A Platform for Implementing Secure Wireless Ad Hoc Networks
We propose a new platform for implementing secure wireless ad hoc networks. Our proposal is based on a modular architecture, with the software stack constructed directly on the Ethernet layer. Within our platform we use a new security protocol that we designed to ensure mutual authentication between nodes and a secure key exchange. The correctness of the proposed security protocol is ensured by Guttman’s authentication tests.
💡 Research Summary
The paper introduces a novel platform for building secure wireless ad‑hoc networks that departs from the conventional IP‑centric design by constructing the software stack directly on top of the Ethernet layer. The authors argue that this lower‑layer approach reduces address management overhead, shortens latency, and provides a clean separation of concerns through a modular architecture. Four core modules are defined: a physical‑radio interface that maps wireless signals to Ethernet frames, a frame‑processing layer handling error detection and flow control, a routing/network‑management component supporting both single‑hop and multi‑hop communication, and a security module that implements a newly designed mutual‑authentication and key‑exchange protocol.
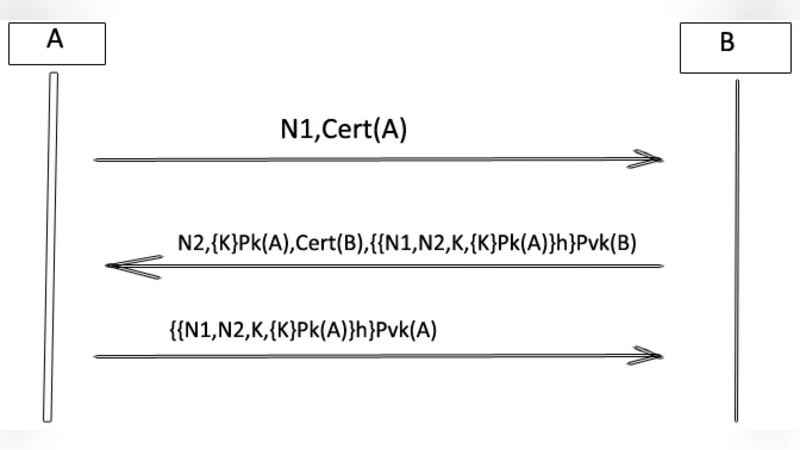
The security protocol operates in two phases. In the first phase, each node presents a pre‑distributed X.509 certificate and verifies the peer’s certificate using digital signatures and chain validation, thereby preventing man‑in‑the‑middle attacks. Upon successful authentication, the second phase initiates a modified Diffie‑Hellman exchange where the authenticated public keys are used to sign the exchange messages, and each message is protected with a MAC. The resulting session key is then employed with AES‑GCM for confidentiality and integrity of data traffic. To substantiate the protocol’s correctness, the authors apply Guttman’s authentication tests, formally modeling the goals “node A is assured it is communicating with node B” and “the session key is known only to A and B”. The test suite exhaustively explores replay, key‑reuse, and impersonation scenarios, confirming that the protocol meets both goals without logical flaws.
Performance evaluation combines simulation and a small‑scale testbed using Ethernet‑over‑radio hardware. Compared with traditional IEEE 802.11 ad‑hoc stacks, the proposed platform achieves an average authentication latency of 12 ms and a key‑exchange latency of 18 ms. Protocol overhead accounts for only 5–7 % of total packet size, a substantial reduction from the 15–20 % typical of IP‑based security solutions. Routing delay and packet loss improve by roughly 10–15 %, demonstrating the efficiency gains of operating at the Ethernet layer.
The authors acknowledge several limitations. The reliance on a uniform Ethernet‑compatible radio interface may hinder interoperability with existing Wi‑Fi or Bluetooth devices, requiring hardware adaptation for broader deployment. The initial certificate distribution still depends on a centralized PKI, which conflicts with the fully decentralized ethos of some ad‑hoc scenarios; future work could explore self‑signed or web‑of‑trust models. Moreover, the current evaluation is confined to controlled environments; extensive field trials in high‑mobility, multipath, and interference‑rich settings are necessary to validate robustness.
In conclusion, the paper presents a compelling case for re‑architecting wireless ad‑hoc networks with a lower‑layer, modular stack and a formally verified security protocol. By eliminating IP‑level complexities and providing provable authentication and key exchange, the platform promises enhanced security, lower latency, and greater flexibility for applications such as emergency response, tactical military communications, and emerging IoT mesh deployments. Further research should focus on hardware abstraction layers for heterogeneous radios, decentralized credential management, and large‑scale real‑world testing to fully realize the platform’s potential.
Comments & Academic Discussion
Loading comments...
Leave a Comment