Security Policy Enforcement Through Refinement Process
In the area of networks, a common method to enforce a security policy expressed in a high-level language is based on an ad-hoc and manual rewriting process. We argue that it is possible to build a formal link between concrete and abstract terms, which can be dynamically computed from the environment data. In order to progressively introduce configuration data and then simplify the proof obligations, we use the B refinement process. We present a case study modeling a network monitor. This program, described by refinement following the layers of the TCP/IP suite protocol, has to warn for all observed events which do not respect the security policy. To design this model, we use the event-B method because it is suitable for modeling network concepts. This work has been done within the framework of the POTESTAT project, based on the research of network testing methods from a high-level security policy.
💡 Research Summary
The paper addresses the longstanding challenge of translating high‑level security policies into concrete network configurations. Traditional approaches rely on ad‑hoc, manual rewriting of policy specifications, which is error‑prone and difficult to maintain as networks evolve. To overcome these limitations, the authors propose a formally grounded methodology that links abstract policy terms with concrete network events through a series of B‑refinement steps, implemented using the Event‑B formalism.
At the highest abstraction level, a security policy is expressed as a set of simple allow/deny rules together with an abstract “violation event” that should be raised whenever a rule is broken. This abstract model contains only the essential logical structure of the policy and a minimal set of invariants guaranteeing internal consistency.
The refinement process then proceeds layer by layer through the TCP/IP stack. For each protocol layer—link, internet, transport, and application—the model introduces concrete variables representing header fields (e.g., MAC addresses, IP addresses, ports, flags) and enriches the invariants to relate these fields to the abstract policy. For instance, at the transport layer the model asserts that a packet’s source and destination ports belong to the set of ports permitted by the policy; at the internet layer it checks that source and destination IP addresses are within authorized sub‑nets. By the final refinement, the abstract violation event is concretized into a predicate over actual packet attributes, enabling the system to detect policy breaches in real time.
A key innovation is the “progressive introduction of configuration data.” Rather than hard‑coding network parameters, the refined model treats them as external data that can be loaded dynamically from the environment (e.g., current routing tables, address allocations, firewall rule sets). This design means that when the network topology or the policy itself changes, only the configuration data need be updated; the underlying formal model and its proofs remain valid.
Proof obligations generated at each refinement step are discharged automatically using Event‑B tool support (Rodin, ProB). Because each refinement adds only a bounded amount of new structure, the proof effort scales linearly, and the overall correctness of the model—i.e., that every concrete event respects the abstract policy—is guaranteed by construction.
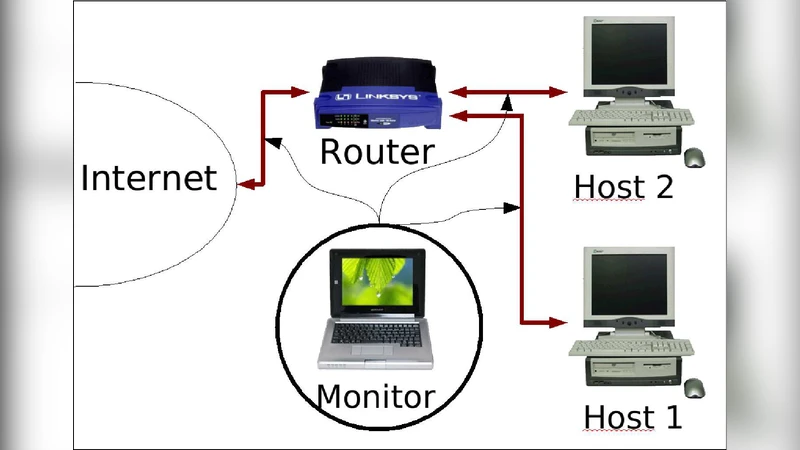
The authors validate their approach with a case study: a network monitor that captures live traffic via libpcap, maps each packet to an Event‑B event, and triggers a warning whenever the refined violation predicate evaluates to true. The monitor is built as a Java wrapper around the Event‑B engine, demonstrating that the formal model can be integrated into a practical runtime system. Experiments show that policy updates require only a reload of the configuration file; no recompilation or re‑verification of the model is necessary, thereby achieving true runtime adaptability.
In summary, the paper makes four substantive contributions. First, it establishes a rigorous, refinement‑based bridge between high‑level security policies and low‑level network events. Second, it introduces a dynamic data‑binding mechanism that enables automatic policy enforcement without manual code changes. Third, it showcases the practical viability of Event‑B and B‑refinement for network‑centric security engineering, reducing proof obligations to manageable, automatically solvable tasks. Fourth, by modeling the TCP/IP stack layer by layer, the work provides a reusable framework that can be extended to other protocols or security domains. The results suggest that formal refinement can move from academic exercise to a concrete tool for secure network management in real‑world deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment