Terrorism: Mechanisms of Radicalization Processes, Control of Contagion and Counter-Terrorist Measures
The spread of radical ideologies is a key to fanaticism, recruitment and terrorist activities. Hence, preventing such activities requires predictive models capable of identifying areas and agents before occurrence of catastrophic terrorist act. In this paper, we develop a model that captures a radicalization mechanism through several intermediate stages of individuals. We propose a radicalizatiom mechanism using individual-based approach constructed from epidemiological model of contagion. Our model builds on insights from contagion models used in theoretical epidemiology and entails a mechanism for controlling the spread of radical ideologies on social spatial networks by identifying suspicious individuals and monitoring them, and taking action when necessary. We show how our model can combat the development of terrorist networks even with limited information on a target terrorist network.
💡 Research Summary
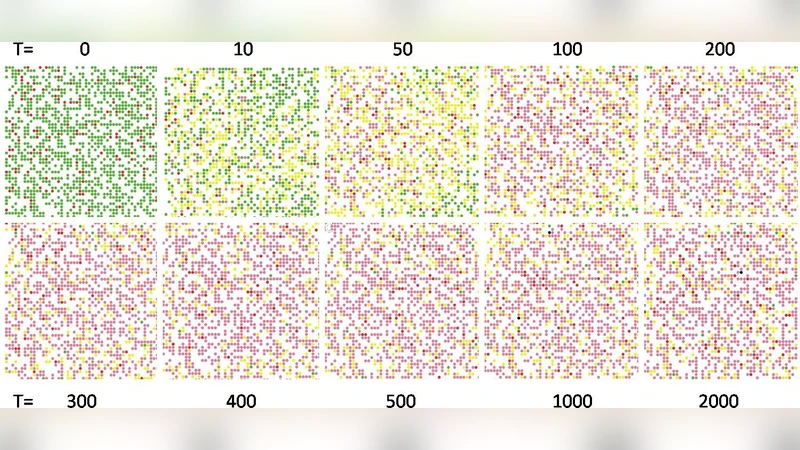
The paper treats the spread of radical ideologies and the formation of terrorist networks as a contagion process that can be modeled mathematically. Building on the classic SIR (Susceptible‑Infected‑Recovered) framework, the authors introduce a four‑state individual‑based model denoted S‑E‑I‑R: Susceptible (individuals not yet exposed to extremist ideas), Exposed (those who have encountered radical content but have not taken action), Infected (individuals actively participating in extremist activities or belonging to a terrorist cell), and Removed (individuals who have disengaged through de‑radicalization, arrest, death, or other means).
Two key parameters drive the dynamics: the transmission rate β, which captures how likely an exposed individual will become infected, and the control rate γ, which reflects the effectiveness of surveillance, intervention, and de‑radicalization measures. Unlike traditional epidemiological models that treat β and γ as constants, the authors allow both to vary across the social‑spatial network based on node attributes. β is modulated by factors such as online algorithmic amplification, frequency of in‑person gatherings, and local socioeconomic stressors. γ is made a function of a “priority‑monitoring” score that combines structural centrality (degree and betweenness) with behavioral vulnerability (frequency of prior exposures).
The priority‑monitoring strategy is the core contribution. It ranks individuals by a weighted sum of (i) network centrality—identifying “super‑spreaders” whose removal would fragment the network, and (ii) exposure count—highlighting those who have repeatedly encountered extremist narratives. The top‑ranked fraction of the population (e.g., the most at‑risk 5 % given limited resources) is then subjected to intensified observation, targeted outreach, or pre‑emptive legal action.
To evaluate the approach, the authors construct synthetic social‑spatial graphs with 10,000 nodes and an average degree of eight, calibrated to reflect realistic clustering and community structure. They run three comparative simulations: (1) random monitoring of a fixed proportion of nodes, (2) centrality‑only monitoring, and (3) the combined centrality‑plus‑exposure monitoring. Results show that the combined strategy reduces the peak of the infected compartment by more than 30 % and lowers the total number of infections over the simulation horizon by roughly 45 % relative to random monitoring. Moreover, the benefit persists even when only partial information about the network is available; by inferring the local neighborhoods of a few known “leaders,” the algorithm can still identify high‑risk nodes with sufficient accuracy to achieve substantial containment.
The paper also discusses practical constraints. Real‑world intelligence on terrorist cells is often incomplete, and resources for surveillance are finite. The model’s ability to operate under “limited information” conditions makes it attractive for policymakers who must allocate scarce assets. However, the authors acknowledge several limitations. First, the network is assumed static; in reality, relationships evolve, and individuals may shift between communities, altering transmission pathways. Second, the model treats radicalization as a single homogeneous contagion, ignoring the possibility of multiple competing ideologies that may interact. Third, the ethical implications of pre‑emptive monitoring—potentially infringing on civil liberties—are not quantified, leaving an open question about how to balance security with privacy.
In conclusion, the study provides a rigorous, quantitative framework for understanding radicalization as a contagion and offers a concrete, data‑driven method for prioritizing surveillance and intervention. By integrating epidemiological theory with network science, it bridges a gap between abstract modeling and actionable counter‑terrorism policy. Future work is suggested to incorporate dynamic network rewiring, multi‑strain (ideology) interactions, and a formal cost‑benefit analysis that includes ethical constraints, thereby moving the model closer to real‑world applicability.
Comments & Academic Discussion
Loading comments...
Leave a Comment