Peer-to-Peer Secure Multi-Party Numerical Computation Facing Malicious Adversaries
We propose an efficient framework for enabling secure multi-party numerical computations in a Peer-to-Peer network. This problem arises in a range of applications such as collaborative filtering, distributed computation of trust and reputation, monitoring and other tasks, where the computing nodes is expected to preserve the privacy of their inputs while performing a joint computation of a certain function. Although there is a rich literature in the field of distributed systems security concerning secure multi-party computation, in practice it is hard to deploy those methods in very large scale Peer-to-Peer networks. In this work, we try to bridge the gap between theoretical algorithms in the security domain, and a practical Peer-to-Peer deployment. We consider two security models. The first is the semi-honest model where peers correctly follow the protocol, but try to reveal private information. We provide three possible schemes for secure multi-party numerical computation for this model and identify a single light-weight scheme which outperforms the others. Using extensive simulation results over real Internet topologies, we demonstrate that our scheme is scalable to very large networks, with up to millions of nodes. The second model we consider is the malicious peers model, where peers can behave arbitrarily, deliberately trying to affect the results of the computation as well as compromising the privacy of other peers. For this model we provide a fourth scheme to defend the execution of the computation against the malicious peers. The proposed scheme has a higher complexity relative to the semi-honest model. Overall, we provide the Peer-to-Peer network designer a set of tools to choose from, based on the desired level of security.
💡 Research Summary
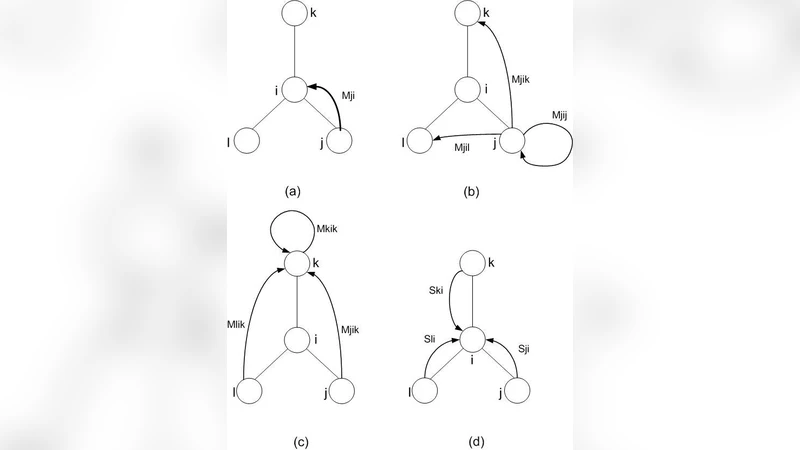
The paper addresses the problem of performing secure multi‑party numerical computations over large‑scale peer‑to‑peer (P2P) networks. Many distributed algorithms—such as belief propagation, expectation‑maximization, power iteration, gradient descent, and collaborative filtering—operate by repeatedly computing weighted sums of scalar messages received from a node’s neighbors. The authors formalize this as a generic iterative computation where each node i, at round r, receives values m_{r‑1}^{j→i} from its neighbors j∈N_i, multiplies each by a known weight a_{ij}, and computes a new weighted sum X_i = Σ_{j∈N_i} a_{ij}·m_{r‑1}^{j→i}. The goal is to preserve the privacy of each node’s input while guaranteeing that the final output of every honest node is correct.
Two adversarial models are considered. In the semi‑honest (honest‑but‑curious) model, corrupted nodes follow the protocol faithfully but may later inspect all internal states and transcripts to infer private data. In the malicious model, adversaries may deviate arbitrarily, sending malformed messages or manipulating intermediate values to bias the final result or extract secrets.
For the semi‑honest setting the authors evaluate three candidate constructions:
-
Random Perturbation – each outgoing scalar is masked with zero‑mean noise. The noisy sums converge to the true sum as the number of neighbors grows. This method is computationally trivial but offers only weak privacy (it protects only against statistical inference) and supports only addition.
-
Shamir’s Secret Sharing (SSS) – each node splits its scalar into n shares using a degree‑k‑1 polynomial and distributes them to its neighbors. Weighted sums are computed by locally aggregating shares and then reconstructing the result via polynomial interpolation. While information‑theoretically secure, the approach incurs O(k·|N_i|) communication and O(k³) local computation per round, which becomes prohibitive for large neighborhoods.
-
Additively Homomorphic Encryption (Paillier) – each node encrypts its scalar under a globally known public key. Because Paillier supports homomorphic addition and scalar multiplication, a node can multiply encrypted messages by public weights and aggregate them directly in ciphertext space. Only the final result needs decryption. Although encryption/decryption require modular exponentiations, the per‑round overhead scales linearly with the number of neighbors and remains modest.
Extensive simulations on real Internet AS‑level topologies (up to one million nodes and hundreds of millions of edges) show that the Paillier‑based scheme dominates both in latency and bandwidth consumption, while preserving exact arithmetic (no approximation error). Consequently, the authors select it as the “light‑weight” solution for the semi‑honest model.
For the malicious adversary model, the authors augment the homomorphic scheme with several defenses:
-
GMW Compiler with Zero‑Knowledge Proofs (ZKPs) – each elementary operation (encryption, homomorphic addition, scalar multiplication, decryption) is accompanied by a ZKP that the party performed it correctly without revealing secret data. This transforms a semi‑honest protocol into a malicious‑secure one.
-
Local Malicious Bound d_i – instead of a global bound on the total number of corrupted nodes, the protocol assumes that at most d_i neighbors of any node i are malicious. If this bound is exceeded, the security guarantees no longer hold, which is a realistic assumption for many P2P systems where adversaries are geographically or topologically constrained.
-
Share Verification – the protocol combines secret sharing with consistency checks. Nodes broadcast commitments to their shares and verify that the aggregated ciphertexts correspond to the committed values, detecting any tampering.
-
Multi‑Signature and Public Verification – every message is signed using a threshold or aggregate signature scheme, allowing receivers to quickly detect forged or altered messages.
These extensions increase computational and communication costs by roughly a factor of three to five compared with the semi‑honest baseline, but they provide strong guarantees: even if a fraction of neighbors behave arbitrarily, the final weighted sums remain correct and private inputs stay hidden.
The paper validates the framework with a concrete application: collaborative filtering using the Jacobi algorithm. In this scenario each peer holds a subset of user‑item ratings and iteratively updates a global matrix by exchanging weighted sums with neighbors. By applying the homomorphic encryption layer, individual ratings are never exposed, yet the algorithm converges to the same recommendation quality as the non‑secure version.
Overall contributions:
- Formalization of a broad class of distributed numerical methods as repeated weighted‑sum computations suitable for secure augmentation.
- Comparative analysis of three semi‑honest constructions, with a clear empirical demonstration that Paillier‑based homomorphic encryption offers the best trade‑off between security and scalability.
- Design of a malicious‑secure extension using ZKPs, local adversarial bounds, and share verification, achieving practical performance even on million‑node networks.
- Large‑scale simulation on realistic Internet topologies, showing sub‑minute convergence times for the semi‑honest scheme and acceptable overhead for the malicious‑secure variant.
- A concrete implementation for privacy‑preserving collaborative filtering, illustrating the practicality of the approach.
The work bridges the gap between theoretical SMPC and real‑world P2P deployments, offering network designers a toolbox of protocols that can be selected according to the desired security level and performance constraints. Future directions suggested include extending the framework to support non‑linear operations, handling dynamic churn, and integrating blockchain‑based identity and reputation mechanisms to further strengthen trust in open P2P environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment