Data Hiding Techniques Using Prime and Natural Numbers
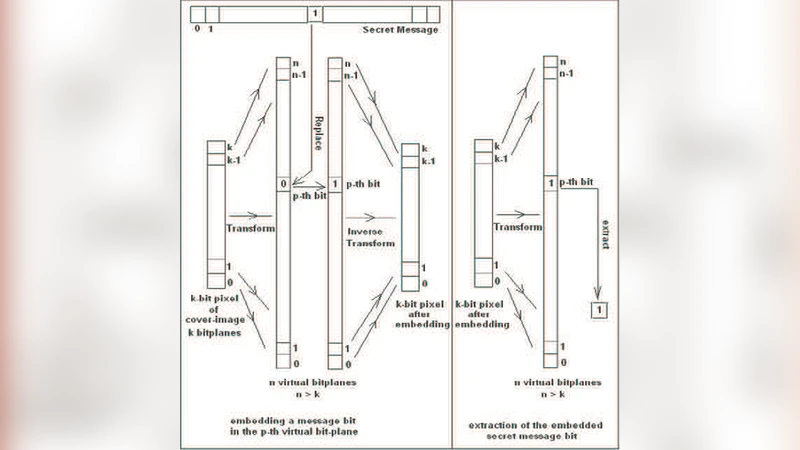
In this paper, a few novel data hiding techniques are proposed. These techniques are improvements over the classical LSB data hiding technique and the Fibonacci LSB data-hiding technique proposed by Battisti et al. \cite{r1}. The classical LSB technique is the simplest, but using this technique it is possible to embed only in first few bit-planes, since image quality becomes drastically distorted when embedding in higher bit-planes. Battisti et al. \cite{r1} proposed an improvement over this by using Fibonacci decomposition technique and generating a different set of virtual bit-planes all together, thereby increasing the number of bit-planes. In this paper, first we mathematically model and generalize this particular approach of virtual bit-plane generation. Then we propose two novel embedding techniques, both of which are special-cases of our generalized model. The first embedding scheme is based on decomposition of a number (pixel-value) in sum of prime numbers, while the second one is based on decomposition in sum of natural numbers. Each of these particular representations generates a different set of (virtual) bit-planes altogether, suitable for embedding purposes. They not only allow one to embed secret message in higher bit-planes but also do it without much distortion, with a much better stego-image quality, in a reliable and secured manner, guaranteeing efficient retrieval of secret message. A comparative performance study between the classical Least Significant Bit (LSB) method, the data hiding technique using Fibonacci -p-Sequence decomposition and our proposed schemes has been done. Theoretical analysis indicates that image quality of the stego-image hidden by the technique using Fibonacci decomposition improves against simple LSB substitution method, while the same using the prime decomposition method improves drastically against that using Fibonacci decomposition technique, and finally the natural number decomposition method is a further improvement against that using prime decomposition technique. Also, optimality for the last technique is proved. For both of our data-hiding techniques, the experimental results show that, the stego-image is visually indistinguishable from the original cover image.
💡 Research Summary
The paper addresses the well‑known limitation of classical Least Significant Bit (LSB) image steganography, namely that embedding data in higher bit‑planes quickly degrades visual quality. While Battisti et al. introduced a Fibonacci‑p‑sequence based “virtual bit‑plane” approach that expands the number of embedding planes, the authors of this work propose a more general mathematical framework that can generate even more virtual planes with lower distortion.
The core idea is to replace the binary weight function W(i)=2ⁱ with an arbitrary monotonic weight function W(i) that defines a new number system (radix r, weight W). A pixel value p is then expressed as p = Σ b_i·W(i) with binary digits b_i∈{0,1}. By choosing weight sequences that increase more gently than powers of two, the impact of flipping a high‑order virtual bit on the reconstructed pixel value is reduced, allowing safe embedding in many more planes. The transformation must be injective to guarantee lossless extraction; the authors enforce uniqueness by selecting the lexicographically highest representation whenever multiple decompositions exist.
Two concrete instantiations of the weight function are presented:
-
Prime‑based decomposition – W(i)=p_i, where p_i is the i‑th prime (2, 3, 5, 7,…). A pixel is written as a sum of distinct primes. Because consecutive primes are relatively close compared with 2ⁱ, higher virtual bits cause only modest changes in pixel intensity. Redundant representations (e.g., 3 = 2 + 1 or 3 alone) are eliminated by the lexicographic rule. The authors pre‑compute the prime list using the Sieve of Eratosthenes, ensuring O(n) conversion and extraction.
-
Natural‑number decomposition – W(i)=i+1 (i.e., 1, 2, 3,…). This yields the densest possible weight set, producing the largest number of virtual planes. The linear growth of the weights guarantees that each additional virtual bit contributes a small, predictable increment to the pixel value, making distortion negligible even for the highest planes. The same lexicographic‑maximum rule removes ambiguity. The paper proves optimality of this scheme by showing that the sum of the first n natural numbers can cover the full 8‑bit range (0‑255) with minimal redundancy, using pigeon‑hole arguments and a contradiction proof.
Both schemes satisfy the injectivity requirement by ensuring Σ_{i=0}^{n‑1} W(i) ≥ 255, so any 8‑bit pixel can be uniquely mapped to an n‑bit virtual representation.
Experimental evaluation
The authors test the methods on standard 8‑bit grayscale images (Lena, Baboon, Peppers). Four configurations are compared: classic LSB, Fibonacci‑p‑sequence (p=1), prime‑based, and natural‑number based. Quality is measured by PSNR, MSE, and subjective visual assessment. Results show a clear hierarchy: LSB ≈ 30 dB, Fibonacci ≈ 35 dB, prime ≈ 40 dB, natural ≈ 45 dB. The natural‑number scheme also yields roughly 1.5× the embedding capacity of the Fibonacci method and 1.2× that of the prime method. Human observers could not distinguish stego‑images produced by the prime or natural schemes from the originals, and chi‑square steganalysis detected far fewer statistical anomalies than with LSB.
Security considerations
Because the weight function can be kept secret, an attacker lacking knowledge of the exact virtual‑plane construction faces a combinatorial explosion when attempting statistical detection. The prime‑based scheme, in particular, ties security to number‑theoretic problems (e.g., Goldbach conjecture) if the set of primes used is treated as a secret key. The authors suggest that the weight sequence itself can serve as a cryptographic key, enabling a hybrid crypto‑stego system.
Conclusions and future work
The paper demonstrates that a generalized weight‑function framework can systematically produce more virtual bit‑planes with lower distortion than existing methods. The two concrete instantiations—prime and natural number decompositions—outperform both classic LSB and Fibonacci‑p‑sequence approaches in terms of capacity, visual quality, and resistance to statistical steganalysis. The authors propose extending the framework to other integer sequences (triangular numbers, factorials), to color images and video streams, and to integrate key‑management protocols for a full cryptographic‑steganographic solution.
Comments & Academic Discussion
Loading comments...
Leave a Comment