Immune System Approaches to Intrusion Detection - A Review
The use of artificial immune systems in intrusion detection is an appealing concept for two reasons. Firstly, the human immune system provides the human body with a high level of protection from invading pathogens, in a robust, self-organised and distributed manner. Secondly, current techniques used in computer security are not able to cope with the dynamic and increasingly complex nature of computer systems and their security. It is hoped that biologically inspired approaches in this area, including the use of immune-based systems will be able to meet this challenge. Here we review the algorithms used, the development of the systems and the outcome of their implementation. We provide an introduction and analysis of the key developments within this field, in addition to making suggestions for future research.
💡 Research Summary
The paper provides a comprehensive review of the use of artificial immune systems (AIS) for intrusion detection, positioning the field at the intersection of immunology and computer security. It begins by outlining the limitations of traditional intrusion detection systems (IDS), namely high false‑positive rates for anomaly‑based detectors, low detection of novel attacks for misuse‑based detectors, and challenges in scalability, configurability, and adaptability in large, dynamic networks. The authors draw a parallel between the human immune system (HIS) and IDS: innate immunity corresponds to misuse detection (signature‑based, low false positives) while adaptive immunity mirrors anomaly detection (learning new patterns, higher false positives).
The review categorises AIS research into three principal philosophies, each rooted in a different immunological concept. The first philosophy adapts conventional algorithms (e.g., IBM’s early virus detector) by mapping HIS stages onto existing computational techniques. The second, and historically dominant, philosophy employs the negative‑selection paradigm introduced by Forrest, which mimics thymic education of T‑cells to generate detectors that do not match “self” data. The third philosophy leverages the Danger Theory, triggering responses only when a damage signal is observed, thereby aiming to reduce spurious alerts. The authors also note newer hybrid approaches such as AINET and immunocomputing that blend multiple immunological ideas.
A central contribution of the paper is the systematic mapping of twelve immune‑derived properties (distributed, self‑organising, lightweight, multi‑layered, diverse, disposable, etc.) to seven widely recognised IDS requirements: robustness, configurability, extensibility, scalability, adaptability, global analysis, and efficiency. Distributed and self‑organising architectures provide robustness and scalability; lightweight designs ensure low overhead; multi‑layered and diverse detectors increase fault tolerance; disposable components simplify updates and extensions.
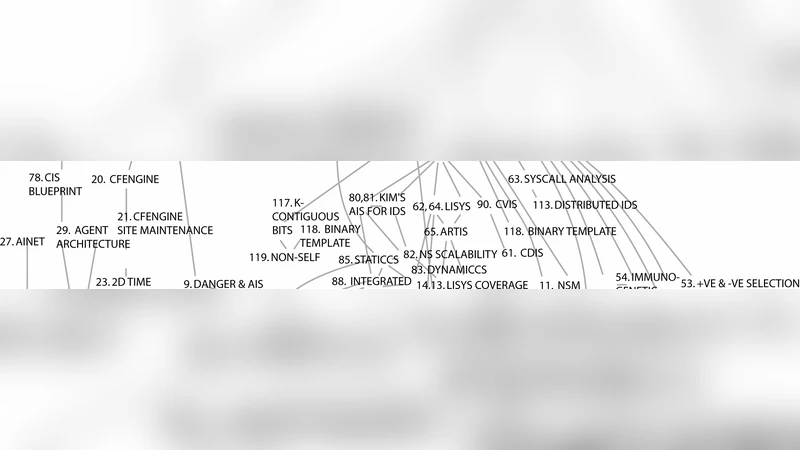
The authors then survey a broad set of AIS‑based IDS implementations, tracing their evolution through a phylogenetic tree. Early work (Kephart et al., IBM) demonstrated a five‑stage model inspired by HIS processes. Subsequent negative‑selection systems refined detector generation, but struggled with the definition of “self” in ever‑changing environments, leading to high false‑positive rates when self‑profiles drift. Danger‑theory systems showed promise in reducing false alerts but required precise definition of damage signals, a non‑trivial engineering problem. Hybrid systems attempt to combine the strengths of statistical learning, machine learning, and immunological mechanisms, yet many remain confined to simulated or small‑scale testbeds.
The paper identifies several critical gaps. First, most evaluations are performed on limited datasets or controlled lab environments, lacking validation on real‑world, high‑throughput networks. Second, the mathematical modelling of immune processes introduces numerous parameters that are difficult to tune and may not generalise across domains. Third, the dynamic nature of “self” in modern networks necessitates continual re‑learning, which can be computationally expensive and may disrupt detection continuity.
To address these challenges, the authors propose a research agenda: (1) develop hybrid frameworks that integrate AIS with modern machine‑learning techniques (deep learning, reinforcement learning) to improve detector generation and adaptation; (2) design online, incremental learning mechanisms that update self‑profiles with minimal overhead; (3) establish standardized benchmark suites and performance metrics for AIS‑IDS to enable fair comparison; (4) explore cloud‑native and edge‑computing architectures that naturally support distributed, lightweight, and disposable immune components; and (5) enhance memory mechanisms inspired by immunological memory to retain knowledge of previously observed attacks for rapid recall.
In conclusion, the review demonstrates that AIS offers a rich set of biologically inspired principles capable of addressing many of the shortcomings of conventional IDS. While existing systems have successfully embodied individual immune properties, a fully integrated, scalable, and adaptive AIS‑IDS remains an open challenge. The paper serves as a roadmap for future work, encouraging interdisciplinary collaboration between immunologists, security researchers, and systems engineers to realise the promise of immune‑inspired intrusion detection.
Comments & Academic Discussion
Loading comments...
Leave a Comment