Soft Computing - A step towards building Secure Cognitive WLAN
Wireless Networks rendering varied services has not only become the order of the day but the demand of a large pool of customers as well. Thus, security of wireless networks has become a very essential design criterion. This paper describes our research work focused towards creating secure cognitive wireless local area networks using soft computing approaches. The present dense Wireless Local Area Networks (WLAN) pose a huge threat to network integrity and are vulnerable to attacks. In this paper we propose a secure Cognitive Framework Architecture (CFA). The Cognitive Security Manager (CSM) is the heart of CFA. The CSM incorporates access control using Physical Architecture Description Layer (PADL) and analyzes the operational matrices of the terminals using multi layer neural networks, acting accordingly to identify authorized access and unauthorized usage patterns.
💡 Research Summary
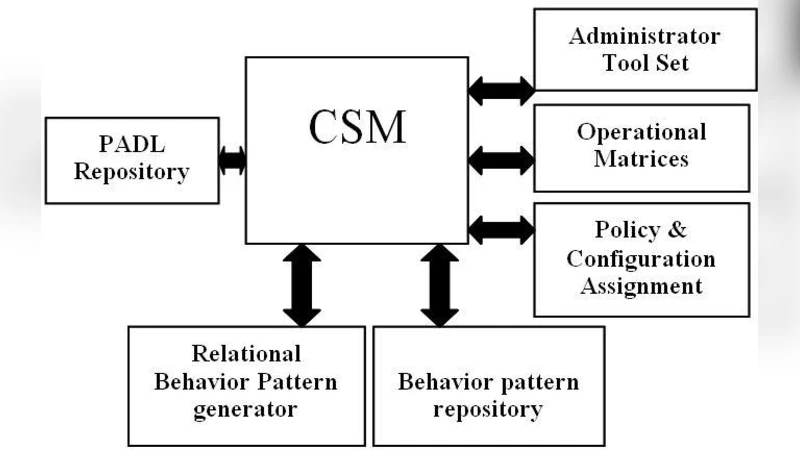
The paper addresses the growing security concerns of dense Wireless Local Area Networks (WLANs) by proposing a Cognitive Framework Architecture (CFA) that integrates soft‑computing techniques with cognitive networking concepts. At the heart of the CFA lies the Cognitive Security Manager (CSM), which performs two main functions: (1) access control based on a Physical Architecture Description Layer (PADL) and (2) behavior‑pattern analysis using multilayer neural networks.
PADL is defined as a collection of physical‑layer and radio‑layer attributes unique to each terminal. By storing PADL values in a repository divided into “authorized” and “unauthorized” sections, the CSM can uniquely identify devices, detect new arrivals, and move devices between sections when misbehavior is observed.
Behavior analysis proceeds in two stages. First, a simple multilayer perceptron (MLP) with a sigmoid activation function receives the current node activity vector together with the node’s operational matrix (OM) and produces a current behavior pattern (BH). Second, a Multilayer Feed‑Forward Neural Network (MFNN) with two hidden layers, also trained by back‑propagation, compares BH with historical patterns (TBH) stored in a Behavior Pattern Repository. If the deviation exceeds a threshold θ (set by an administrative tool), the node is classified as unauthorized; its PADL and related data are removed from the authorized repository, and network services are denied.
The CSM workflow is as follows: a node enters the WLAN, its PADL is captured, and the CSM classifies it as (i) new, (ii) authorized, or (iii) unauthorized. For new nodes, the administrative tool supplies a conservative operational matrix and registers the PADL. For authorized nodes, the CSM retrieves the stored OM, generates BH, runs the MFNN, and decides whether to maintain normal service or to block the node. Unauthorized nodes are blocked outright.
To evaluate the approach, the authors built a testbed with 60 client nodes and six access points, deploying the CSM on a quad‑core server with 4 GB RAM. They varied neural‑network parameters such as the number of input neurons, learning rate, and iteration count, measuring the learning error rate. The results show that increasing the input‑layer size and selecting an appropriate learning rate (approximately 0.01–0.05) reduces the error, indicating effective training. However, the evaluation focuses solely on learning‑error metrics; it does not provide detection accuracy, false‑positive/negative rates, latency measurements, or a comparison with existing security mechanisms like WPA3.
Strengths of the paper include the novel use of PADL for device fingerprinting, the integration of cognitive concepts into WLAN security, and a clear algorithmic description of the CSM’s decision process. Weaknesses involve the lack of detail on how PADL is collected and protected, insufficient discussion of privacy implications, limited experimental scale (only 60 nodes), and the absence of quantitative security performance results. Moreover, the reliance on a static threshold set by an administrator may limit adaptability in dynamic environments, and the policy of completely deleting a node’s data upon a single detection could lead to denial‑of‑service issues if false alarms occur.
In summary, the paper proposes an interesting architecture that combines soft‑computing (multilayer neural networks) with a physical‑layer identification scheme to enhance WLAN security. While the conceptual framework is sound and the implementation details are reasonably described, further work is needed to validate the approach in larger, real‑world deployments, to address privacy and scalability concerns, and to benchmark its security effectiveness against established standards.
Comments & Academic Discussion
Loading comments...
Leave a Comment