As an immune inspired algorithm, the Dendritic Cell Algorithm (DCA) has been applied to a range of problems, particularly in the area of intrusion detection. Ideally, the intrusion detection should be performed in real-time, to continuously detect misuses as soon as they occur. Consequently, the analysis process performed by an intrusion detection system must operate in real-time or near-to real-time. The analysis process of the DCA is currently performed offline, therefore to improve the algorithm's performance we suggest the development of a real-time analysis component. The initial step of the development is to apply segmentation to the DCA. This involves segmenting the current output of the DCA into slices and performing the analysis in various ways. Two segmentation approaches are introduced and tested in this paper, namely antigen based segmentation (ABS) and time based segmentation (TBS). The results of the corresponding experiments suggest that applying segmentation produces different and significantly better results in some cases, when compared to the standard DCA without segmentation. Therefore, we conclude that the segmentation is applicable to the DCA for the purpose of real-time analysis.
Deep Dive into Integrating Real-Time Analysis With The Dendritic Cell Algorithm Through Segmentation.
As an immune inspired algorithm, the Dendritic Cell Algorithm (DCA) has been applied to a range of problems, particularly in the area of intrusion detection. Ideally, the intrusion detection should be performed in real-time, to continuously detect misuses as soon as they occur. Consequently, the analysis process performed by an intrusion detection system must operate in real-time or near-to real-time. The analysis process of the DCA is currently performed offline, therefore to improve the algorithm’s performance we suggest the development of a real-time analysis component. The initial step of the development is to apply segmentation to the DCA. This involves segmenting the current output of the DCA into slices and performing the analysis in various ways. Two segmentation approaches are introduced and tested in this paper, namely antigen based segmentation (ABS) and time based segmentation (TBS). The results of the corresponding experiments suggest that applying segmentation produces di
Integrating Real-Time Analysis With The Dendritic Cell
Algorithm Through Segmentation
Feng Gu, Julie Greensmith and Uwe Aickelin
School of Computer Science, University of Nottingham,
Nottingham, UK, NG8 1BB.
{fxg,jqg,uxa}@cs.nott.ac.uk
ABSTRACT
As an immune inspired algorithm, the Dendritic Cell Algo-
rithm (DCA) has been applied to a range of problems, par-
ticularly in the area of intrusion detection. Ideally, the intru-
sion detection should be performed in real-time, to contin-
uously detect misuses as soon as they occur. Consequently,
the analysis process performed by an intrusion detection sys-
tem must operate in real-time or near-to real-time. The
analysis process of the DCA is currently performed offline,
therefore to improve the algorithm’s performance we suggest
the development of a real-time analysis component. The ini-
tial step of the development is to apply segmentation to the
DCA. This involves segmenting the current output of the
DCA into slices and performing the analysis in various ways.
Two segmentation approaches are introduced and tested in
this paper, namely antigen based segmentation (ABS) and
time based segmentation (TBS). The results of the corre-
sponding experiments suggest that applying segmentation
produces different and significantly better results in some
cases, when compared to the standard DCA without seg-
mentation. Therefore, we conclude that the segmentation is
applicable to the DCA for the purpose of real-time analysis.
Categories and Subject Descriptors
I.2 [Artificial Intelligence]: Miscellaneous
General Terms
Algorithms, Experimentation, Performance
Keywords
Dendritic Cell Algorithm, Intrusion Detection Systems, Real-
Time Analysis, Segmentation
- INTRODUCTION
Artificial Immune Systems (AIS) [4] are computer sys-
tems inspired by both theoretical immunology and observed
Permission to make digital or hard copies of all or part of this work for
personal or classroom use is granted without fee provided that copies are
not made or distributed for profit or commercial advantage and that copies
bear this notice and the full citation on the first page. To copy otherwise, to
republish, to post on servers or to redistribute to lists, requires prior specific
permission and/or a fee.
GECCO’09, July 8–12, 2009, Montréal Québec, Canada.
Copyright 2009 ACM 978-1-60558-325-9/09/07 …$5.00.
immune functions, principles and models, which can be ap-
plied to real world problems. As the natural immune system
is designed to protect the body from a wealth of invading
micro-organisms, artificial immune systems are developed
to provide the same defensive properties within a comput-
ing context. Initially AIS based themselves upon simple
models of the human immune system. As noted by Stibor
et al. [16], ‘first generation algorithms’ including negative
and clonal selection do not produce the same high perfor-
mance as the human immune system. These algorithms,
negative selection in particular, are prone to problems with
scaling and the generation of excessive false alarms when
used to detect intruders in computer networks. Recently
developed AIS use more rigourous and up-to-date immunol-
ogy and are developed in collaboration with immunologists.
The resulting algorithms are believed to encapsulate the de-
sirable properties of immune systems including robustness
and error tolerance.
One of such ‘second generation’ AIS is the Dendritic Cell
Algorithm (DCA) [7]. This algorithm is inspired by the
function of the dendritic cells of the innate immune sys-
tem and incorporates the principles of a key novel theory
in immunology, termed the danger theory [13]. This theory
suggests that dendritic cells (DCs) are responsible for the
initial detection of invading micro-organisms. An abstract
model of natural DC behaviour is used as the foundation
of the developed algorithm. Currently, the DCA has been
successfully applied to numerous problem domains, includ-
ing port scan detection [7], Botnet detection [1] and as a
classifier for robotic security [14]. These applications have
suggested that
the DCA shows
not only good
performance on detection rate, but also the ability to
reduce the rate of false alarms in comparison to other
systems including Self Organising Maps [10]. The majority
of applications to which the DCA is applied involve the
detection of unauthorised use and abuse of computer
systems and networks - a prob- lem termed intrusion
detection. Systems designed to detect intrusions are
termed intrusion detection systems. The de- velopment of
reliable and sophisticated intrusion detection systems is
non trivial, as such systems need to pro
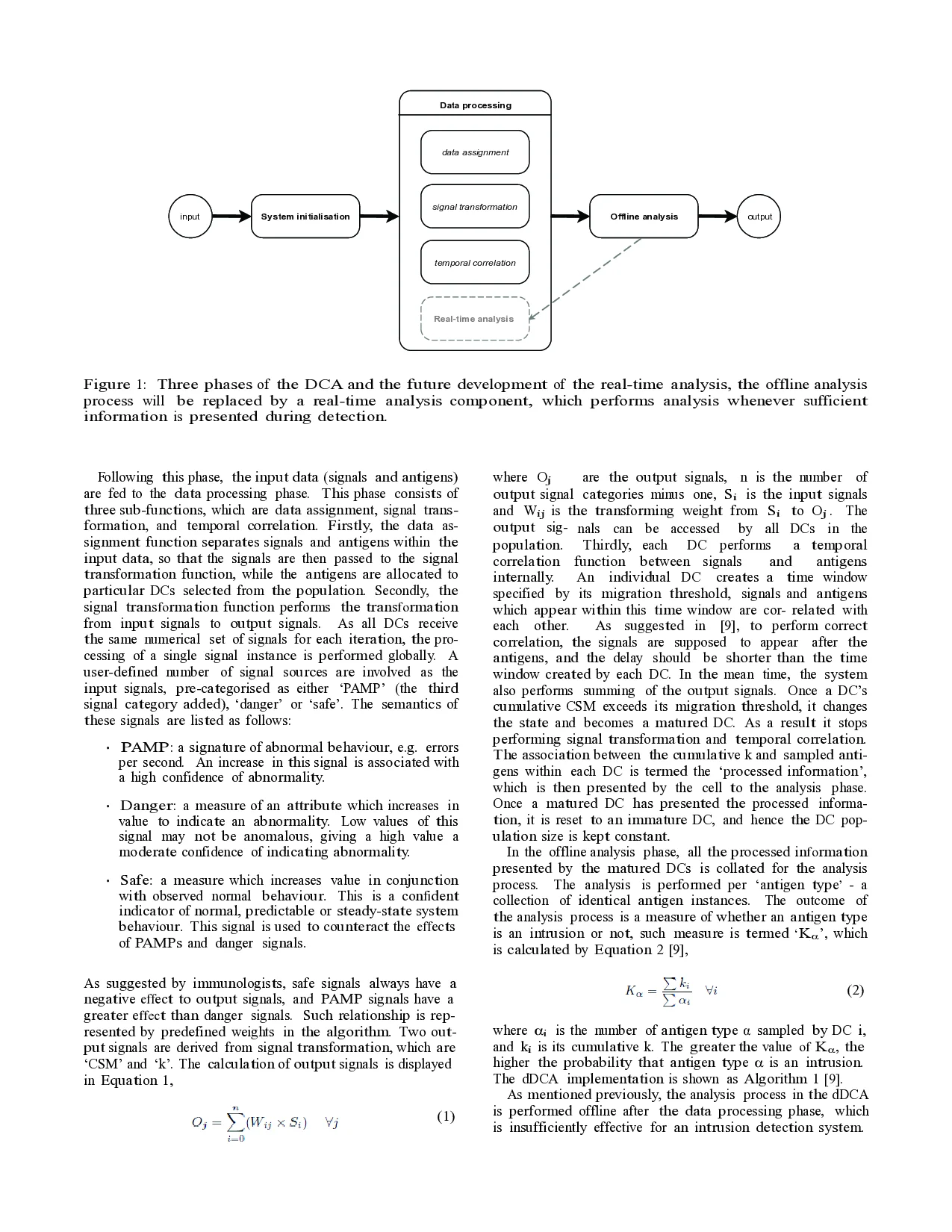
…(Full text truncated)…
This content is AI-processed based on ArXiv data.