A Novel Method for Intrusion Detection System to Enhance Security in Ad hoc Network
The notion of an ad hoc network is a new paradigm that allows mobile hosts (nodes) to communicate without relying on a predefined infrastructure to keep the network connected. Most nodes are assumed to be mobile and communication is assumed to be wireless. The mobility of nodes in an ad-hoc network means that both the population and the topology of the network are highly dynamic. It is very difficult to design a once-for-all intrusion detection system. A secure protocol should atleast include mechanisms against known attack types. In addition, it should provide a scheme to easily add new security features in the future. The paper includes the detailed description of Proposed Intrusion Detection System based on Local Reputation Scheme. The proposed System also includes concept of Redemption and Fading these are mechanism that allow nodes previously considered malicious to become a part of the network again. The simulation of the proposed system is to be done using NS-2 simulator.
💡 Research Summary
The paper addresses the challenge of securing mobile ad‑hoc networks (MANETs), where nodes act both as hosts and routers and the network topology changes constantly. Traditional intrusion detection systems (IDS) designed for wired infrastructures are ill‑suited for MANETs because there is no central infrastructure, and the wireless medium is open to both legitimate and malicious users. After reviewing existing IDS classifications (host‑based vs. network‑based, anomaly vs. misuse vs. specification) and summarizing prior MANET‑specific approaches such as Watchdog/Path‑Rater, CONFIDANT, CORE, and OCEAN, the authors propose a new IDS built around a Local Reputation System.
Key characteristics of the proposed system:
-
Local Reputation Only – Each node stores reputation values for its one‑hop neighbors only, avoiding the overhead of disseminating global reputation information. Reputation values R lie between Rmin and Rmax, with two thresholds Ru (untrust) and Rt (trust). Based on where R falls, a node’s trust level T is set to 1 (trustworthy), 0 (undecided) or –1 (untrustworthy). New or recently moved nodes start with a neutral reputation between Ru and Rt.
-
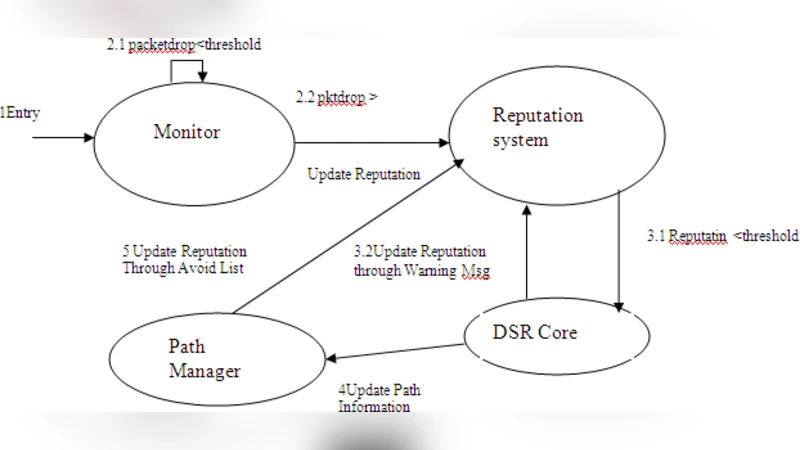
Monitoring Module – Leveraging the Passive ACK (PACK) feature of the DSR protocol, a node registers every data packet it forwards. In promiscuous mode it listens for PACKs from the next hop and matches them against its register. At the end of a fixed “Timing Window” (e.g., one second) the node logs the number of packets that did not generate a PACK and forwards this log to the Reputation Manager.
-
Reputation Manager – Reputation updates come from three sources, each with an associated weight: (a) direct self‑observation (highest weight), (b) warning messages received from neighbors, and (c) an “avoid list” that is attached to DSR RREQ/RREP packets. After each timing window the manager adjusts the reputation of each neighbor. Nodes are classified as Normal, Suspicious, or Malicious based on their current reputation.
-
Path Manager – Integrated with DSR’s route discovery, the Path Manager appends an “avoid list” (list of malicious nodes) to every RREQ header. If a node finds its own identifier in the list, it drops the request. When a route reply is generated, paths that contain malicious or suspicious nodes are deprioritized or discarded. If a node becomes malicious during an active session, all routes containing it are removed from the route cache and a route error (RERR) is generated.
-
Trace Test – When a neighbor’s reputation falls into the suspicious range, the node initiates a trace test. It creates a fake data packet with TTL = 2, routes it through the suspect node, and waits for a PACK. Successful PACK receipt restores the node’s reputation to a default level; failure leads to an immediate malicious classification and the broadcast of a warning message.
-
Redemption and Fading – To avoid permanently ostracizing nodes that may have been falsely labeled malicious (e.g., due to transient link failures or congestion), the system introduces a fading mechanism. If a node remains inactive (no appearance in warning messages or avoid lists) for a predefined period, its reputation is gradually increased by a fading rate, moving it from the malicious list to the middle of the suspicious category. The node does not regain full neutral status automatically, ensuring that any subsequent misbehavior will quickly re‑classify it as malicious.
The authors outline the algorithms for route discovery, monitoring, warning propagation, and trace testing in pseudo‑code. They claim that the local reputation approach reduces communication overhead, while the combination of timing windows, trace tests, and fading provides robustness against both malicious behavior and occasional false positives.
The paper mentions that the proposed system will be evaluated using the NS‑2 network simulator, but it does not provide concrete simulation parameters (number of nodes, mobility model, traffic patterns), attack scenarios, or performance metrics such as detection rate, false‑positive rate, packet delivery ratio, or overhead. Consequently, the effectiveness of the design remains unverified within the manuscript.
Critical assessment:
- Novelty: The focus on strictly local reputation distinguishes the work from prior global‑reputation schemes, potentially lowering overhead.
- Strengths: Clear modular design (Monitor, Reputation Manager, Path Manager), integration with existing DSR mechanisms, and the inclusion of redemption/fading to mitigate permanent exclusion.
- Weaknesses: Lack of quantitative evaluation, insufficient discussion of how timing‑window size and reputation thresholds affect detection accuracy, and limited analysis of how non‑malicious packet loss (e.g., due to channel errors) could trigger false accusations. The trace test, while useful, adds extra traffic and may be exploited by attackers to generate denial‑of‑service conditions.
- Future work: The authors should conduct extensive NS‑2 experiments covering diverse mobility patterns, varying node densities, and multiple attack types (e.g., blackhole, grayhole, wormhole). Sensitivity analysis on window size, thresholds, and fading rates would clarify trade‑offs between detection speed and false‑positive rate. Comparison with existing reputation‑based IDS (CONFIDANT, CORE, OCEAN) would also help position the contribution.
In summary, the paper proposes a coherent, locally‑focused reputation‑based IDS for MANETs, enriched with mechanisms for testing suspect nodes and rehabilitating previously malicious nodes. While conceptually sound, the lack of empirical validation limits confidence in its practical applicability. Further simulation and possibly real‑world test‑bed experiments are required to substantiate the claimed benefits.
Comments & Academic Discussion
Loading comments...
Leave a Comment