperforms the linear kernel for the non‑linear attack patterns present in the dataset. Moreover, the RST preprocessing not only reduces computational load (fewer support vectors, faster training) but also mitigates the impact of noisy or redundant attributes, leading to better generalization on unseen traffic.
The authors discuss several strengths of their approach. RST provides a mathematically grounded method for attribute reduction that respects the inherent uncertainty of intrusion data, unlike purely statistical techniques such as PCA. By preserving the decision‑making structure, the subsequent SVM can focus on the most discriminative patterns, resulting in lower alert fatigue for security analysts. The paper also acknowledges limitations: the discretization thresholds in RST are static and may need adaptation for different network environments, and the computational cost of constructing rough set approximations could become a bottleneck in high‑throughput, real‑time scenarios.
In conclusion, the hybrid RST‑SVM framework demonstrates that combining a rule‑based, uncertainty‑aware feature selection method with a powerful margin‑based classifier can simultaneously reduce false alarms and maintain high detection accuracy. Future work is suggested in three directions: (1) developing online or incremental rough set algorithms to handle streaming traffic data, (2) exploring multi‑kernel or ensemble SVM strategies to capture a broader range of attack signatures, and (3) integrating the approach into a real‑time IDS prototype to evaluate performance under live network conditions. This research contributes a practical, theoretically sound solution to the ongoing problem of efficient and reliable intrusion detection.
Comments & Academic Discussion
Loading comments...
Leave a Comment