Advanced Trace Pattern For Computer Intrusion Discovery
The number of crime committed based on the malware intrusion is never ending as the number of malware variants is growing tremendously and the usage of internet is expanding globally. Malicious codes easily obtained and use as one of weapon to gain their objective illegally. Hence, in this research, diverse logs from different OSI layer are explored to identify the traces left on the attacker and victim logs in order to establish worm trace pattern to defending against the attack and help revealing true attacker or victim. For the purpose of this paper, it focused on malware intrusion and traditional worm namely sasser worm variants. The concept of trace pattern is created by fusing the attacker’s and victim’s perspective. Therefore, the objective of this paper is to propose a general worm trace pattern for attacker’s, victim’s and multi-step (attacker/victim)’s by combining both perspectives. These three proposed worm trace patterns can be extended into research areas in alert correlation and computer forensic investigation.
💡 Research Summary
The paper addresses the growing challenge of malware‑driven intrusions, focusing specifically on the Sasser worm and its variants. Recognizing that most existing detection and forensic approaches concentrate solely on the attacker’s perspective, the authors propose a comprehensive “trace pattern” methodology that fuses attacker, victim, and multi‑step (attacker/victim) viewpoints.
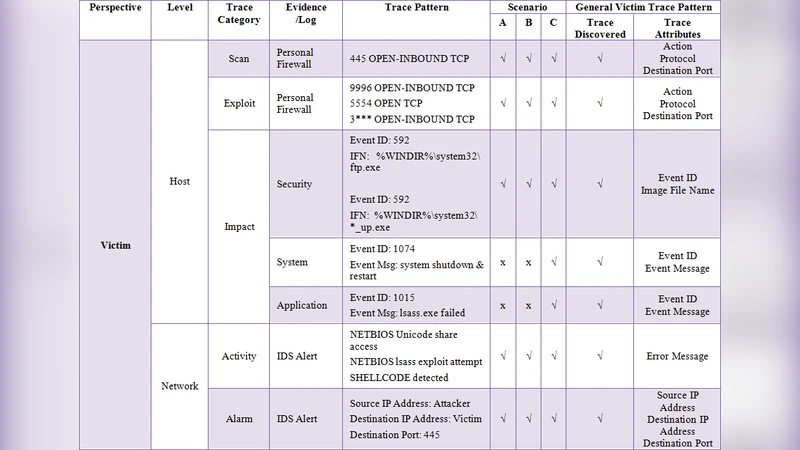
To build these patterns, the researchers set up a controlled laboratory environment and executed three distinct intrusion scenarios (labeled A, B, and C). In each scenario, a designated “attacker” host (named Selamat) initiates a Sasser infection against one or more victim hosts. The infection process follows the well‑documented Sasser behavior: scanning for the LSASS vulnerability on TCP port 445, exploiting it to open a remote shell on TCP port 9996, and delivering the worm payload via a custom FTP server on TCP port 5554 or a non‑standard port (represented as 3***). Once a host is compromised, it becomes a secondary attacker, launching further infections—this creates a multi‑step chain that the authors explicitly model.
During the experiments, logs were collected from multiple OSI layers: personal firewall logs, Windows security logs, system logs, application logs, IDS alert logs, as well as raw packet captures (tcpdump and Wireshark). The analysis identified a set of recurring artefacts across all three scenarios:
- Network‑level artefacts – Repeated connection attempts to ports 445, 9996, 5554, and the variant‑specific high‑numbered port. These appear in firewall logs and packet captures as inbound SYNs from the attacker and outbound responses from the victim.
- Host‑level artefacts – Security log – Event ID 592 (new process creation) indicating the launch of the FTP server or the worm executable, and Event ID 1074 (system shutdown/reboot) triggered after LSASS crashes.
- Application log – Event ID 1015 reporting an LSASS.exe failure, which is the hallmark of Sasser‑induced system instability.
- System log – Entries confirming that the system has been forced to restart, often accompanied by a “shutdown timer” message.
- IDS alerts – Signatures detecting abnormal FTP traffic, port‑scanning activity, and the specific payload exchange patterns used by Sasser.
By correlating these artefacts, the authors define three generic trace patterns:
- Attacker‑Centric Pattern – Emphasizes the initial scanning (port 445), exploitation (port 9996), and payload delivery (port 5554/3***). It includes the creation of a temporary FTP service and the spawning of multiple attack threads.
- Victim‑Centric Pattern – Highlights the victim’s exposure of vulnerable ports, the appearance of LSASS‑related error events, the forced system reboot, and the presence of the worm executable in the Windows directory (e.g., C:\WIN.LOG, C:\WIN2.LOG).
- Multi‑Step (Attacker/Victim) Pattern – Captures the transition where a compromised host becomes a new attacker, repeating the attacker‑centric artefacts against fresh targets. This pattern is crucial for detecting worm propagation chains in real time.
The paper argues that integrating victim‑side evidence with attacker‑side signatures yields a more robust detection framework and aids forensic investigators in attributing the true source of an intrusion. The multi‑step pattern, in particular, provides a systematic way to visualize and interrupt cascading infections.
Limitations are acknowledged: the experiments are confined to a lab network and to Sasser variants only; therefore, the applicability to newer worms, polymorphic malware, or cloud‑based infrastructures remains untested. Moreover, the reliance on comprehensive log collection assumes that logs are intact and unaltered, which may not hold in sophisticated attacks.
Future work suggested includes extending the methodology to other malware families (e.g., ransomware, trojans), evaluating the patterns against real‑world enterprise log streams, and exploring automated correlation engines that can ingest the defined artefacts and raise alerts in Security Operations Centers.
In summary, the study contributes a novel, three‑fold trace‑pattern framework that bridges attacker and victim perspectives, offering a practical tool for intrusion detection, incident response, and digital forensic analysis of worm‑based attacks.
Comments & Academic Discussion
Loading comments...
Leave a Comment