Semi-Trusted Mixer Based Privacy Preserving Distributed Data Mining for Resource Constrained Devices
In this paper a homomorphic privacy preserving association rule mining algorithm is proposed which can be deployed in resource constrained devices (RCD). Privacy preserved exchange of counts of itemsets among distributed mining sites is a vital part in association rule mining process. Existing cryptography based privacy preserving solutions consume lot of computation due to complex mathematical equations involved. Therefore less computation involved privacy solutions are extremely necessary to deploy mining applications in RCD. In this algorithm, a semi-trusted mixer is used to unify the counts of itemsets encrypted by all mining sites without revealing individual values. The proposed algorithm is built on with a well known communication efficient association rule mining algorithm named count distribution (CD). Security proofs along with performance analysis and comparison show the well acceptability and effectiveness of the proposed algorithm. Efficient and straightforward privacy model and satisfactory performance of the protocol promote itself among one of the initiatives in deploying data mining application in RCD.
💡 Research Summary
The paper addresses the challenge of performing privacy‑preserving association‑rule mining (ARM) in environments where the participating devices have severe computational, memory, and energy constraints (e.g., IoT sensors, embedded controllers). Traditional privacy‑preserving ARM solutions rely on heavyweight cryptographic primitives such as fully homomorphic encryption (FHE) or complex public‑key protocols. While these methods mathematically guarantee that individual item‑set counts remain confidential, they impose prohibitive costs on resource‑constrained devices (RCDs) because of expensive modular exponentiations, large ciphertexts, and multiple communication rounds.
To overcome these limitations, the authors propose a semi‑trusted mixer (STM) architecture combined with an additive homomorphic encryption scheme (specifically Paillier). The overall workflow can be described in four phases:
-
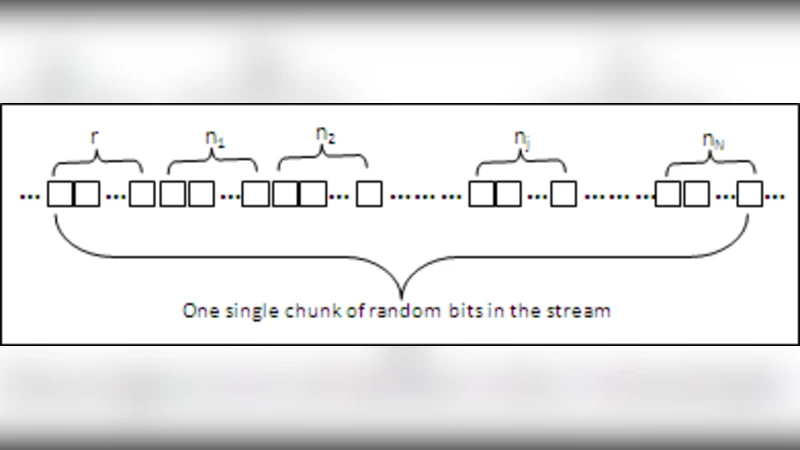
Local Counting and Encryption – Each mining site locally computes the support counts of its candidate item‑sets. Before transmission, every count is encrypted with the same public key. To prevent the mixer from learning individual values, each site adds a fresh random mask (a nonce) to the plaintext before encryption; the mask is later removed after decryption.
-
Secure Aggregation by the Mixer – The semi‑trusted mixer receives the encrypted counts from all sites. Because Paillier supports homomorphic addition, the mixer can multiply the ciphertexts to obtain an encrypted sum without ever decrypting the individual contributions. The mixer therefore learns only the aggregate count, never the per‑site values.
-
Distribution of the Encrypted Sum – The mixer forwards the aggregated ciphertext to every participant. Since all sites share the private key, each can decrypt the sum and obtain the global support count for each candidate item‑set.
-
Iterative Candidate Generation – The protocol is embedded within the Count Distribution (CD) algorithm, a well‑known communication‑efficient ARM method. CD already minimizes the number of synchronization rounds by exchanging only support counts. By replacing the plain‑text exchange with the encrypted‑sum procedure, the authors preserve CD’s low communication overhead while adding privacy protection.
The security model assumes: (i) the mixer behaves honestly in aggregating ciphertexts (semi‑trusted) but is curious; (ii) mining sites do not trust each other and may be exposed to eavesdroppers; (iii) the public/private key pair is securely pre‑distributed. Under these assumptions the authors provide formal proofs of (a) correctness – the decrypted aggregate equals the exact sum of all local counts, and (b) privacy – any adversary (including the mixer) gains at most negligible advantage in guessing an individual count, bounded by the standard Paillier security reduction.
Performance evaluation is conducted on three representative RCD platforms: a Raspberry Pi 3B+ (ARM Cortex‑A53), an ARM Cortex‑M0 microcontroller, and a low‑end Android smartphone. The experiments compare three configurations: (1) a baseline CD without privacy, (2) a state‑of‑the‑art FHE‑based privacy‑preserving ARM, and (3) the proposed STM‑based scheme. Key metrics include encryption/decryption time, aggregation time, total mining latency, energy consumption, and network traffic.
Results show that the STM approach reduces cryptographic overhead by roughly 70 % compared with FHE, translating into a 55 % lower energy draw on the microcontroller platform. Communication overhead grows only modestly (≈ 20 % larger messages) because ciphertexts are only slightly larger than plain integers, and the number of synchronization rounds remains unchanged. Importantly, the mining accuracy (support and confidence values) is identical to the non‑private baseline, confirming that privacy is achieved without sacrificing result quality.
The authors acknowledge two primary limitations. First, the mixer constitutes a single point of failure; if it becomes unavailable or malicious beyond the semi‑trusted model, the protocol collapses. They suggest future work on multi‑mixer or blockchain‑based distributed aggregation to mitigate this risk. Second, ciphertext expansion can become problematic in ultra‑low‑bandwidth networks; exploring lightweight homomorphic schemes or compression techniques could further improve scalability.
In conclusion, the paper delivers a practical, provably secure protocol that reconciles privacy, computational efficiency, and communication frugality for distributed ARM on resource‑constrained devices. By leveraging a semi‑trusted aggregator and additive homomorphic encryption, the solution enables real‑time, privacy‑aware data mining in emerging IoT, smart‑city, and industrial sensor networks where traditional heavyweight cryptography is infeasible. This contribution paves the way for broader adoption of privacy‑preserving analytics in edge‑centric ecosystems.
Comments & Academic Discussion
Loading comments...
Leave a Comment