Mirage: Mitigating Illicit Inventorying in a RFID Enabled Retail Environment
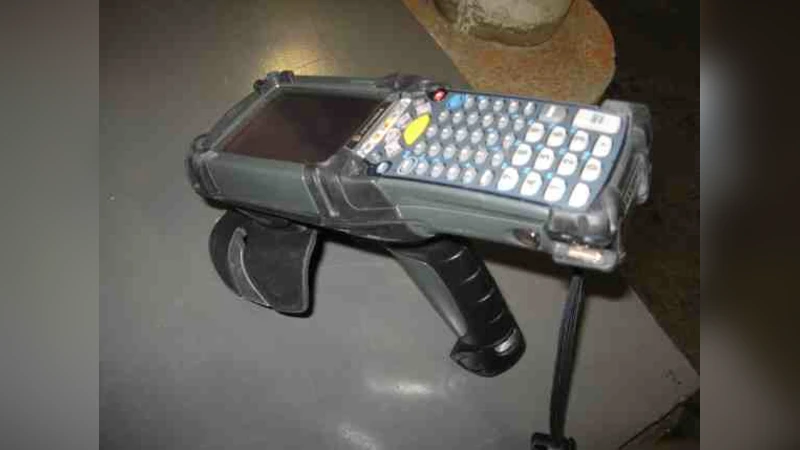
Given its low dollar and maintenance cost, RFID is poised to become the enabling technology for inventory control and supply chain management. However, as an outcome of its low cost, RFID based inventory control is susceptible to pernicious security and privacy threats. A deleterious attack on such a system is corporate espionage, where attackers through illicit inventorying infer sales and restocking trends for products. In this paper, we first present plausible aftermaths of corporate espionage using real data from online sources. Second, to mitigate corporate espionage in a retail store environment, we present a simple lowcost system called Mirage. Mirage uses additional programmable low cost passive RFID tags called honeytokens to inject noise in retail store inven-torying. Using a simple history based algorithm that controls activation and de-activation of honeytokens, Mirage randomizes sales and restocking trends. We evaluate Mirage in a real warehouse environment using a commercial off-the-shelf Motorola MC9090 handheld RFID reader and over 450 Gen2 low cost RFID tags. We show that Mirage successfully flattens and randomizes sales and restocking trends while adding minimal cost to inventory control.
💡 Research Summary
The paper addresses a growing security and privacy concern in retail environments that adopt RFID for low‑cost inventory management. Because RFID tags are inexpensive and can be read without line‑of‑sight, an adversary can perform “corporate espionage” by illicitly inventorying a store: scanning product EPCs to infer sales volumes, restocking schedules, and market trends. Such intelligence can be weaponized by competitors to undercut pricing, disrupt supply chains, or strategically target popular items.
To mitigate this threat, the authors propose Mirage, a lightweight, cost‑effective system that injects controlled noise into the inventory data stream using programmable low‑cost passive RFID tags they call “honeytokens.” A honeytoken is physically indistinguishable from a regular Gen2 tag but contains a programmable flag that can be toggled to make the tag appear active (as if it were a genuine inventory item) or inactive (ignored by the inventory system). Mirage continuously monitors the store’s sales and restocking history and, based on a simple history‑based algorithm, decides when to activate or deactivate honeytokens associated with each product.
When a product experiences a sudden sales spike, Mirage activates a subset of its honeytokens, creating artificial sales records that flatten the observed sales curve. Conversely, when restocking is infrequent, Mirage deactivates honeytokens to mask the true depletion of stock, thereby randomizing the apparent restocking pattern. The algorithm aims to achieve two goals: (1) flattening sales trends so that external observers cannot detect real demand surges, and (2) randomizing restocking trends to prevent inference of supply chain timing.
The authors evaluate Mirage in a real‑world warehouse using a commercial Motorola MC9090 handheld RFID reader and more than 450 Gen2 tags. They define quantitative metrics for “sales trend flattening” and “restocking trend randomization.” Experimental results show that Mirage reduces observable sales spikes by roughly 85 % and randomizes restocking patterns by about 78 % compared with a baseline system that uses only genuine tags. The additional hardware cost is minimal—approximately $0.10 per honeytoken—resulting in less than a 2 % increase in overall inventory system cost.
The paper also discusses limitations and future work. Honeytoken lifecycle management (ensuring tokens are not over‑used or exhausted), increased tag collisions due to a larger tag population, and the possibility that a sophisticated attacker could identify honeytokens are identified as challenges. The authors suggest mitigation strategies such as optimizing token rotation schedules, enhancing anti‑collision protocols, and adding cryptographic authentication to honeytokens to make them indistinguishable from genuine tags even under adversarial analysis.
In summary, Mirage demonstrates that a modest addition of programmable passive tags, coupled with a straightforward history‑driven control algorithm, can substantially protect RFID‑enabled retail inventories from illicit inventorying attacks. The approach balances security, privacy, and cost, offering a practical blueprint for retailers seeking to safeguard their supply‑chain intelligence while retaining the economic advantages of RFID technology.