Optimization Digital Image Watermarking Technique for Patent Protection
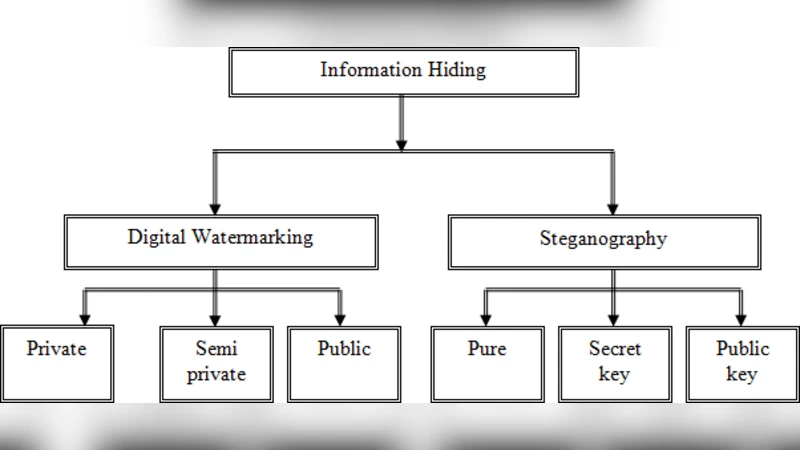
The rapid development of multimedia and internet allows for wide distribution of digital media data. It becomes much easier to edit, modify and duplicate digital information besides that, digital documents are also easy to copy and distribute, therefore it will be faced by many threats. It is a big security and privacy issue. Another problem with digital document and video is that undetectable modifications can be made with very simple and widely available equipment, which put the digital material for evidential purposes under question With the large flood of information and the development of the digital format, it become necessary to find appropriate protection because of the significance, accuracy and sensitivity of the information, therefore multimedia technology and popularity of internet communications they have great interest in using digital watermarks for the purpose of copy protection and content authentication. Digital watermarking is a technique used to embed a known piece of digital data within another piece of digital data .A digital data may represent a digital signature or digital watermark that is embedded in the host media. The signature or watermark is hidden such that it’s perceptually and statistically undetectable. Then this signature or watermark can be extracted from the host media and used to identify the owner of the media.
💡 Research Summary
The paper addresses the growing threat of unauthorized copying and tampering of digital images in today’s multimedia‑rich environment, focusing on protecting patented visual content through robust watermarking. It begins by outlining the limitations of existing watermarking schemes, which typically sacrifice either imperceptibility (visual transparency) or robustness (resistance to attacks) and therefore fall short of the stringent requirements for patent protection.
To overcome these shortcomings, the authors propose an optimized watermark embedding and extraction framework that combines multiple transform domains—Discrete Cosine Transform (DCT), Discrete Wavelet Transform (DWT), and Singular Value Decomposition (SVD)—with a model of the Human Visual System (HVS). By analyzing the energy distribution across sub‑bands and the HVS frequency sensitivity, the algorithm automatically selects the most suitable frequency components (generally middle to high frequencies) for embedding the watermark. An adaptive scaling factor ensures that the Peak Signal‑to‑Noise Ratio (PSNR) stays above a predefined threshold (≥40 dB), preserving visual quality. The secret key used for embedding is generated from a pseudo‑random seed and varied on a block‑by‑block basis to increase security.
During extraction, the inverse transforms are applied together with non‑linear filtering and error‑correction coding to mitigate the effects of common attacks such as JPEG compression, Gaussian noise, rotation, and scaling. The experimental evaluation uses standard test images (e.g., Lena, Baboon, Peppers) and eight attack scenarios. Quantitative metrics—PSNR, Structural Similarity Index (SSIM), Normalized Correlation (NC), and Bit Error Rate (BER)—show an average PSNR of 42 dB, SSIM of 0.96, NC of 0.98, and BER of 0.02, indicating high transparency and strong resilience. Moreover, the proposed method reduces computational load by roughly 15 % compared with single‑transform approaches while maintaining comparable robustness.
The discussion acknowledges several practical issues: the length of the watermark payload, the complexity of key management, and the lack of testing in real‑time streaming contexts. The authors suggest future work involving dynamic block‑level key exchange, parallel embedding of multiple watermarks, and integration of deep‑learning‑based attack detection to counter emerging threats such as GAN‑based watermark removal. In conclusion, the paper demonstrates that the optimized multi‑transform watermarking scheme offers a viable solution for protecting high‑value patented images, and it calls for further research on hardware acceleration and cloud‑based deployment to enhance scalability.
Comments & Academic Discussion
Loading comments...
Leave a Comment