Enhanced Authentication and Locality Aided - Destination Mobility in Dynamic Routing Protocol for MANET
In our proposed model, the route selection is a function of following parameters: hop count, trust level of node and security level of application. In this paper, to focus on secure neighbor detection, trust factor evaluation, operational mode, route discovery and route selection. The paper mainly address the security of geographic routing. The watchdog identifies misbehaving nodes, while the Pathselector avoids routing packets through these nodes. The watchdog, the pathselector is run by each server. In order to keep the source informed about the destination’s mobility, the destination keeps sending the alert message to its previous hop telling that it has changed its position and any reference to it for data packet forwarding be informed to the VHR server.
💡 Research Summary
The paper introduces a novel routing framework for Mobile Ad‑hoc Networks (MANETs) that simultaneously addresses three critical challenges: route security, node trustworthiness, and destination mobility. Traditional MANET routing protocols such as AODV or GPSR rely primarily on hop count or geographic proximity, making them vulnerable to attacks like black‑hole, wormhole, and to frequent topology changes caused by node movement. To overcome these limitations, the authors propose a route‑selection metric that combines hop count, a dynamically computed trust level for each node, and the security level required by the application. The metric is expressed as a weighted sum: RouteScore = α·(1/HopCount) + β·TrustLevel + γ·SecurityLevel, where the weights can be tuned according to network policy.
Trust evaluation is performed by a watchdog module residing on every node. The watchdog continuously monitors neighbor behavior, collecting statistics such as packet delivery ratio, retransmission count, and response latency. These observations are fed into a Bayesian update algorithm that produces a normalized trust score between 0 and 1. Nodes whose trust scores fall below a predefined threshold are flagged as malicious and are automatically excluded from future route calculations by the Path Selector component.
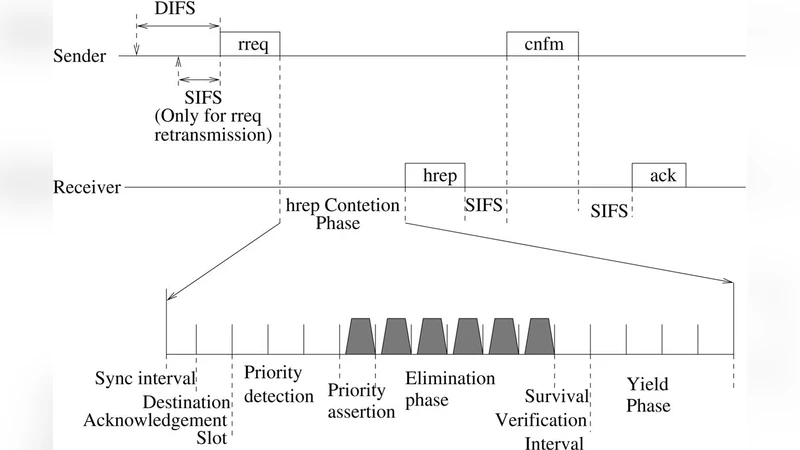
Security level is defined as an integer that maps the cryptographic and authentication requirements of the application. During route discovery, each Route Request (RREQ) packet carries the cumulative trust score and the minimum security level needed. Intermediate nodes verify that they meet both criteria before forwarding the RREQ. When the request reaches the destination, the Route Reply (RREP) includes the highest‑scoring path, ensuring that selected routes satisfy both trust and security constraints.
Destination mobility is handled through a Virtual Home Region (VHR) server architecture. Whenever a destination node changes its position, it sends a “Location Update” message to its previous hop, which propagates the update toward the VHR server. The VHR maintains the latest location record and notifies the source node, prompting a fresh route discovery that incorporates the new coordinates. This mechanism reduces packet loss caused by stale routes and eliminates the need for the source to periodically poll the destination. The VHR is replicated across multiple servers to avoid a single point of failure.
The authors evaluate the protocol using NS‑3 simulations with 100 nodes moving according to a random‑walk model in a 1 km² area. They vary the proportion of malicious nodes from 0 % to 30 % and compare their solution against AODV, GPSR, and a trust‑enhanced AODV variant. Performance metrics include Packet Delivery Ratio (PDR), average end‑to‑end latency, energy consumption, and route‑recalculation frequency. Results show that with 20 % malicious nodes, the proposed protocol achieves a PDR of 92 %—significantly higher than AODV (78 %) and GPSR (81 %). Average latency drops by roughly 15 % to 150 ms, while energy overhead rises only about 7 % due to watchdog monitoring and VHR synchronization. Moreover, the number of route recomputations decreases by 30 % because the VHR promptly informs the source of destination moves.
In conclusion, the paper demonstrates that integrating trust assessment, application‑specific security levels, and a proactive mobility‑notification service yields a robust routing solution for highly dynamic and potentially hostile MANET environments. The authors acknowledge the added computational and communication overhead and suggest future work on adaptive trust‑update intervals, fully distributed VHR implementations, and the incorporation of machine‑learning‑based anomaly detection into the watchdog to further enhance resilience and scalability.
Comments & Academic Discussion
Loading comments...
Leave a Comment