Secure sum computation of private data inputs is an important component of Secure Multi party Computation (SMC).In this paper we provide a protocol to compute the sum of individual data inputs with zero probability of data leakage. In our proposed protocol we break input of each party into number of segments and change the arrangement of the parties such that in each round of the computation the neighbors are changed. In this protocol it becomes impossible for semi honest parties to know the private data of some other party.
Deep Dive into Changing Neighbors k Secure Sum Protocol for Secure Multi Party Computation.
Secure sum computation of private data inputs is an important component of Secure Multi party Computation (SMC).In this paper we provide a protocol to compute the sum of individual data inputs with zero probability of data leakage. In our proposed protocol we break input of each party into number of segments and change the arrangement of the parties such that in each round of the computation the neighbors are changed. In this protocol it becomes impossible for semi honest parties to know the private data of some other party.
In today's world of information technology opportunities exist for joint computation requiring privacy of the inputs. These computations occur between parties which may not have trust in one another. In literature this subject is called Secure Multi-party Computation (SMC). It is aimed at privacy of individual inputs and the correctness of the result. Formally in SMC the parties P 1, P 2 ,…, P n want to compute some common function f(x 1 , x 2, …, x n ) of inputs x 1 , x 2, …,x n such a party can know only its own input x i and the value of the function f . The SMC problems use two computation models; ideal model and real model. In ideal model there exists a Trusted Third Party (TTP) which accepts inputs from all the parties, evaluates the common function. In real model the parties agree on some protocol which allows all the parties to evaluate the function. For example if two banks cooperatively want to know details about some customer but no bank is willing to disclose the details of the customer to other bank due to privacy of customer or policy of the bank. In such situations the SMC solutions are important. The best example of SMC is the secure sum computation where all the cooperating parties want to compute the sum of their individual data inputs while preserving confidentiality of inputs [10]. The secure sum protocol proposed by Clifton et al. in [10] uses randomization method for computing the sum. In this protocol two adjacent parties to a middle party can collude maliciously to know the data of a middle party. We proposed new protocols in [11] where the probability of data leakage has been reduced by segmenting the data block into a fixed number of segments. In this paper we propose a novel secure sum computation protocol with zero probability of data leakage. In this protocol we change the position of the parties so that the neighbors are changed in each round of the computation. This protocol which is an extension of our previous protocol we call as ck-Secure Sum Protocol.
The subject of SMC began in 1982 when Yao proposed his millionaire’s problem in which two millionaires wanted to know who was richer without revealing individual wealth to each other [1]. The solution provided was for semi honest. The semi honest parties follow the protocol but also try to know some other information. The concept was extended to multi-party computation [2]. Goldreich et al. also used circuit evaluation protocols for secure computation. Some real life applications of SMC emerged like Private Information Retrieval (PIR) [3,4], Privacypreserving data mining [5,6], Privacy-preserving geometric computation [7], Privacy-preserving scientific computation [8], Privacy-preserving statistical analysis [9] etc. An excellent review of SMC is provided by Du et al. in [12] where they developed a framework for SMC problem discovery and transformation of normal problem to SMC problem. A review of SMC problems with a focus on telecommunication systems is provided by Oleshchuk et al. in [13]. Anonymity enabled SMC was proposed by Mishra et al. in [14] where the identities of the parties are hidden for achieving privacy. In this paper the protocol is motivated by the work of Clifton et al. [10] where they proposed a toolkit of components for solution to SMC problems. They proposed that one of components of the toolkit for SMC is the secure sum computation. Secure sum computation is used in many distributed data mining applications where many geographically distributed sites compute sum of values from individual sites. The secure sum protocol proposed in [10] used random numbers for privacy of individual data inputs. In this scheme any two parties P i-1 and P i+1 can collude to know the secret data of party P i by performing only one computation. We proposed k-Secure Sum Protocol and Extended k-Secure Sum Protocol in [11] where the probability of data leakage is significantly reduced by breaking the data block of individual party in number of segments. The probability of data leakage decreases as the number of segments in a data block is increased. As per our survey no secure sum protocol is available in the literature with zero probability of data leakage when two neighbors collude. In this paper we proposed zero probability protocol for secure sum computation namely ck-Secure Sum Protocol in which neighbors are changed in each round of computation.
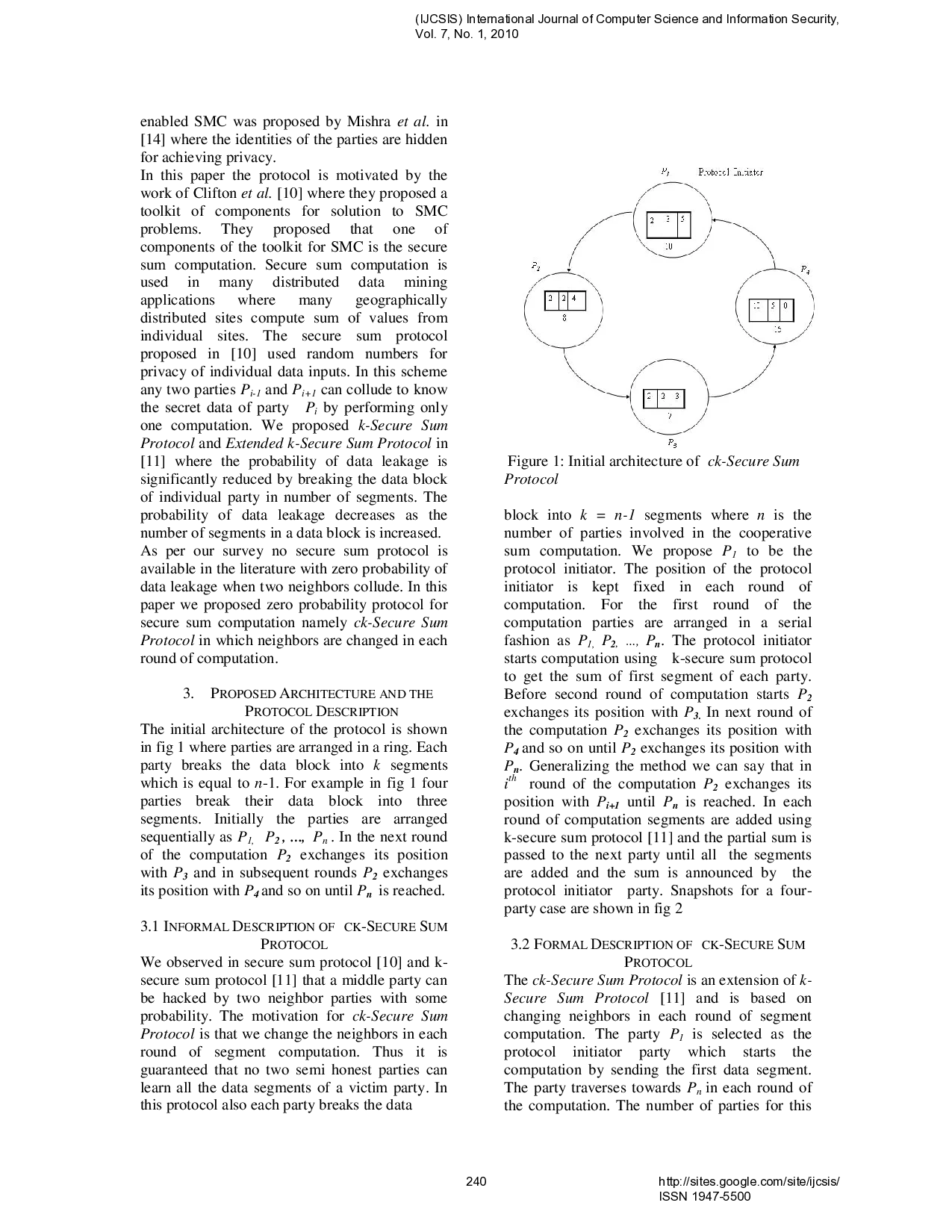
PROTOCOL DESCRIPTION The initial architecture of the protocol is shown in fig 1 where parties are arranged in a ring. Each party breaks the data block into k segments which is equal to n-1. For example in fig 1 four parties break their data block into three segments. Initially the parties are arranged sequentially as P 1, P 2 , …, P n . In the next round of the computation P 2 exchanges its position with P 3 and in subsequent rounds P 2 exchanges its position with P 4 and so on until P n is reached.
PROTOCOL We observed in secure sum protocol [10] and ksecure sum protocol [11] th
…(Full text truncated)…
This content is AI-processed based on ArXiv data.