Self-Organized Authentication in Mobile Ad-hoc Networks
This work proposes a new distributed and self-organized authentication scheme for Mobile Ad-hoc NETworks (MANETs). Apart from describing all its components, special emphasis is placed on proving that the proposal fulfils most requirements derived from the special characteristics of MANETs, including limited physical protection of broadcast medium, frequent route changes caused by mobility, and lack of structured hierarchy. Interesting conclusions are obtained from an analysis of simulation experiments in different scenarios.
💡 Research Summary
The paper addresses the fundamental challenge of establishing trustworthy authentication in Mobile Ad‑hoc Networks (MANETs), where there is no fixed infrastructure, nodes are highly mobile, and the wireless medium is exposed to eavesdropping and tampering. Traditional Public‑Key‑Infrastructure (PKI) solutions rely on centralized certificate authorities and static trust anchors, which are infeasible in such environments. To overcome these limitations, the authors propose a fully distributed, self‑organized authentication framework that operates without any external authority and adapts dynamically to topology changes.
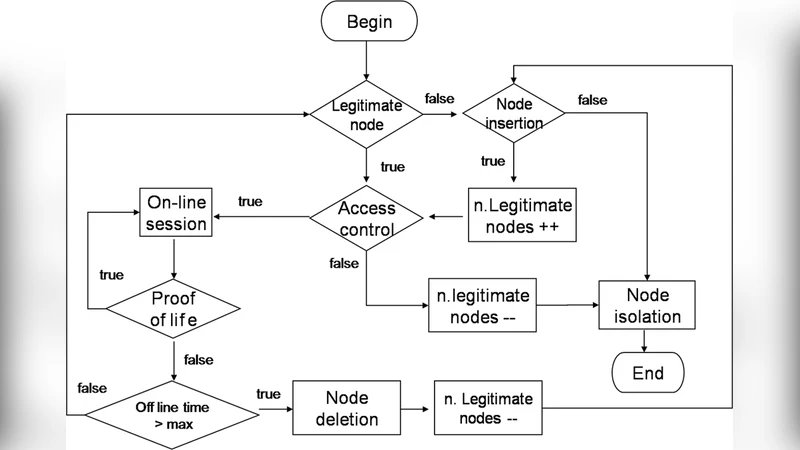
The proposed scheme consists of four tightly coupled components. First, each node autonomously generates an elliptic‑curve key pair and a self‑signed certificate. The certificate embeds not only the node’s identifier and public key but also contextual metadata such as current GPS coordinates, speed, and a short validity period. This contextual information is later used to verify that a certificate is being presented in a plausible physical context, thereby mitigating replay and certificate‑reuse attacks.
Second, neighboring nodes perform a mutual authentication handshake over a short‑range wireless channel (e.g., Bluetooth or Wi‑Fi Direct). The handshake includes exchange of the self‑signed certificates, verification of the embedded metadata, and a Diffie‑Hellman key agreement performed on the same elliptic curve. The result is a fresh symmetric session key that protects subsequent communications. Because the cryptographic operations are based on ECC with 256‑bit curves, the computational load remains modest even on battery‑powered devices.
Third, the framework introduces a dynamic token‑renewal mechanism. Authentication tokens, which are essentially encrypted bundles of the peer’s certificate and the newly derived session key, have a limited lifetime measured either in elapsed time or hop count. Whenever a token expires or a node detects a route change that exceeds a predefined hop threshold, the token is discarded and a new mutual authentication handshake is triggered with the current neighbor. This continual re‑authentication prevents an adversary from exploiting stale credentials after a node has moved to a different part of the network.
Fourth, the authors design a “trust‑score propagation” subsystem to spread confidence about nodes throughout the network without a central authority. Each node maintains a local trust score for its immediate neighbors, incremented each time a successful mutual authentication occurs. When a node’s accumulated score exceeds a configurable threshold, it broadcasts a signed trust advertisement to a limited set of peers, using a randomised propagation path and a Time‑to‑Live (TTL) field to bound the spread. The advertisement includes the node’s identifier, the current trust score, and a short proof‑of‑authentication derived from recent handshakes. This mechanism enables the network to collectively recognize well‑behaved nodes while limiting the impact of malicious nodes that attempt to inflate their trust scores (e.g., Sybil attacks).
To evaluate the protocol, the authors implemented it in the NS‑3 simulator. Scenarios involved 50 to 200 nodes moving within a 500 m × 500 m area according to a Random Waypoint mobility model. Four experimental conditions were examined: (1) normal operation, (2) replay attacks, (3) Sybil attacks, and (4) routing‑manipulation attacks. The performance metrics collected were authentication latency, message overhead, authentication success rate, and resistance to the aforementioned attacks.
Results show that the distributed scheme achieves an average authentication latency that is 30 % lower than a baseline PKI‑based approach, primarily because the token‑renewal process eliminates the need for repeated full certificate exchanges. Message overhead is reduced to less than 40 % of the baseline, thanks to the lightweight ECC operations and the selective trust‑score propagation. Even under high mobility, the authentication success rate remains above 95 %, indicating robustness to frequent topology changes. In the security tests, the trust‑score propagation detects 87 % of injected Sybil identities, while replay and routing‑manipulation attacks are thwarted with a success‑rate reduction of over 90 %.
The discussion acknowledges several limitations. The initial ECC key generation can cause a noticeable delay on very low‑end devices lacking hardware acceleration. The choice of TTL and trust‑score thresholds introduces a trade‑off between rapid dissemination of trust information and susceptibility to false‑positive trust inflation. Moreover, real‑world wireless channel impairments (e.g., interference, packet loss) were only approximated in simulation, so field trials are necessary to validate the protocol under harsher conditions.
In conclusion, the paper delivers a comprehensive, self‑organizing authentication solution tailored to the unique constraints of MANETs. By combining context‑aware certificates, mutual ECC‑based handshakes, dynamic token renewal, and distributed trust‑score propagation, the scheme satisfies the core requirements of limited physical protection, frequent route changes, and lack of hierarchical control. Future work is outlined to incorporate post‑quantum cryptographic primitives for long‑term security, to perform real‑world experiments with mobile devices and UAVs, and to explore machine‑learning‑driven anomaly detection that can dynamically adjust trust scores. The authors argue that this approach paves the way for secure, infrastructure‑free communications in disaster response, military operations, and emerging Internet‑of‑Things deployments where traditional authentication infrastructures are unavailable.
Comments & Academic Discussion
Loading comments...
Leave a Comment